Mobile banking applications are no longer a supplementary channel; they are the primary interface between a financial institution and its customers. For technical leaders, this shift elevates the mobile platform from a feature to a core engine for business growth, influencing everything from operational resilience to customer retention.
A well-architected mobile presence is a non-negotiable strategic asset. Superficial implementations create significant technical debt and regulatory risk. This guide outlines the key architectural decisions and engineering trade-offs required to build a secure, compliant, and scalable mobile banking system.
The Problem: Legacy Systems vs. Digital-First Demands
The transition from branch-first to digital-first banking has fundamentally rewired customer expectations for performance, availability, and security. This places immense pressure on the underlying architecture of mobile banking systems, exposing the limitations of legacy infrastructure.
For CTOs and product leaders, the challenge is not merely a user experience problem but a core business continuity risk. The quality of a mobile banking app directly impacts operational stability and regulatory standing. A poorly engineered application introduces systemic vulnerabilities, while a thoughtfully architected system provides a durable competitive advantage.
Strategic Implications of a Mobile-First Architecture
Adopting a mobile-first strategy involves reorienting business processes, technology investments, and customer engagement around mobile as the central point of interaction. The benefits are measurable and well-documented.
In the United States, for instance, mobile banking is the dominant channel, with 54% of customers using apps as their primary method for account management. This trend has been consistent for six consecutive years. Financial institutions that have architected for this shift have reported tangible gains, with some increasing deposit balances by 10% to 15% through optimized digital channels alone.
The Risks of Retrofitting Legacy Core Systems
A common and high-risk approach is to place a modern mobile interface on top of a legacy core banking system. These platforms, often monolithic and decades old, were not designed for the real-time, high-concurrency, and security-intensive workloads of mobile banking. Attempting to bridge this gap with a simple API gateway is an insufficient solution.
This approach introduces critical failure points:
- Performance Bottlenecks: Legacy systems cannot handle the thousands of concurrent connections and low-latency responses that mobile users expect, leading to timeouts and service degradation.
- Security Vulnerabilities: Bolted-on security layers often leave critical gaps, failing to provide the end-to-end encryption and modern authentication required to protect sensitive financial data.
- Scalability Constraints: Monolithic systems lack elastic scalability. They are prone to failure during peak transaction periods, leading to service outages and reputational damage.
This architectural anti-pattern results in a brittle, insecure, and unreliable user experience, ultimately leading to customer churn and increased regulatory scrutiny. A deliberate, modern architectural approach is required.
Foundational Technology Stack Decisions
The selection of a technology stack is a foundational decision with long-term consequences for performance, security, maintainability, and total cost of ownership. Each architectural choice represents a trade-off, balancing initial development velocity against long-term operational stability and flexibility.
The first critical decision point is the frontend technology, which directly shapes the user experience, development lifecycle, and the implementation of security features like hardware-backed biometrics.
Frontend: Native vs. Cross-Platform Trade-offs
A native development approach involves building two separate applications: one using Swift for iOS and another using Kotlin for Android. This strategy provides optimal performance, direct access to the latest device hardware (e.g., secure enclaves, advanced biometric sensors), and the most robust security posture. The primary trade-off is higher initial cost and complexity due to the management of two distinct codebases and specialized development teams.
Cross-platform frameworks like React Native or Flutter offer a single-codebase solution that compiles for both iOS and Android. This can reduce initial development time and resource allocation. However, this efficiency comes with significant trade-offs, including potential performance degradation, delayed access to new OS features, and increased complexity when interfacing with specific hardware security modules.
For mobile apps banking, where security and performance are non-negotiable, a native approach is typically the more prudent long-term investment.
The decision between native and cross-platform is a business decision, not merely a technical one. A native build prioritizes maximum performance and security assurance, while a cross-platform approach optimizes for initial development speed and cost.
Backend Architecture: Monolith vs. Microservices
The backend architecture dictates the system’s scalability, resilience, and maintainability. Historically, a monolithic architecture, where all functions are bundled into a single, tightly-coupled application, was the standard.
While monoliths may appear simpler to build and deploy initially, they become exceedingly difficult to update, scale, and secure as they grow. A failure in a single component, such as a loan application module, can cascade and cause a total system outage—an unacceptable risk for a financial institution.
A modern microservices architecture decomposes the application into a collection of small, independent, and loosely coupled services. Each service handles a discrete business function—such as user authentication, transaction processing, or account management—and communicates with others via well-defined APIs.
This modular approach offers distinct advantages for a mobile banking platform:
- Improved Scalability: High-demand services, such as payment processing, can be scaled independently without impacting the rest of the system.
- Enhanced Fault Isolation: An issue within a non-critical service (e.g., push notifications) will not cause a catastrophic failure of the entire application.
- Technology Heterogeneity: Teams can select the optimal technology stack for each specific service, avoiding vendor or framework lock-in.
- Simplified Compliance and Auditing: It is far simpler to manage, audit, and demonstrate regulatory compliance on a service-by-service basis.
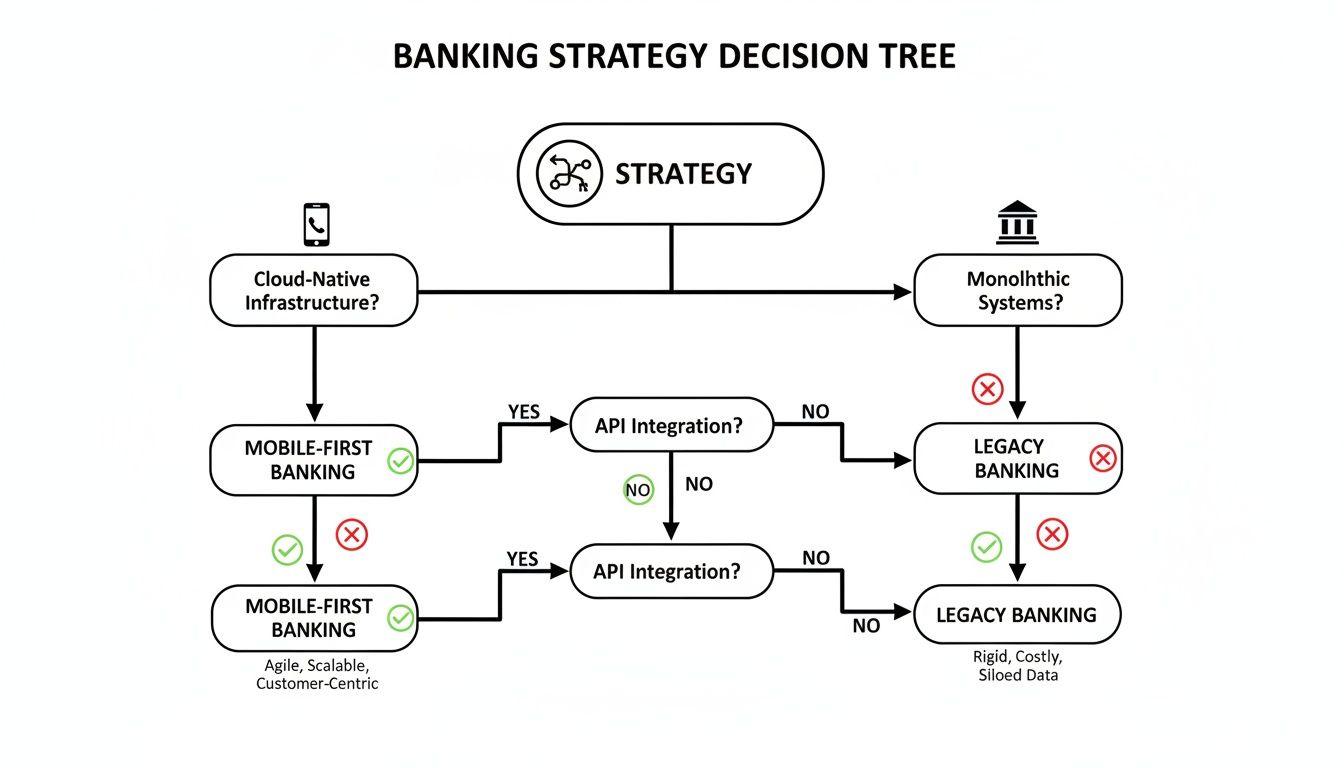
This decision tree illustrates the strategic trade-offs between a modern, cloud-native architecture and a legacy approach.
While a microservices architecture introduces its own set of complexities, particularly around distributed data management and service orchestration, its benefits in resilience and scalability align directly with the stringent demands of modern financial services.
For a deeper dive into the principles of decoupled systems, our guide to service-oriented architecture provides further technical detail.
Architecting for Security and Privacy by Design
In mobile banking, security is not a feature; it is a foundational architectural principle. A superficial approach—for example, relying solely on transport-layer encryption—creates unacceptable risks for both customers and the institution.
The only viable methodology is a privacy by design philosophy, where every architectural decision is evaluated through a security and data minimization lens. The objective is to implement a defense-in-depth strategy, where multiple, independent security controls work in concert to protect sensitive data at all stages of its lifecycle. To understand how this shapes system development, you can learn more about privacy by design.

Securing Data in Transit, at Rest, and in Use
Financial data must be protected across its entire lifecycle: on the device (at rest), over the network (in transit), and during processing on backend systems. This requires a multi-layered approach to cryptography and data storage.
-
End-to-End Encryption (E2EE): All communication between the mobile client and backend servers must be encrypted using strong, modern protocols such as TLS 1.3. This ensures that intercepted data remains confidential and its integrity is preserved.
-
Secure On-Device Storage: Sensitive information such as authentication tokens, session data, or cryptographic keys must never be stored in plaintext on the user’s device. Instead, leverage the platform’s native, hardware-backed secure containers: the Keychain on iOS and the Keystore on Android. These systems encrypt data and store it within a secure enclave, making it extremely difficult for other applications or attackers to access.
-
Certificate Pinning: This is a critical defense against sophisticated man-in-the-middle (MITM) attacks. Pinning involves embedding the server’s public key or SSL certificate within the mobile application. The app will then reject connections to any server that does not present the pinned credential, mitigating the risk of rogue access points and compromised Certificate Authorities.
Implementing Robust Authentication and Anti-Tampering Controls
Beyond data protection, the architecture must actively defend against unauthorized access and malicious modification of the application itself.
A common implementation flaw is treating multi-factor authentication (MFA) as a simple check-box exercise. A robust MFA strategy must be adaptive, integrating biometrics, device-specific cryptographic tokens, and potentially behavioral analytics to create a layered and risk-aware security posture.
The following table maps common threats to specific architectural mitigation strategies.
Threat Vector vs. Mitigation Strategy
| Threat Vector | Description of Risk | Primary Mitigation Strategy | Architectural Consideration |
|---|---|---|---|
| Man-in-the-Middle (MITM) | An attacker intercepts and potentially alters communication between the app and the server. | Certificate Pinning | Embed the server’s public key or certificate within the mobile app’s code to prevent spoofing. |
| Unauthorised Access | A malicious actor gains access to a user’s account through stolen credentials. | Multi-Factor Authentication (MFA) | Integrate biometric, TOTP, or hardware token verification at critical touchpoints (login, transfers). |
| Data Extraction from Device | Sensitive data is stolen from a lost or compromised device. | Secure On-Device Storage | Use native, hardware-backed Keystore (Android) and Keychain (iOS) for all sensitive data. |
| Reverse Engineering | Attackers decompile the app to find vulnerabilities, API keys, or proprietary logic. | Code Obfuscation | Integrate an obfuscation tool into the build process to make the compiled code difficult to read. |
| Running on Compromised OS | The app operates on a rooted or jailbroken device, bypassing OS-level security. | Root/Jailbreak Detection | Implement checks at startup to detect compromised environments and limit app functionality accordingly. |
Key Defense Mechanisms
-
Multi-Factor Authentication (MFA): This is a mandatory control. A robust implementation combines multiple factors: something the user knows (password), something they have (a device generating a one-time code), and something they are (biometrics). The system should support modern standards like Time-based One-Time Password (TOTP) or FIDO2.
-
Code Obfuscation: The application’s compiled binary should be obfuscated to hinder reverse-engineering attempts. Obfuscation tools rename classes, methods, and variables, making the decompiled code significantly more difficult for an attacker to analyze for vulnerabilities.
-
Anti-Tampering and Root/Jailbreak Detection: The application must be able to detect if it is running in a compromised or hostile environment, such as a jailbroken iOS device or a rooted Android device. Upon detection, the app should either refuse to run or operate in a degraded, limited-functionality mode to protect user data from inspection tools and malware.
These mechanisms form a resilient security framework. By integrating these controls into the architecture from the outset, you transition from a reactive security posture to a proactive one, safeguarding customer data and building institutional trust.
Translating Regulatory Compliance into System Architecture
For compliance and IT leaders, European regulations like GDPR, NIS2, and the Digital Operational Resilience Act (DORA) are not abstract legal frameworks; they are concrete engineering requirements. A checklist-based approach to compliance is insufficient and creates significant regulatory risk.
Regulators now demand evidence of embedded compliance, where regulatory principles are demonstrably built into the system architecture, code, and operational processes.
From GDPR Principles to Data Lifecycle Management
The General Data Protection Regulation (GDPR) has direct architectural implications. The “right to erasure” (Article 17), for example, presents a complex engineering challenge in a distributed microservices environment.
A naive implementation, such as setting an is_deleted = true flag in a central database, is non-compliant. A user’s data is often replicated across numerous services for transaction histories, marketing communications, fraud detection, and customer support.
A compliant solution requires an event-driven data lifecycle management architecture:
- Event-Driven Deletion: A user’s deletion request triggers an event that is broadcast across the system.
- Service-Level Responsibility: Each microservice that stores personal data must subscribe to this event and be responsible for permanently deleting the relevant information from its own datastore.
- Anonymisation and Aggregation: For data required for long-term analytics, all personally identifiable information (PII) must be cryptographically stripped, leaving only anonymized, aggregated data that cannot be re-identified.
This pattern ensures that data deletion is a comprehensive, verifiable, and auditable process, transforming a legal requirement into a predictable, automated workflow.
DORA and Architecting for Operational Resilience
The Digital Operational Resilience Act (DORA) mandates a shift in focus from incident prevention to ensuring the business can withstand and recover from operational disruptions. For engineering teams, this means resilience is a design constraint that must be continuously tested and verified.
DORA effectively makes chaos engineering a regulatory expectation. It is no longer sufficient to assume a system is resilient; organizations must proactively and systematically test its failure modes to prove it.
This requirement translates into specific engineering practices:
- Automated Resilience Testing: The CI/CD pipeline must include automated tests that simulate failure scenarios, such as network latency, API timeouts, or the complete failure of a dependent microservice in a pre-production environment.
- Immutable Infrastructure: Infrastructure as Code (IaC) tools like Terraform should be used to define and manage all environments. This ensures that the production infrastructure can be rebuilt quickly, consistently, and reliably from version-controlled code following a critical incident.
- Third-Party Risk Mitigation: DORA requires strict oversight of third-party dependencies, including cloud providers and API vendors. The system must be architected to handle their failures gracefully, using patterns like circuit breakers and fallbacks to prevent cascading failures.
Integrating these practices into the development lifecycle builds a system that is not just compliant on paper but is demonstrably resilient in operation, meeting the stringent demands of modern regulations for all mobile apps banking.
Designing Resilient Features and System Integrations
Features like real-time balances and instant transfers are defined by the reliability of the backend integrations that power them. The primary engineering challenge is not UI design, but architecting the secure, high-integrity communication between the mobile frontend and disparate backend systems.
In this distributed environment, transactional integrity is paramount. A naive implementation that directly exposes legacy systems via a thin API layer introduces risks of data inconsistency, poor performance, and operational failure. A robust architecture is designed for reliability and failure tolerance from the start.
API Design Patterns: REST vs. GraphQL
The choice of API design pattern has a direct impact on application performance, network efficiency, and developer productivity. The two predominant approaches, REST and GraphQL, offer distinct trade-offs.
-
REST (Representational State Transfer): As a long-standing industry standard, REST is structured and predictable, using resource-based endpoints (e.g.,
/accounts/{id}). Its primary drawback is the potential for “over-fetching” (receiving more data than necessary) or “under-fetching” (requiring multiple round-trips to populate a single view), which can degrade mobile performance. -
GraphQL: This newer pattern allows the mobile client to specify precisely the data it needs in a single query. A view that requires a user’s balance, recent transactions, and reward points might necessitate three separate REST calls. With GraphQL, this can be accomplished in a single request, reducing network latency and improving perceived performance.
This choice has significant architectural implications. GraphQL offers superior efficiency for data-intensive mobile interfaces but requires a more complex server-side implementation. REST provides simplicity and broad ecosystem support, making it a pragmatic choice for simpler interactions.
Integrating with Core Banking Systems
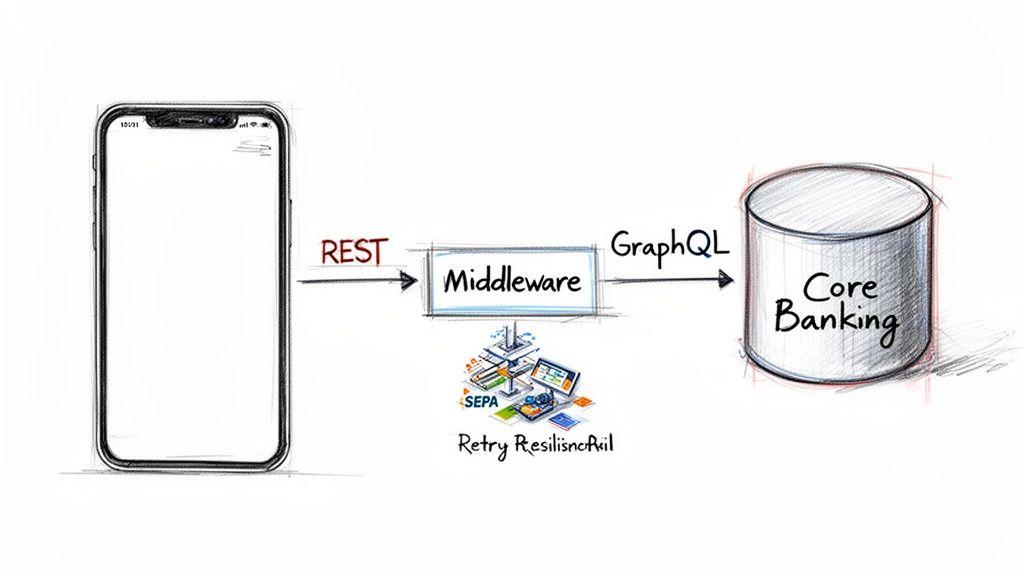
Connecting a modern mobile application to a legacy Core Banking System (CBS) is a significant engineering challenge. These monolithic systems were not designed for the performance or security demands of direct, real-time API access. A direct connection is often brittle, slow, and insecure.
The most effective architectural pattern is the introduction of an anti-corruption layer or middleware. This intermediary service acts as a translator and shock absorber, decoupling the agile mobile application from the rigid, slow-moving CBS.
This middleware performs several critical functions:
- Protocol Translation: It converts modern API calls (REST/GraphQL) into legacy formats the CBS can process (e.g., SOAP, file-based transfers).
- Data Transformation: It transforms data from complex CBS schemas into clean, mobile-optimized JSON payloads.
- Caching and Resilience: It caches frequently requested, non-sensitive data to reduce load on the CBS and implements patterns like the Circuit Breaker to handle CBS downtime without causing a cascading failure in the mobile app.
Connecting to External Payment Rails
A mobile banking app must integrate with external payment networks such as SEPA or Faster Payments. These integrations demand absolute transactional integrity to prevent financial loss from duplicate or failed transactions.
An idempotent API design is critical, ensuring that if the same request is sent multiple times due to network issues, the transaction is processed exactly once.
Furthermore, implementing distributed transaction patterns like the Saga pattern helps maintain data consistency across both internal microservices and external systems. This ensures that a multi-step process, such as a cross-border payment, either completes successfully across all participating systems or is safely rolled back, preventing data corruption.
Applying AI for Advanced Fraud Detection and Automation
Beyond conversational interfaces, applied AI provides powerful, practical tools for enhancing security and automating high-cost operational processes in mobile banking apps. This is not about speculative technology adoption but about leveraging mature machine learning (ML) to solve concrete business problems like fraud prevention and identity verification.
A common pitfall is integrating a generic third-party AI service without considering the architectural, data privacy, and model governance implications. A robust strategy requires a careful evaluation of the trade-offs between building proprietary models and integrating external AI services, based on the institution’s risk appetite, data assets, and long-term strategic goals.
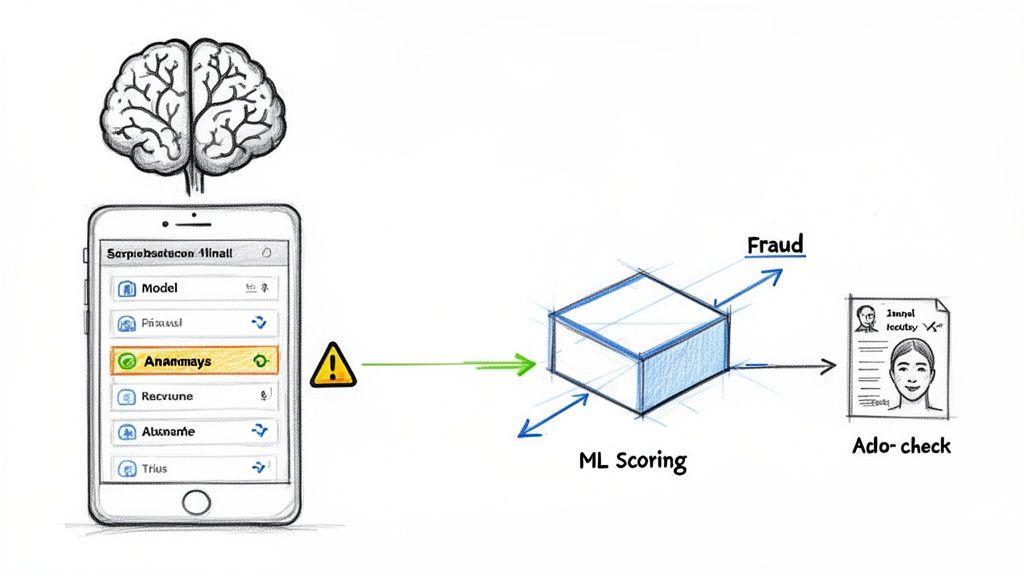
Real-Time Fraud Detection with Behavioral Analytics
Legacy, rule-based fraud detection systems are increasingly ineffective against sophisticated attacks. ML-based systems offer a more dynamic and adaptive approach, shifting from static “if-then” logic to pattern-based anomaly detection.
These systems establish a behavioral baseline for each user by analyzing a continuous stream of data points:
- Transactional Patterns: Typical transaction amounts, payees, and times of day.
- Device and Geolocation Data: The devices, IP addresses, and geographical locations from which a user normally operates.
- In-App Navigation: Biometric patterns based on how a user navigates and interacts with the application interface.
When a new action deviates significantly from this established baseline—such as a large transfer to an unknown beneficiary at an unusual time from a new device—the system can flag it in real time for immediate intervention, either by blocking the transaction or escalating it for manual review.
AI-Powered Identity Verification (ID&V) Automation
Customer onboarding is a security-critical and operationally intensive process. AI offers practical solutions to automate and strengthen ID&V workflows.
- Automated Document Processing: Computer vision models can scan and extract data from government-issued identity documents, verifying their authenticity and cross-referencing information against user-provided data.
- Liveness Detection: To prevent spoofing attacks using photos or videos, liveness checks require the user to perform a randomized action (e.g., turning their head) to prove they are physically present.
- Intelligent Automation: Modern Natural Language Processing (NLP) models can power chatbots to handle routine customer inquiries, freeing up human agents to focus on complex, high-value interactions.
Such automation is critical for scaling operations, particularly in high-growth markets. The Asia Pacific region, for example, is projected to have a mobile banking market of $0.44 billion by 2025, with a compound annual growth rate of 15.3%. Capturing this opportunity requires a platform that can scale onboarding and support securely and efficiently.
For technical leaders, the core decision is whether to build these AI models in-house or consume a third-party API. Building provides maximum control and customization but requires significant data science expertise and MLOps infrastructure. Using a third-party service offers faster time-to-market but creates vendor dependency and introduces data privacy considerations.
Evaluating these risks requires a structured approach. A formal assessment, such as a detailed AI Risk & Privacy Checklist, can help identify potential security, compliance, and governance gaps in your proposed architecture.
Conclusion: Key Takeaways for B2B Leaders
Developing a secure and resilient mobile banking application is a complex, multi-disciplinary engineering effort. For founders, CTOs, and product leaders, success depends on pragmatic, long-term architectural thinking. The quality of the final digital product is a direct reflection of the strategic decisions made before development begins.
A secure, compliant, and scalable application is the result of deliberate design choices that embed security and privacy as foundational, non-functional requirements. This is the essence of a privacy by design philosophy.
Core Architectural Principles
Navigating from concept to a market-leading product requires a clear understanding of the technical and regulatory landscape. Short-term optimizations that prioritize speed over stability invariably lead to unacceptable business risks, from data breaches to regulatory penalties.
Key takeaways include:
- Architecture is Strategy: The choice between native and cross-platform, or monolith and microservices, is a business decision that dictates future performance, scalability, and total cost of ownership.
- Compliance is Code: Regulations like GDPR and DORA must be translated into concrete engineering requirements, implemented through auditable architectural patterns and automated resilience testing.
- Security is Non-Negotiable: A defense-in-depth strategy is the only viable approach. This includes end-to-end encryption, certificate pinning, secure on-device storage, and robust code obfuscation.
Ultimately, building robust mobile banking apps requires a deep, practical understanding of modern software engineering, the regulatory environment, and the specific threat landscape of the financial sector. It is a system-level challenge that demands a holistic and expert-led approach.
Successfully executing this vision requires a technical partner capable of translating strategic objectives into a secure, compliant, and reliable digital product engineered for the long term.
At Devisia, we build reliable digital products and AI-enabled systems with a focus on pragmatic architecture and long-term maintainability. We provide the technical expertise to navigate these challenges and deliver real business value. Learn how we can help you build your next digital product.
