Too many IoT projects fail for one simple reason: they start with the technology, not the problem. The allure of a new sensor or platform can be powerful, but successful initiatives are grounded in tangible business outcomes, like reducing operational costs by 15% or boosting asset uptime with predictive maintenance.
This problem-first approach is non-negotiable. It separates a valuable business asset from a costly technical exercise.
Frame the Problem Before Architecting the Solution
The most common mistake in an IoT initiative is architecting a system before deeply understanding why it is being built. Technical leaders are often pressured to adopt the latest technology, leading to over-engineered systems that solve no one’s actual problem. To avoid this trap, a pragmatic framework is needed to anchor the entire project to measurable goals.
This means moving beyond generic use cases like “asset tracking” and focusing on specific, value-driven objectives.
Before drawing a single architectural diagram, critical questions must be answered. What specific data will drive our most critical decisions? What are the absolute, real-world constraints on latency and reliability? How will this architecture scale from a ten-device proof-of-concept to a ten-thousand-device deployment? Answering these questions forces clarity and manages stakeholder expectations from day one.
Deconstructing the Core Components
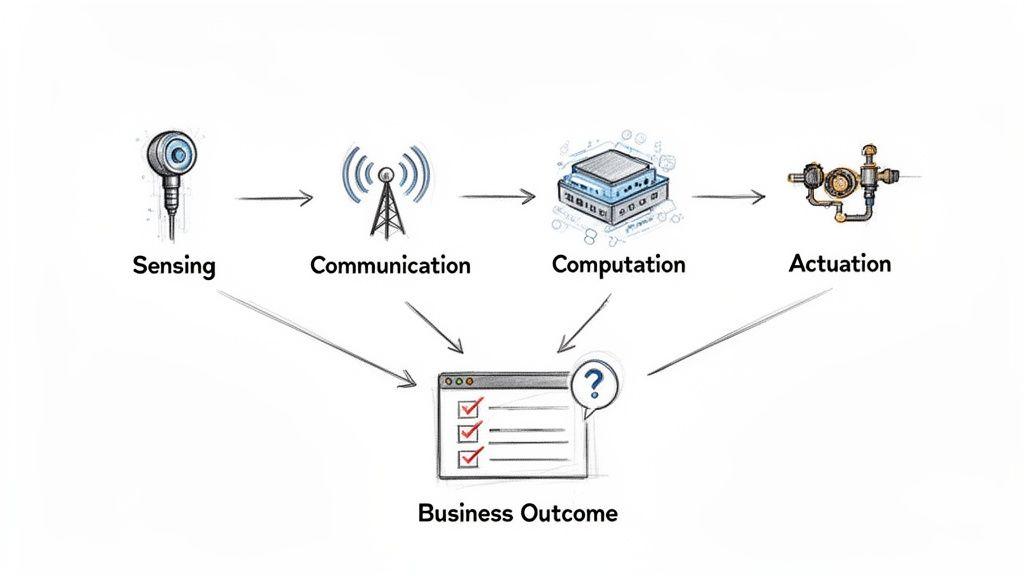
Any IoT problem can be broken down into four fundamental components. Analyzing these pillars clarifies requirements and identifies potential roadblocks early in the process.
- Sensing: What physical property must be measured? This could be temperature, location, vibration, or visual data. The sensor choice dictates data quality, power consumption, and the final cost per device.
- Communication: How will data be transmitted from the sensor to its destination? Options range from low-power, long-range networks like LoRaWAN for small data packets to high-bandwidth cellular or Wi-Fi for richer data streams. Each option presents significant trade-offs in cost, battery life, and throughput.
- Computation: Where will the data be processed? This is a critical architectural decision, balancing on-device processing at the edge for low-latency responses against sending data to the cloud for complex analytics and model training.
- Actuation: Based on the processed data, what action should the system perform? This could range from sending an alert to autonomously adjusting industrial machinery.
This structured approach transforms a vague concept into a concrete set of engineering requirements. The following checklist provides a framework for initial technical discussions.
Initial IoT Problem-Framing Checklist
This table provides a starting point for technical leaders to define the scope and constraints of an IoT initiative before commencing architectural work.
| Domain | Key Question | Example Implication |
|---|---|---|
| Business Outcome | What specific, measurable KPI is being targeted? | ”Reduce spoilage-related losses by 20%,” not “Monitor temperature.” |
| Data & Sensing | What is the minimum data required to achieve the outcome? | Is temperature data needed every second, or is every 15 minutes sufficient? |
| Environment | What are the physical deployment conditions, including power and connectivity? | A sensor in a remote agricultural field has different constraints than one in a factory with reliable Wi-Fi. |
| Latency | How quickly must a decision be made after data is collected? | An emergency shutdown requires millisecond response (edge), while a weekly report does not (cloud). |
| Scale | What does success look like at 10, 100, and 10,000 devices? | The architecture for a pilot is often fundamentally different from a production system. |
| Security | What is the impact if a device is compromised or data is intercepted? | Medical device security requirements are far more stringent than those for a smart waste bin. |
By working through these questions, you build a solid foundation that directly links technical choices to business value.
This methodical approach is essential. The market for IoT platforms—which help manage these components—is a testament to their importance. In the United States alone, it is projected to grow from USD 4.71 billion in 2025 to USD 14.67 billion by 2034. You can explore the full research on IoT platform growth to understand the centrality of these systems.
By framing your project around the four pillars—Sensing, Communication, Computation, and Actuation—you ensure the architecture is built to deliver business value, not just to showcase a new technology. This is the foundation of a reliable and scalable IoT strategy.
Deconstructing Modern IoT Architecture Layers
A successful IoT system is not a collection of connected devices; it is a layered, cohesive architecture where each component has a defined responsibility. A decision made in one layer creates ripple effects throughout the entire system. Effective solutions for iot start with a clear architectural blueprint that balances performance, cost, and scalability.
This architecture is typically organized into four distinct layers, each solving a specific class of problems, from interfacing with the physical world to delivering business value through applications.
The Device and Firmware Layer
This is where the physical and digital worlds intersect. The device layer comprises hardware—sensors, actuators, microcontrollers—and the embedded software, or firmware, that runs on it. This layer is responsible for sensing environmental conditions or actuating physical changes.
The trade-offs at this layer are significant. A low-power sensor designed to operate for a decade on a single battery will have minimal processing power and limited data transmission capacity. Conversely, a device with a powerful processor for running computer vision models will require a constant power source and thermal management.
Firmware controls the device’s behavior, dictating how it gathers data and communicates. A naive approach, such as hardcoding network credentials, creates a significant security vulnerability. A robust approach involves secure boot processes and over-the-air (OTA) update capabilities to patch security flaws remotely.
The Connectivity and Edge Layer
Once a device collects data, it must transmit it. This layer is responsible for secure and reliable communication between devices and the network. It is also where edge computing becomes relevant, enabling data processing closer to the source.
The choice of communication protocol is a defining architectural decision.
- MQTT (Message Queuing Telemetry Transport): A lightweight protocol ideal for low-bandwidth, high-latency environments. It is highly efficient for sending small, frequent updates from thousands of devices.
- CoAP (Constrained Application Protocol): Designed for constrained devices and networks, commonly used in machine-to-machine (M2M) applications.
- Cellular (4G/5G) & Wi-Fi: Suitable for high-bandwidth requirements like video streaming but entail higher power consumption and costs.
Edge gateways can act as local hubs, aggregating data from multiple nearby devices before forwarding it to the cloud. This reduces connectivity costs and enables real-time local processing. For example, an edge device on a factory floor can analyze vibration data, detect an imminent machine failure, and trigger an immediate shutdown—a task where the latency of a cloud round-trip would be unacceptable.
The Cloud Platform Layer
This layer serves as the central nervous system for the entire IoT operation, handling large-scale data ingestion, storage, and analysis. It is responsible for managing the device fleet, processing data streams, and hosting core business logic. Leading providers like AWS IoT and Azure IoT Hub offer managed services that handle much of the undifferentiated heavy lifting.
This layer must be designed for massive scale, capable of handling data from potentially millions of devices, routing messages to appropriate services, and storing data cost-effectively and accessibly. The patterns here often resemble a service-oriented architecture, with microservices handling specific functions like device authentication, data transformation, or rule-based alerting. You can learn more about how a service-oriented architecture can structure complex systems in our dedicated guide.
A critical mistake is treating the cloud as a mere data repository. A well-designed platform layer uses rules engines and serverless functions to filter, enrich, and act on data in real time, converting raw telemetry into actionable intelligence.
The Application Layer
The final layer is where data is transformed into business value. This is the component users interact with, whether it’s a dashboard for visualizing industrial data, a mobile app for controlling a smart device, or an API that feeds information into an existing ERP system.
This layer’s primary function is to translate complex underlying data into an intuitive and useful format. It is about providing insights that drive decisions. For instance, a logistics application might not only display a truck’s location but also predict its arrival time based on live traffic data and alert managers to potential delays. This is where the investment in the other three layers yields a tangible return.
Embedding AI for Intelligent and Autonomous Operations
An IoT system that only collects and displays data represents a missed opportunity. Real value is unlocked when the system can interpret its own data and act autonomously. This is where Artificial Intelligence (AI) and Machine Learning (ML) transform passive data streams into active, intelligent operations. It is a core part of modern solutions for iot, turning simple devices into decision-making agents.
The objective is to move beyond dashboards and build systems that can predict failures, identify quality issues, or optimize processes dynamically. This requires an architectural shift from merely funneling data to the cloud to placing intelligence where it is most effective—often at the edge.
The hierarchy below illustrates the typical layers of an IoT architecture. It serves as a foundation for embedding AI at various levels, from the device to the cloud.
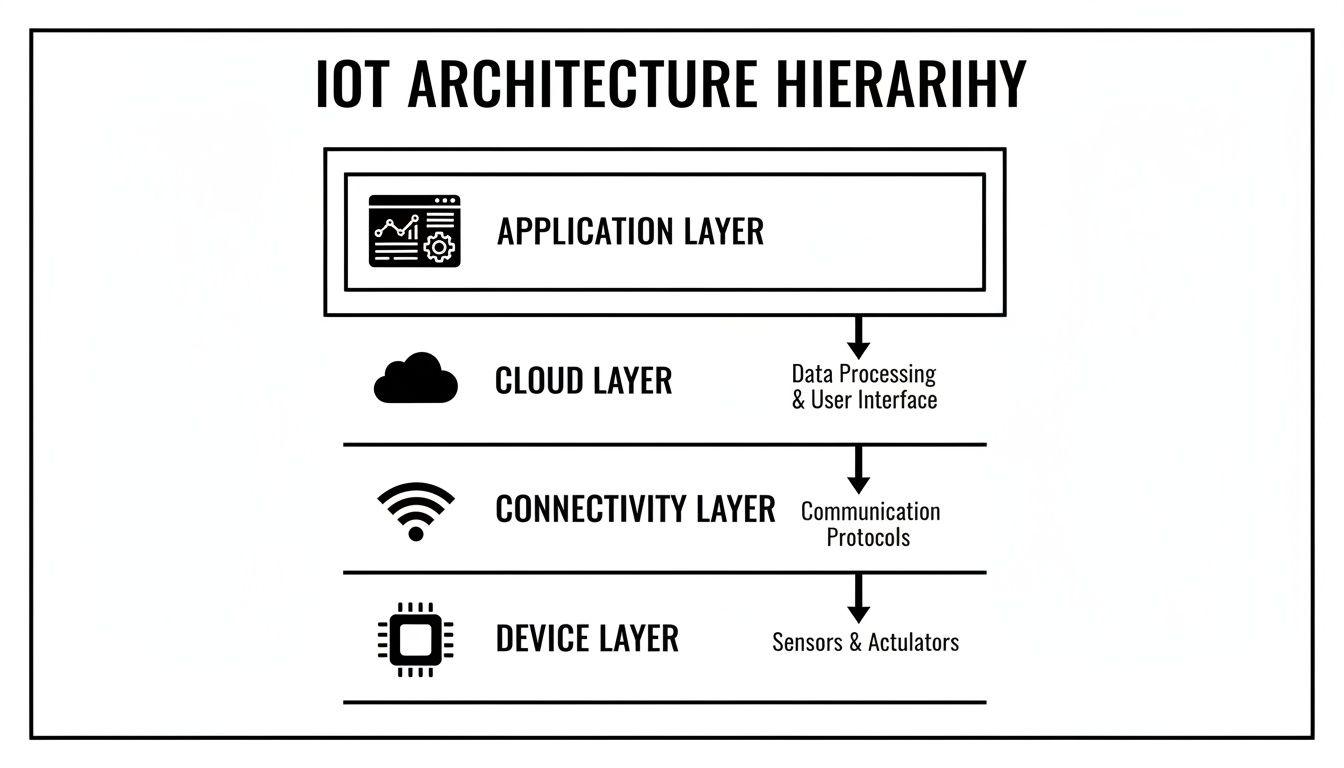
This structure is a map for AI implementation. It shows how AI can reside at the edge (on devices or gateways) for tasks requiring immediate responses, or in the cloud for heavy-duty analytics, with results delivered to the application layer.
From Anomaly Detection to Agentic Workflows
Integrating AI is a spectrum of capabilities, not a single step. Each level of intelligence solves a different class of problem with increasing complexity and business impact. The key is to determine where the processing should occur.
A pragmatic starting point is deploying lightweight models directly on edge devices.
- Edge-Based Anomaly Detection: An industrial pump with a vibration sensor can run a simple ML model to learn its normal operating baseline. If an anomalous vibration is detected, it can trigger a local alert or shut down the pump to prevent failure, all without cloud latency.
- Real-Time Computer Vision: On a manufacturing line, a camera connected to an edge gateway can run a vision model to inspect products for defects. This provides instant quality control, flagging faulty items faster than a human operator and avoiding the need to stream high-bandwidth video to the cloud.
The next evolution is building systems that act, not just alert. This is where agentic workflows become relevant.
An agentic workflow empowers an IoT system to execute a sequence of actions to achieve a goal. It’s the difference between a system that reports, “There is a problem,” and one that reports, “I found a problem, analyzed the causes, and have already initiated a fix.”
Implementing Safe and Controlled Autonomy
Granting a system autonomy introduces risk. A poorly designed workflow could take costly or dangerous actions. Therefore, implementing guardrails and human-in-the-loop (HITL) systems is non-negotiable. These mechanisms ensure that autonomous actions remain safe, predictable, and aligned with business rules.
- Technical Guardrails: These are hard-coded limits on system capabilities. An autonomous agricultural system might be permitted to adjust irrigation levels but physically prevented from dispensing more than a pre-set amount of fertilizer within a 24-hour period.
- Human-in-the-Loop (HITL) Systems: For critical decisions, the AI should propose an action for human approval. In a smart grid, if the system detects an anomaly suggesting a power reroute, it would present its findings and recommendation to a human operator for final authorization.
By building AI integration with these safety patterns, you can create powerful, autonomous solutions without sacrificing control. This methodical approach elevates an IoT solution from a simple data-gathering tool to an intelligent system that delivers measurable business value.
Building Security and Governance into Your IoT Architecture
In IoT, security is not an optional feature; it is the foundation of the architecture. A single compromised device can serve as an entry point into your network, and a data breach can irrevocably damage customer trust. For any credible IoT solution, security and governance must be integrated into every layer, from device provisioning to data retirement.
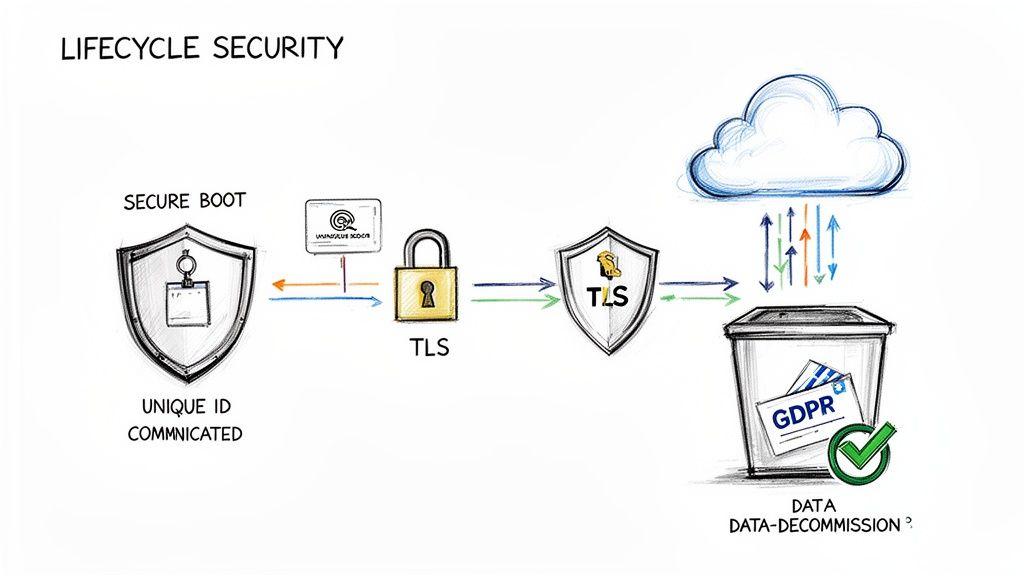
This proactive stance is the only viable approach. Naive methods, such as using hardcoded credentials or deploying devices without a firmware update strategy, create brittle, vulnerable systems that are easily exploited at scale. A robust architecture treats security as an ongoing lifecycle.
Non-Negotiable Security Elements
To build a trustworthy system, certain security practices are non-negotiable. They are the bedrock of a defensible architecture and must be implemented from day one.
- Unique Device Identity and Secure Provisioning: Every device requires a unique, unforgeable identity, typically stored in a hardware secure module. This identity authenticates the device before it is permitted to connect to your network, preventing unauthorized hardware access.
- Secure Boot: This critical process ensures a device only loads trusted, cryptographically signed firmware. It prevents malicious actors from loading compromised software onto your hardware, securing the device’s core functions.
- End-to-End Encryption: All data must be encrypted, both in transit and at rest. Communications between devices, gateways, and the cloud should be protected using standard protocols like TLS (Transport Layer Security) or its lightweight variant, DTLS (Datagram Transport Layer Security), for constrained devices.
These three pillars create a chain of trust. Secure boot ensures the device runs authentic code, its unique identity verifies it as a legitimate part of your fleet, and encryption protects its communications.
Integrating Governance and Compliance by Design
Beyond technical security controls, data governance is a major architectural concern, particularly with regulations like GDPR and NIS2. Compliance cannot be an afterthought; it must be designed into your data pipelines from the outset.
This is the central tenet of Privacy by Design, a philosophy that embeds data protection directly into the system architecture. For a deeper analysis, refer to our complete guide on how to implement Privacy by Design in your systems.
This proactive approach is essential in a rapidly expanding market. Across Europe, IoT solutions are driving major upgrades in smart cities and industry. The U.K. market alone is projected to reach USD 56.91 billion by 2026 as part of a continent-wide push toward Industry 4.0. You can discover more insights about this market expansion and its key drivers.
A common failure mode is collecting as much data as possible “just in case.” This not only increases storage costs but also significantly expands compliance risk. A superior architecture enforces data minimization by design, collecting only what is necessary to achieve a specific business outcome.
Key governance principles must be translated into technical controls within your architecture.
- Data Minimization: Configure devices and data pipelines to collect only the fields absolutely necessary for the defined business purpose. If you only need to know whether a machine is on or off, do not collect its precise energy consumption data.
- Purpose Limitation: Architect your system so that data collected for one purpose (e.g., predictive maintenance) cannot be easily used for another (e.g., employee performance monitoring) without explicit consent and technical guardrails.
- Data Retention and Decommissioning: Implement automated policies that delete or anonymize data once it is no longer needed. This must include a secure process for wiping data from devices when they are decommissioned.
By building these security and governance principles directly into your IoT architecture, you create a system that is not only powerful and scalable but also defensible, compliant, and trustworthy.
Choosing the Right Implementation and Sourcing Strategy
A company’s business lifecycle stage dictates its optimal approach to an IoT project. A startup validating an idea has vastly different needs from an enterprise integrating a solution into legacy systems. The decision is not about selecting the “best” technology but finding the right fit for immediate goals, budget, and risk tolerance.
A mismatch here is costly. Startups can exhaust their funding by building a custom platform for an unvalidated product. Enterprises can get stuck in endless pilot projects using off-the-shelf tools that fail to meet their security or scalability requirements. The correct approach is pragmatic and deliberate, based on the company’s current context.
A Roadmap for Startups, SMBs, and Enterprises
The implementation journey evolves as a business grows. Each stage has a distinct primary focus, which dictates technology choices and introduces different risks.
- Startup (Validation Phase): The sole priority is speed to learning. The goal is to get a Minimum Viable Product (MVP) to users to validate the core idea as quickly and cheaply as possible. This means leveraging off-the-shelf hardware and managed IoT platforms. Customization is counterproductive; the objective is to gather data and feedback, not to build a perfect system.
- SMB (Scaling Phase): With a validated concept, the focus shifts from speed to building a reliable, scalable product. This involves developing custom dashboards, refining device firmware for stability, and selecting connectivity partners with solid service-level agreements (SLAs). The goal is to build a robust foundation for growth.
- Enterprise (Integration Phase): The primary challenge is no longer the IoT technology itself but its integration with a complex web of existing systems, such as ERPs and manufacturing execution systems (MES). Key considerations include meeting strict security protocols and adhering to long-term governance policies. Solutions must be designed for maintainability and seamless integration with existing business operations.
How to Evaluate Platforms and Partners
Selecting the right external platforms or development partners is a critical decision. It is easy to be distracted by marketing and extensive feature lists, but these rarely determine long-term success. A better evaluation framework prioritizes substance.
When assessing a partner or platform, investigate these areas:
- Architectural Alignment: Does their technology philosophy align with yours? A heavy, monolithic platform will add unnecessary complexity and cost to a lean, event-driven system.
- Technical Support and Documentation: What level of support is available during a critical failure? Clear, comprehensive documentation is an indicator of a mature, well-maintained product.
- Long-Term Viability: Is this product a core part of the vendor’s business, or a side project that could be discontinued? Partnering with a company that might sunset the service introduces significant business risk. Our guide on cloud computing versus on-premise solutions offers relevant insights on this topic.
The best partner is not the one with the most impressive demo. It is the one whose technical architecture, support model, and business stability align with your long-term roadmap. Focusing on these fundamentals will prevent costly rework.
The following table breaks down the criteria and trade-offs at each business stage.
IoT Solution Criteria by Business Stage
This table compares the primary focus, technology choices, and key risks for startups, SMBs, and enterprises to help align strategy with your company’s trajectory.
| Criteria | Startup (Validation) | SMB (Scaling) | Enterprise (Integration) |
|---|---|---|---|
| Primary Focus | Speed to MVP and market feedback | Product reliability and user experience | System integration and governance |
| Technology Choices | Off-the-shelf hardware; managed PaaS | Custom dashboards; production-grade firmware | Bespoke integrations; private networks |
| Key Risks | Building a product no one wants | Technical debt and scalability issues | Security vulnerabilities; compliance failures |
Ultimately, choosing the right path requires an honest assessment of current needs and constraints. An enterprise strategy will fail a startup, and a startup’s approach is insufficient for a scaling SMB. Matching your strategy to your stage is the first step toward a successful IoT implementation.
Managing Total Cost of Ownership and System Observability
An IoT deployment is only viable if it is financially and operationally sustainable. Launching a system is one challenge; operating it efficiently for years is another. This requires a sharp focus on two critical, long-term factors: Total Cost of Ownership (TCO) and system observability.
Ignoring these from the start leads to systems that are too expensive to scale and impossible to debug during failures. A pragmatic IoT architecture confronts these realities from the outset.
Breaking Down the Complete Cost Picture
The hardware purchase price is a dangerously small fraction of the true TCO. A complete financial model must account for every recurring fee and hidden expense across the system’s entire lifecycle. Failure to do so risks creating a solution that becomes a financial black hole at scale.
A superficial cost analysis almost always misses the largest long-term budget drains.
The most expensive component of many IoT systems is not the hardware or the software, but the data. Unchecked connectivity and cloud processing fees can silently undermine a project’s financial viability, especially at scale.
To build a sustainable model, you must meticulously track every cost vector:
- Hardware and Development: This includes the initial cost of devices, gateways, and the non-recurring engineering (NRE) for design and certification.
- Connectivity Fees: These costs scale with deployment. They include monthly SIM card charges, data overage penalties, and platform access fees from cellular or satellite providers.
- Cloud Services: This is a major variable, encompassing data ingestion, storage tiers (hot vs. cold), compute for processing and analytics, and database operations.
- Maintenance and Support: This represents the long tail of cost, covering ongoing firmware updates, device replacements (including technician dispatch, or “truck rolls”), security patching, and platform support personnel.
Engineering a Cost-Optimized Architecture
With a clear view of the costs, you can design an architecture to control them. This is not about choosing the cheapest component but making intelligent trade-offs to build a system that meets requirements without wasting resources.
Effective cost-optimization patterns are built into the architecture. For instance, edge processing is a powerful lever for cost management. By filtering, aggregating, or analyzing data on the device or gateway, you can significantly reduce the volume of data sent to the cloud, directly cutting connectivity and cloud ingestion costs.
Other key tactics include:
- Intelligent Data Routing: Differentiate data by importance. The system should distinguish between a critical, real-time alert and routine telemetry that can be batched and sent less frequently over a cheaper connection.
- Strategic Use of Caching: Implementing a cache at the edge gateway or in the cloud can dramatically reduce the load on expensive databases and compute services for frequently requested data.
- Dynamic Data Policies: Build the system with the flexibility to remotely configure data transmission frequency. During a critical event, updates may be needed every second, but for normal operations, once an hour may be sufficient—and far cheaper.
Building Observability into the System
A system you cannot see is a system you cannot manage. Observability—the ability to understand a system’s internal state from its external outputs—is non-negotiable for reliability. Without it, you are unable to diagnose failures, identify performance bottlenecks, or predict problems before they cause an outage.
Observability must be engineered into every layer of the architecture from the start. You need deep visibility into:
- Device Health: Monitor metrics such as battery level, signal strength, memory usage, and firmware version to proactively identify failing devices.
- Data Pipeline Latency: Track the time it takes for a message to travel from a sensor to your application to pinpoint delays in connectivity or cloud processing layers.
- Anomaly-Based Alerting: Use monitoring systems that learn the normal behavior of your devices and only alert you when a genuine anomaly occurs, avoiding the noise of static thresholds.
By pairing a realistic TCO model with a robust observability strategy, you build and maintain reliable, cost-effective solutions for iot that perform predictably as they scale.
Frequently Asked Questions About IoT Solutions
Here are common, practical questions from technical leaders planning and building IoT solutions.
What Is the Biggest Mistake Companies Make When Starting an IoT Project?
The single biggest mistake is focusing on technology before defining the business problem. Many projects fail because they start with a vague goal like “we need to use IoT” instead of a concrete objective like “we need to reduce machine downtime by 20%.”
A successful initiative always begins with a measurable business outcome. This clarity dictates the necessary data, device functionality, and system architecture. Without it, you risk building a technically impressive but commercially useless solution.
Should We Build Our Own IoT Platform or Use an Existing One?
For most companies, building an entire IoT platform from scratch is a significant distraction from their core business. The decision depends on the scale and uniqueness of your requirements.
Using an established platform like AWS IoT or Azure IoT Hub dramatically accelerates development time and provides robust, scalable infrastructure. A full “build” approach is only justifiable if your requirements are so specific that no existing platform can meet them, and you have the deep engineering resources to maintain it long-term.
Often, the most pragmatic path is a hybrid one: leverage a platform’s core services for undifferentiated heavy lifting while building your unique application logic on top.
How Do We Ensure Our IoT Solution Remains Secure Over Time?
IoT security is not a one-time setup; it is an ongoing process that must be integrated into the system from day one. It requires a multi-layered strategy.
- Secure Device Lifecycle: Every device needs a unique, trusted identity, provisioned securely during manufacturing.
- Over-the-Air (OTA) Updates: A reliable method for deploying firmware updates remotely is essential to patch vulnerabilities as they are discovered.
- End-to-End Encryption: All data must be encrypted, both in transit (from device to cloud) and at rest (in storage), without exception.
- Continuous Monitoring: Actively monitor network traffic and device behavior. Anomalies are often the first sign of a security breach.
Security cannot be an afterthought. It must be an architectural concern from the beginning to build a trustworthy and defensible system.
At Devisia, we help businesses architect and build secure, scalable, and maintainable IoT solutions that deliver measurable value. We provide a clear path to meaningful, reliable software, turning your business vision into a reality. Learn more about our approach.
