A familiar pattern plays out in SaaS teams. Product adds analytics, marketing installs a retargeting tag, support embeds a chat widget, and engineering drops in a session recording tool to diagnose onboarding friction. Launch goes well. Then someone asks a simple question: which of these scripts sets cookies before consent, in which regions, and who can prove it?
Few teams can answer cleanly.
That is the core web cookie law problem. It rarely starts with lawyers reading statutes. It starts with code paths, third-party dependencies, and release velocity. A banner gets added late in the cycle, but the application has already been wired to load tracking libraries on first paint. At that point, compliance isn’t a copy change. It’s a rework of frontend loading, backend event routing, consent state management, and auditability.
For CTOs and product leaders, the lesson is straightforward. Cookie compliance sits in the same category as authentication, logging, and access control. If you treat it as a design concern, you can build clean controls. If you treat it as a post-launch patch, you inherit hidden risk and expensive retrofits.
Why Cookie Compliance Is an Architectural Problem
A lot of teams approach cookie work as a banner problem. They buy a consent popup, paste a script into the site shell, and assume the legal issue is contained.
It usually isn’t.
The failure mode is simple. The banner appears, but analytics, ad pixels, A/B testing tools, social embeds, or support widgets have already loaded. Some of them set cookies immediately. Others trigger network calls that amount to tracking even before the user has made a choice. The interface says “manage preferences”, but the architecture has already made the decision.
Third-party scripts create hidden liability
The modern web stack normalised this behaviour over years of growth in browser tracking. UC Berkeley Law’s Web Privacy Census found that cookies on the top 100 popular websites increased from 3,602 in 2009 to 5,675 in 2011, a 57% increase, with third-party cookies driving much of that expansion. By 2011, nearly every major website used cookies, making them part of core web infrastructure and a direct target for privacy regulation (UC Berkeley Law Web Privacy Census).
That history matters because many SaaS products still inherit assumptions from that era:
- Frontend-first loading: Scripts are bundled or injected globally.
- Vendor default settings: Tools assume immediate activation unless engineers disable it.
- Weak ownership: Marketing, product, and engineering each add trackers without a single approval path.
- No runtime control: There’s no dependable gate between user choice and script execution.
A privacy issue becomes an engineering issue the moment a non-essential script can execute before consent.
Practical rule: If a third-party script can run before your consent state is resolved, your banner is cosmetic.
Superficial fixes create technical debt
Late fixes are expensive because the problem spreads through the stack. You may need to refactor tag loading, split essential from non-essential services, redesign the consent model for authenticated users, and stop downstream event forwarding to vendors that never should have received data.
This also affects performance and maintainability. A consent-aware architecture often reduces unnecessary client-side script execution. The opposite is also true. Uncontrolled trackers increase page weight, complicate debugging, and make incidents harder to investigate.
What works and what doesn’t
What works:
- Central script governance
- Consent-aware loading paths
- Regional policy handling
- Records that show what the user chose and when
What doesn’t:
- One global “accept cookies” toggle with no categories
- Post-hoc disclosure after scripts already fired
- Relying on vendor claims without testing runtime behaviour
- Treating production as the first audit environment
Teams that build this properly don’t start with banner design. They start by mapping data flows and deciding which components are allowed to execute before consent exists.
Understanding Core Principles of Cookie Regulation
Web cookie law requirements often make more sense when you stop reading them as legal formalities and start reading them as system constraints.
A useful analogy is building access control for an internal platform. You wouldn’t grant every service broad permissions and then explain the overreach in a policy document. You’d scope access up front. Cookie regulation follows the same logic.
Consent means a real choice
The core question is whether the user had a meaningful opportunity to decide before non-essential tracking began. That’s the practical meaning of informed consent.
For engineering teams, this has direct consequences:
- The choice must happen before activation for consent-based regimes.
- The interface must explain what happens in language users can understand.
- The system must honour the result consistently across the application.
If the “reject” path is hidden, delayed, or weaker than the “accept” path, your implementation may look finished while still failing the principle behind the rule.
Purpose limitation works like least privilege
Purpose limitation is the privacy equivalent of least privilege. Data collected for one reason shouldn’t automatically be reused for another because the stack makes that convenient.
That means a product team should separate functions such as:
| Principle | Engineering interpretation |
|---|---|
| Consent | Don’t run non-essential tracking until the required user action exists |
| Transparency | Describe categories and purposes in plain language at the point of choice |
| Purpose limitation | Don’t reuse analytics or advertising identifiers for unrelated workflows |
| Data minimisation | Load fewer trackers, collect less data, keep less by default |
Many products drift at this point. A tool is introduced for analytics, then reused for audience building, attribution, or personalisation without a fresh review of legal basis, user disclosure, or vendor routing.
Transparency is a product design task
Transparency isn’t solved by a long policy page. Users need enough context at the moment they choose.
Good implementations tell users:
- Which categories exist
- Why each category is used
- Whether third parties are involved
- How to change the decision later
That’s also why the opt-in versus opt-out distinction matters significantly in practice. If your team is deciding which model applies in a market, Devisia’s explanation of opt-in and opt-out approaches is a useful operational reference.
Good privacy engineering translates legal principles into runtime controls, not paperwork.
Data minimisation is an architecture filter
Teams often over-focus on consent collection and under-focus on whether they need the tracker at all. Data minimisation asks a harder question: can the product achieve the goal with fewer cookies, fewer vendors, or more first-party control?
In practice, that can mean replacing broad third-party marketing tags with first-party analytics, limiting retention, or moving some telemetry into server-side systems where data can be governed more tightly.
The strongest compliance posture often starts by removing complexity, not documenting it.
Navigating the Global Web Cookie Law Environment
A SaaS team launches in the US, adds self-serve signups from Germany six months later, then discovers its analytics stack fires before any consent choice is stored. That is the point where cookie law stops being a policy problem and becomes a systems problem.
The legal rules differ by region, but the engineering question is consistent. Which scripts run, under what condition, for which user, and how do you prove it later?
The EU model requires prior control
In the EU, the operational baseline is simple to state and easy to violate. Non-essential cookies and similar tracking technologies generally need prior informed consent before they are set. A large-scale EU cookie law measurement study found that 49% of measured websites still installed profiling cookies before obtaining consent.
For engineering teams, that means:
- non-essential tags cannot load on page render
- consent choices must map to actual runtime behaviour
- withdrawal must stop future processing and prevent new writes
- records must show what the user saw and what the system did
Many teams fail here for predictable reasons. Tag managers are loaded globally. A product analytics SDK initializes in the app shell. A support widget drops identifiers before the consent layer finishes evaluating. None of that is fixed by updating the banner copy.
The US model creates branching logic
US state rules are less uniform, and that affects architecture. California and other states often focus more on notice, opt-out rights, sale or sharing definitions, and sensitive data handling than on the EU-style prior consent model for every non-essential cookie.
That does not make implementation easier. It creates more branching.
A region-aware system may need to support one behaviour for EU visitors, another for California residents, and a fallback for users whose location is uncertain. If product, web, and data teams do not share the same classification model, disclosures drift away from actual tag behaviour. That is the failure pattern that creates enforcement risk.
Common breakpoints include:
- adtech vendors labelled as analytics
- consent applied on marketing pages but not inside the app
- opt-out signals ignored by downstream event routing
- cookie choices stored in the browser while server-side enrichment keeps running
GDPR and CCPA CPRA compared in practice
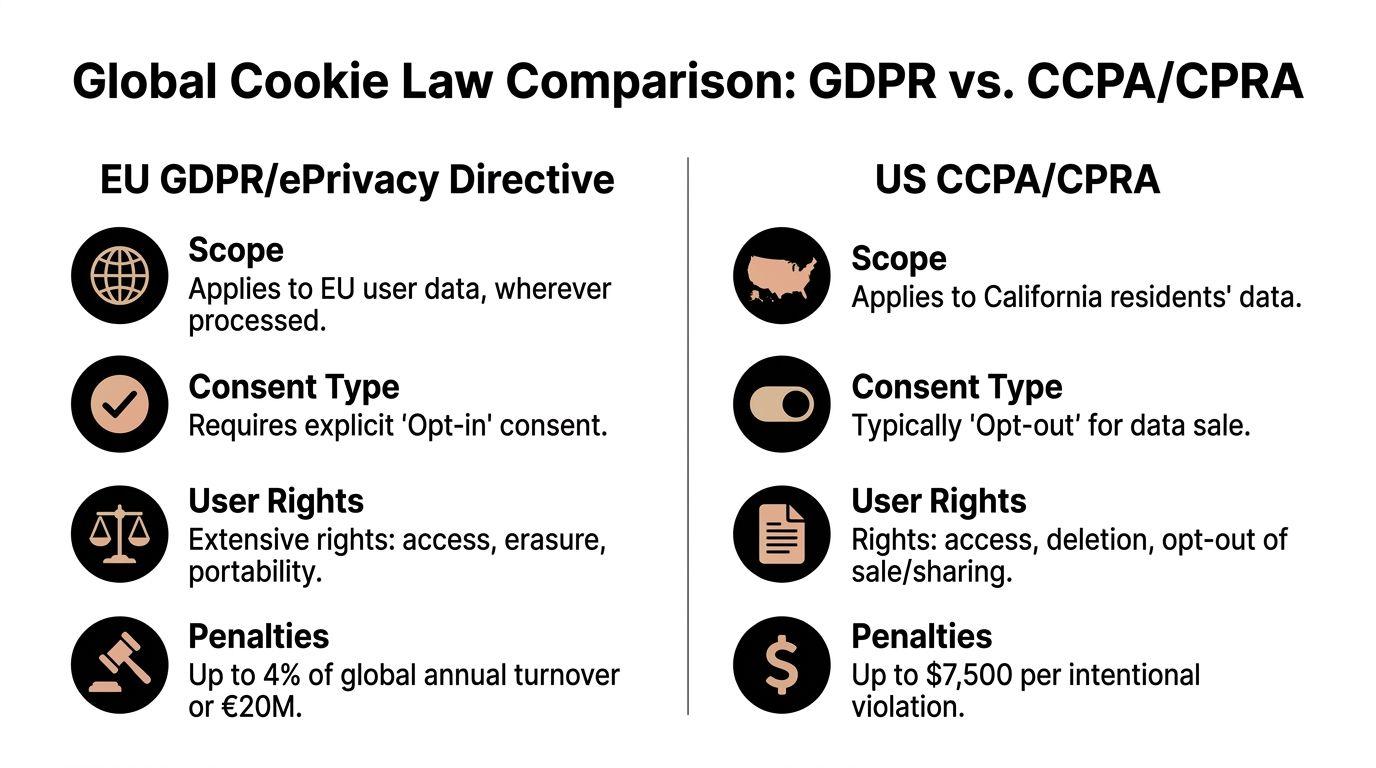
A CTO does not need a long legal summary. The useful question is what the product has to do differently.
| Compliance Area | GDPR / ePrivacy (EU) | CCPA / CPRA (California) |
|---|---|---|
| Default model | Prior consent for non-essential cookies and similar trackers | Notice, disclosure, and opt-out controls are often the main user-facing requirements |
| Timing | Choice must exist before activation | Behaviour, disclosures, and user rights handling must stay aligned |
| UX impact | Granular controls are often expected | Clear notice and accessible opt-out paths matter most |
| Engineering impact | Script blocking, conditional loading, consent-aware SDK initialisation | Accurate classification, suppression logic, and downstream data-use controls |
| Evidence | Consent logs and configuration history | Records of disclosures, user choices, and vendor handling |
Teams that need a user-facing explanation alongside the implementation work should keep the legal summary separate from the controls design. A privacy and cookies policy guide for SaaS teams helps with the policy side, but the harder work is still in the application architecture.
Choose your operating model early
The expensive mistake is waiting until international growth forces the issue. By then, the product usually assumes unrestricted client-side loading, shared vendor containers, and weak separation between necessary and optional tooling.
Three operating models show up in practice:
-
Global strict mode
Apply consent-first behaviour broadly. This reduces branching and lowers the chance that a geo failure causes unlawful tracking. The trade-off is lower data collection in regions where the law is more permissive. -
Region-aware mode
Apply different rules by jurisdiction. This can preserve measurement and marketing workflows in some markets, but it adds testing overhead, geo uncertainty, and more edge cases for travelling users, VPN traffic, and cached pages. -
Minimal tracking mode
Reduce reliance on third-party cookies and limit optional tracking. This usually gives the cleanest long-term compliance position, but product and growth teams may need to accept less granular attribution.
The right choice depends on your sales motion, traffic mix, and vendor stack. What matters is making the choice intentionally, then building the application around it.
Where implementation fails
Legal scope is rarely the hardest part. Runtime consistency is.
The biggest failures usually come from split ownership across teams. Marketing controls the tag manager. Product owns the app shell. Data engineering forwards events server-side. Nobody owns the end-to-end rule that says a user who declined marketing tracking should not trigger marketing identifiers anywhere in the stack.
Watch for these failure modes:
- Geo decisions that break under VPNs, proxies, or travel
- Consent state that frontend code can read but backend systems cannot
- Third-party scripts hardcoded outside the consent framework
- Separate consent behaviour across docs, app, billing, and support surfaces
- Vendor changes shipped without reclassification or legal review
The clean approach is product-wide. One taxonomy for purposes. One source of truth for consent state. One enforcement model across web, app, and downstream services. That is how regional legal differences stay manageable instead of turning into a permanent exception list.
Designing Compliant Consent and Policy Experiences
The banner is the part users see, so teams obsess over wording, button colour, and placement. That matters, but not for the reason many teams think. A good consent interface isn’t merely there to lower legal risk. It tells users whether your product handles data transparently.
If the first privacy interaction feels manipulative, users notice. Enterprise buyers notice too, especially during procurement and security review.
Dark patterns are a legal and product problem
Under FTC Act Section 5 and CPRA, cookie banners that use dark patterns, such as pre-selected checkboxes or making rejection materially harder than acceptance, are considered deceptive. A study found 62% of consent notices used vague language, which creates regulatory risk and undermines user understanding (analysis of dark patterns in cookie consent notices).
That shows up in design choices such as:
- Accept all on the first layer, but reject only after several clicks
- labels like “improve experience” with no concrete purpose
- category descriptions that hide advertising or cross-site tracking
- banners that imply cookies aren’t active when they already are
These patterns don’t merely create exposure. They produce bad product behaviour. Users become less likely to trust the dashboard, the account settings, and the rest of your privacy communications.
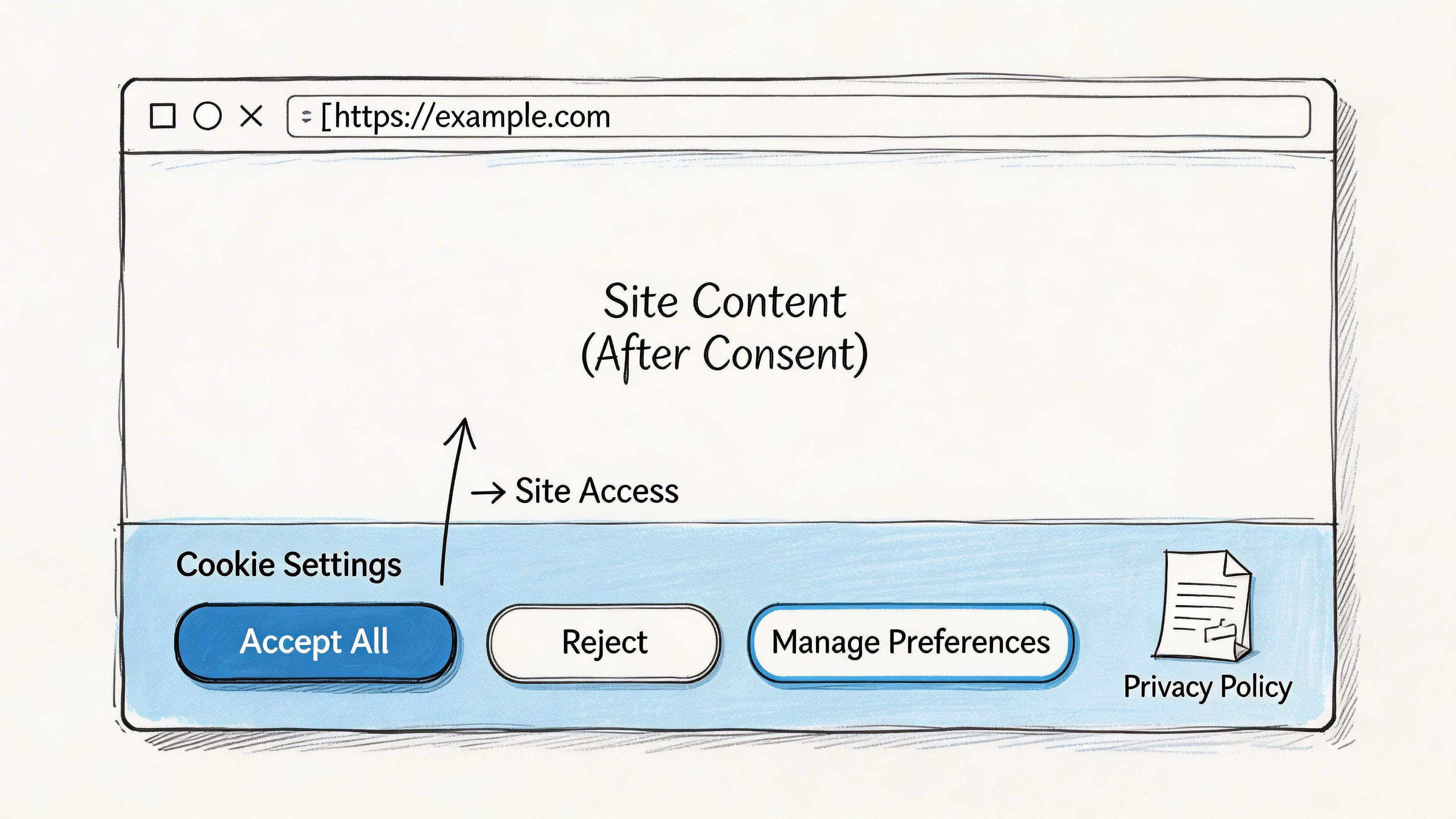
What a usable banner looks like
A compliant banner usually shares a few traits:
-
Balanced actions Accept and reject should both be visible and easy to use.
-
Clear categories Strictly necessary, analytics, advertising, and functional uses should be understandable without legal translation.
-
Specific language Say what the category does. Don’t hide behind broad phrases.
-
Persistent controls Users need a reliable way to revisit the decision.
Here’s a simple way to think about it.
| Weak pattern | Strong pattern |
|---|---|
| “We use cookies to improve your experience” | “We use analytics cookies to measure feature usage and advertising cookies for campaign attribution” |
| Tiny reject link | Reject and accept presented with similar prominence |
| One bundled consent choice | Category-level controls where the law or risk profile demands it |
| Hidden settings page | Always-available preference centre link |
Design note: If legal accuracy and UI simplicity conflict, simplify the architecture first. Don’t hide the complexity in the banner.
Policy writing should support the interface
Your cookie policy shouldn’t repeat the banner in longer form. It should answer the next layer of questions:
- what categories are used
- what each category is for
- whether first parties or third parties set them
- how users can change preferences
- how this relates to the broader privacy policy
A clear policy reduces friction in security questionnaires and vendor diligence. It also gives your support and compliance teams something accurate to point to when customers ask what tracking is active inside the product.
For teams reviewing their documentation model, Devisia’s guide to privacy and cookies policy structure is a practical reference point.
Good UX can reduce operational strain
A strong consent experience reduces follow-up problems. Fewer confused users means fewer support tickets about tracking, fewer internal disagreements about what the banner signifies, and less pressure on engineers to justify behaviour that should have been explicit.
This short walkthrough is useful if your team is reviewing banner patterns and wording before implementation:
In practice, the best banner is the one your engineers can enforce. Fancy preference centres don’t help if the underlying scripts ignore the choices.
Technical Architecture for Cookie Compliance
Compliance stops being theory at this point. If your stack can’t prevent non-essential tracking before the right user action, the rest is window dressing.
The core engineering requirement is prior blocking. GDPR compliance mandates a prior blocking architecture, meaning websites must technically prevent all non-essential scripts and cookies from loading until the user provides explicit consent. This often requires sitewide code alterations and isn’t easy to retrofit, which is why it belongs in initial application design (prior blocking architecture for cookie compliance).
Prior blocking changes how you load the app
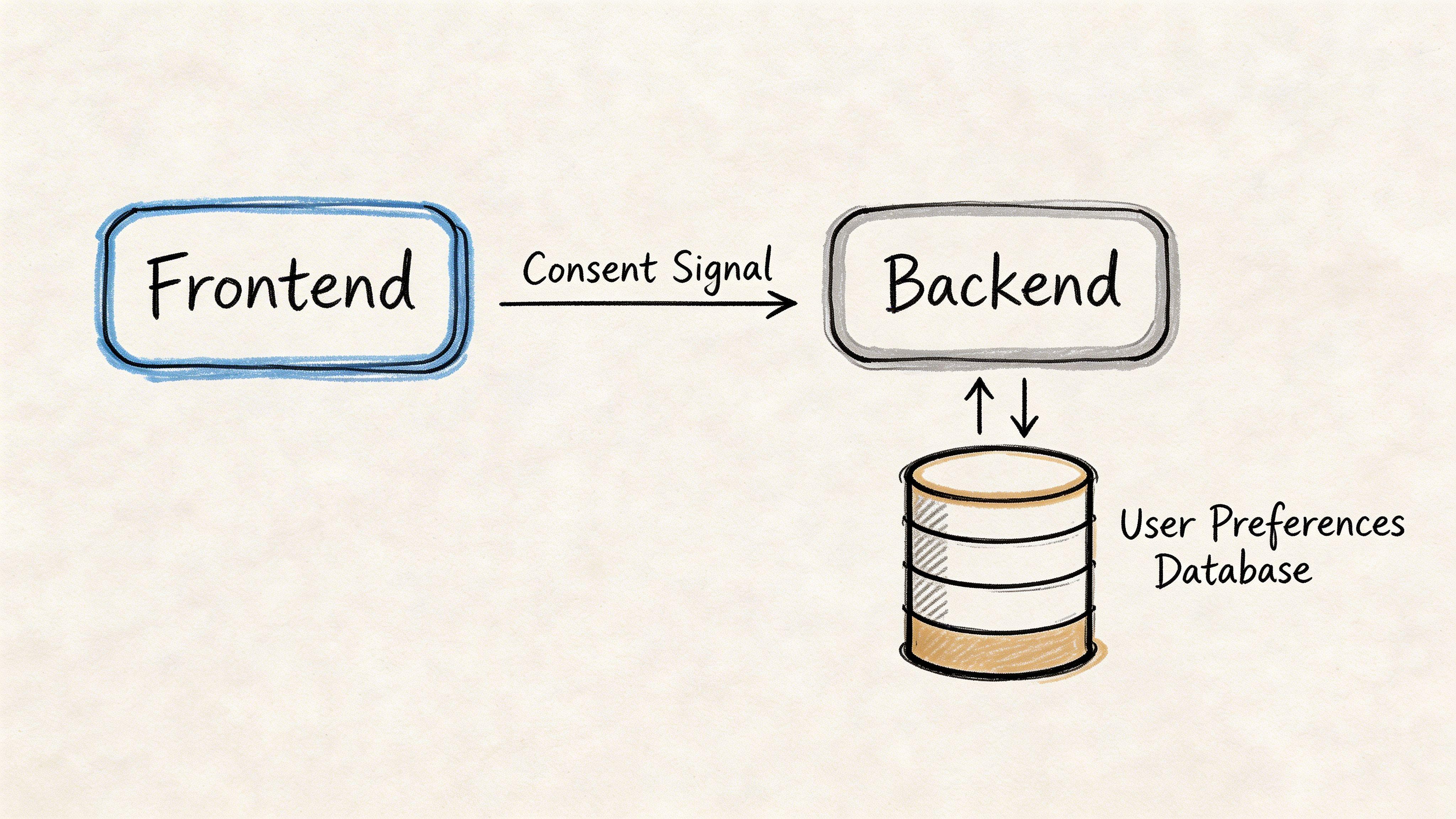
In a compliant design, consent is a control signal. It isn’t merely a preference stored somewhere in local state.
That signal needs to influence:
- Frontend rendering, so blocked categories don’t initialise
- Tag management, so vendor scripts aren’t injected too early
- Backend event handling, so server-side forwarding respects the same decision
- Persistence, so the system can remember and audit the choice
- Cross-surface consistency, so marketing pages and authenticated product areas behave the same way
A common anti-pattern is loading all vendors, then trying to suppress some behaviour after the fact. By then, network requests may already have happened and cookies may already exist.
Client-side blocking versus server-side control
There are two broad implementation patterns. Most mature systems combine them.
Client-side gating
This is the visible layer. The browser checks the current consent state and decides which scripts to load.
It works well when:
- you need straightforward category-based activation
- your vendor set is relatively small
- the team can maintain strict script registration rules
It fails when:
- developers add tags outside the approved loader
- third-party libraries chain-load additional scripts
- the app has multiple entry points with inconsistent bootstrapping
Server-side tagging and event routing
This pattern moves more control away from the browser. Instead of letting every vendor run directly on the client, the application sends limited first-party events to backend services that decide what can be forwarded and to whom.
Benefits include:
- Tighter governance over downstream vendors
- Reduced client-side script sprawl
- Better observability of what data leaves your systems
- Cleaner enforcement when consent changes after initial page load
Trade-offs matter. Server-side tagging adds operational complexity. You need clear schemas, consent-aware routing logic, and discipline about what enters the pipeline in the first place.
If you can’t explain which layer enforces consent for each vendor, you don’t have a reliable consent architecture.
Build versus buy decisions
Organizations typically choose among three models.
| Model | Where it fits | Main risk |
|---|---|---|
| Fully custom consent framework | Products with strong internal platform engineering and unusual requirements | Long-term maintenance burden and legal drift |
| Commercial CMP | Teams that need faster rollout and standard controls | Weak integration if treated as a plug-in rather than part of the app |
| Hybrid approach | SaaS platforms with custom event pipelines and standardised consent UI | Split ownership between product, marketing, and engineering |
A consent management platform can help, but only if it’s wired into enforcement points. One option is Devisia’s consent management platform, which captures user choices, stores consent preferences in first-party cookies, and validates consent state before requests or third-party processing proceed. That kind of tooling is useful when it acts as a system control, not merely a banner generator.
A practical implementation pattern
An effective SaaS pattern often looks like this:
-
Categorise every cookie and tracker Necessary, analytics, advertising, functional, and any special-risk category relevant to your product.
-
Create a single consent service One source of truth for current state, change history, and region-aware rules.
-
Block by default Vendors stay disabled unless the required condition exists.
-
Load through approved wrappers No direct script embeds in product templates or ad hoc components.
-
Pass consent downstream Backend jobs, event buses, and vendor connectors should receive the same policy signal.
-
Support revocation properly Stopping future events is part of the work. Cleaning up persisted identifiers may be too.
Where retrofits usually break
Legacy systems often hide trackers in places the main app team doesn’t govern:
- CMS templates
- support centre embeds
- old landing pages
- billing portals
- tag manager containers with broad edit access
That’s why privacy-by-design matters. It’s not a slogan. It’s an acknowledgement that consent logic has to be woven into loading, routing, and state management from the start.
Implementing Audits and Continuous Governance
A common failure pattern looks like this. The team ships a compliant consent flow, legal signs off, and everyone moves on. Over the next few sprints, marketing adds a new pixel through the tag manager, product enables an SDK module that sets identifiers by default, and support launches a help centre embed outside the main app shell. The banner still renders. The policy still exists. The actual system behaviour has changed.
That is why audit work has to be operational, not annual.
Audits should verify runtime behaviour
A useful cookie audit checks what the product does under real conditions, not what the policy says should happen. For SaaS teams, that means testing across consent states, user states, and product surfaces, then comparing observed requests, storage activity, and downstream processing against the intended rules.
Test at least these cases:
- First visit with no consent choice
- Explicit rejection
- Partial acceptance by category
- Consent withdrawal after earlier acceptance
- Authenticated sessions
- Marketing site versus app shell versus embedded tools
Include browser and server paths in the same review. I regularly see teams block front-end tags correctly while backend services continue sending event data to analytics or ad platforms because consent never reached the queue consumer, webhook handler, or warehouse sync.
Put governance into the delivery system
Cookie compliance breaks in change management long before it breaks in policy text. New vendors arrive through procurement. New scripts arrive through CMS blocks, experimentation tools, and support widgets. Engineers add SDKs for one feature and inherit tracking behaviour they did not intend to ship.
The control point is the delivery workflow.
Add release gates that engineers will use
Privacy review works better when it rides existing process instead of creating a parallel approval system.
-
Definition of ready Any new script, SDK, or vendor integration needs a declared purpose, cookie category, data recipient, owner, and expected regional behaviour before implementation starts.
-
Definition of done Stories that introduce tracking need consent-state tests, evidence of blocked behaviour where required, and confirmation that revocation works after acceptance.
-
Release review Check whether the release changes the cookie inventory, request destinations, tag manager configuration, or vendor-side defaults.
This matters in fast-moving product teams, especially where state privacy rules keep expanding, as noted earlier. The harder part is making sure weekly releases do not bypass the controls you already built.
Add automation where drift is predictable
Manual review catches obvious issues. Automation catches the regressions that appear two weeks later.
-
Automated scanning Run browser tests in staging and production-like environments to detect cookies, local storage writes, and outbound requests under each consent state.
-
Regression alerts Alert on any analytics, advertising, or functional category activity that appears before the required consent condition is met.
-
Configuration control Restrict publishing rights in tag managers, consent tools, CMS templates, and vendor dashboards. Audit logs matter here.
A consent record only helps if you can connect it to the system behaviour that followed.
Keep records that answer incident questions
When legal, a regulator, or an enterprise customer asks what happened on a specific date, the team needs more than a boolean consent flag. The useful record is reconstructable.
Keep enough detail to answer:
- what the user was shown
- what the user selected
- when the selection was recorded
- which categories, scripts, and data flows were enabled from that selection
- whether the user later changed the choice
That usually means versioning the consent copy, preserving category definitions over time, and logging the enforcement decision that your consent service returned. Without that history, teams can prove that a choice was collected but not that the platform honoured it correctly.
Assign ownership before the stack grows
Governance fails when ownership is implied instead of named. In practice, cookie compliance crosses too many systems for one team to handle alone, but each area still needs a clear decision-maker.
A workable model usually looks like this:
| Area | Owner |
|---|---|
| Legal interpretation | Privacy or legal lead |
| Consent UX and wording | Product and design |
| Technical enforcement | Engineering |
| Vendor inventory | Shared between engineering, marketing, and procurement |
| Ongoing audits | Security, privacy, or platform operations |
If vendor sprawl, tag manager changes, and embedded tools do not have explicit owners, your cookie controls will drift. The banner will be the last thing to break, which is exactly why this problem survives so long unnoticed.
Conclusion Building Privacy into Your Products DNA
Web cookie law isn’t difficult because the banner is hard to design. It’s difficult because modern SaaS products are full of hidden dependencies, overlapping jurisdictions, and tracking behaviour that spreads across frontend code, backend services, and vendor integrations.
That’s why the right starting point is architecture.
Teams that do this well make a few disciplined choices early. They categorise tracking clearly. They block non-essential technologies by default where required. They make consent a runtime control, not a visual gesture. They keep policies and banners aligned with system behaviour. Then they audit continuously, because product stacks don’t stay still.
The opposite approach is common and expensive. A team adds a banner late, keeps direct third-party embeds everywhere, and hopes disclosure will compensate for uncontrolled execution. It won’t. That model creates legal exposure, product inconsistency, and technical debt that only gets harder to unwind as the platform grows.
For founders and CTOs, the strategic point is simple. Privacy is an architectural choice, not a feature. When you treat it that way, compliance work becomes more maintainable. It also improves system clarity. Fewer uncontrolled scripts, cleaner data flows, better vendor oversight, and more trustworthy user-facing controls are all signs of a healthier product.
The strongest privacy posture rarely comes from adding more tooling. It usually comes from making fewer assumptions, loading less by default, and building systems that can prove they respected the user’s choice.
If you’re building a SaaS product or modernising an existing platform, Devisia can help design consent-aware architecture, privacy-aligned data flows, and maintainable implementation patterns that fit real delivery constraints.
