Means of Compliance (MOC) are the specific, tangible artifacts that prove your systems meet regulatory requirements. They are not bureaucratic paperwork, but the architectural blueprints, configuration files, and operational logs for your digital products. They demonstrate how abstract legal rules are met with concrete engineering evidence.
The Problem: Translating Legal Rules into Engineering Proof

For a CTO, product leader, or IT manager, regulations like GDPR, NIS2, and the EU AI Act present a significant challenge. These legal frameworks outline complex obligations but rarely specify the technical implementation details. This ambiguity creates a gap between legal requirements and engineering execution.
This is where the concept of Means of Compliance (MOC) becomes critical.
MOC are the collection of verifiable artifacts that translate legal obligations into engineering and operational reality. They provide the definitive answer to an auditor’s direct question: “How do you prove your system is compliant?”
The Risk of a Superficial “Checklist” Approach
A naive approach treats compliance as a pre-launch checklist. This often results in “shelfware”—documents and policies that look complete but fail to reflect the system’s actual, operational state. This creates a false sense of security and introduces significant business risk, as the documentation provides no real defense during an audit or security incident.
In contrast, a robust MOC strategy is built on tangible, living evidence integrated directly into the software development and operational lifecycle.
A well-architected MOC strategy delivers several practical benefits:
- Reduces Legal and Financial Risk: It provides defensible proof of due diligence, which is invaluable during a regulatory audit or in the aftermath of a security breach.
- Unlocks Commercial Opportunities: Demonstrating auditable compliance is often a prerequisite for securing enterprise B2B contracts. Customers require verified proof of a vendor’s security and privacy posture.
- Improves System Quality: Systems designed for auditable compliance are inherently more observable, maintainable, and resilient. This engineering discipline translates directly into a more valuable and robust asset.
In the current regulatory climate, authorities are shifting their focus from simple declarations of compliance to demanding verifiable proof. Your Means of Compliance are the primary evidence you will present.
From Administrative Burden to Architectural Principle
Effective MOC management requires treating compliance as an architectural concern, not an administrative task. This demands a shift in mindset: from asking “Are we compliant?” to “How do we demonstrate our compliance continuously and verifiably?”
This involves architecting systems that generate compliance evidence as a natural byproduct of their operation.
For example, instead of merely having a policy document describing data deletion, a strong MOC for GDPR’s “right to be forgotten” would include:
- An automated script that orchestrates the data erasure request across all relevant data stores.
- Immutable logs confirming that the script executed successfully for a specific user ID at a specific time.
- A system architecture diagram that clearly illustrates the end-to-end data deletion workflow.
This approach transforms compliance from a source of friction into a driver of quality engineering. It enables the construction of defensible, trustworthy, and genuinely valuable software systems.
Translating Compliance Theory Into Engineering Practice
Turning an abstract rule from a regulation like GDPR or NIS2 into a concrete engineering task is a core challenge for technical leadership. The solution is to deconstruct “compliance” into a set of specific, tangible artifacts.
These artifacts are your Means of Compliance (MOC). They are the evidence that proves your claims.
A strong MOC portfolio is not a static folder of documents. It is a living, version-controlled collection of evidence that covers your entire system—from high-level policy down to individual lines of code and log entries. The risk of “shelfware”—documentation disconnected from reality—is a primary cause of failed audits and a false sense of security.
The Anatomy of Strong Compliance Evidence
Effective Means of Compliance are specific, auditable, and directly traceable to a particular regulatory requirement. They replace vague assertions with verifiable proof.
A robust MOC portfolio typically includes a combination of documentation and technical outputs:
- Annotated System Architecture Diagrams: These are more than just blueprints. A MOC diagram highlights security controls, data encryption points, and sensitive data flows, with annotations explaining why specific design choices were made to meet compliance objectives.
- Data Flow Diagrams (DFDs): Essential for privacy compliance (e.g., GDPR). They map how personal data enters, moves through, and exits your system, proving you understand and control its lifecycle.
- Records of Processing Activities (ROPA): Required by GDPR, a ROPA is a detailed inventory of your data processing. It serves as a central index of what data you collect, the legal basis for processing, and who has access.
- Security Risk Assessments: These documents demonstrate due diligence. They identify potential threats to the system, assess their impact, and outline the specific technical and organizational controls implemented to mitigate them.
- Immutable Audit Logs: Perhaps the most powerful MOC. Immutable logs provide a timestamped, unchangeable record of critical system events, such as user logins, data access requests, or administrative configuration changes.
The difference between ‘compliance theatre’ and genuine compliance is the quality of the evidence. Good evidence is a natural byproduct of a well-architected system; poor evidence is typically scrambled together reactively before an audit.
Designing for Demonstrable Compliance
This reflects a core principle at Devisia: privacy and compliance are architectural choices, not features bolted on later. When you design systems for observability from the outset, generating and maintaining these MOCs becomes far simpler. A system architected to log its own actions generates its own proof.
You can find more details on this approach in our article on data protection and privacy by design.
The industry is rapidly standardizing on verifiable frameworks. According to A-LIGN’s 2025 Compliance Benchmark Report, 81% of organisations now hold or are pursuing ISO 27001 certification, a 14% year-over-year increase from 67% in 2024. This trend indicates a move toward risk-based frameworks to manage data privacy and security, particularly with the rise of AI. For startups and SMBs, this is a clear signal: prioritizing ISO 27001 is a practical step to winning enterprise contracts, as 42% of organisations now mandate SOC 2 or ISO certifications from their partners. Learn more about these compliance benchmark findings.
Mapping MOC Across GDPR, NIS2, and DORA
Collecting evidence is only half the battle. The real work lies in connecting that evidence directly to specific regulatory requirements. For tech companies in Europe, three regulations are paramount: GDPR, NIS2, and DORA.
Let’s map the Means of Compliance (MOC) for each, translating abstract legal text into concrete engineering and product deliverables.
GDPR: Proving Data Subject Rights
GDPR grants individuals specific rights over their personal data. A common challenge is proving compliance with the “right to erasure” (Article 17). An auditor will not accept a mere assertion; they require evidence.
The problem is not just deleting the data but proving, with verifiable artifacts, that a user’s data has been permanently removed from all systems, including production databases, backups, and third-party services.
A robust set of MOCs for this requirement would include:
- A Documented Data Deletion Workflow: A version-controlled diagram or document detailing each step of the process. It should specify which systems are affected, the sequence of operations, and the roles responsible.
- Technical Implementation Evidence: The actual code that performs the erasure. This could be the SQL scripts, the microservice endpoint definition, or the API calls that trigger the workflow.
- Immutable Database Logs: Verifiable logs are your strongest evidence. They must show that the deletion command for a specific user ID was executed successfully at a specific time. To be credible, these logs must be tamper-proof.
- Confirmation Records: A copy of the notification sent to the user confirming their request has been completed, which closes the loop for an audit trail.
Together, these artifacts create a complete, auditable trail from user request to final confirmation.
NIS2: Demonstrating Incident Handling Capabilities
The NIS2 Directive significantly raises the bar for cybersecurity, requiring organizations to prove they have effective incident handling capabilities. It’s not enough to simply have a plan; you must demonstrate that it works and that you learn from incidents.
The following diagram illustrates how different artifacts—policies, diagrams, and logs—interconnect to form a cohesive body of compliance evidence.
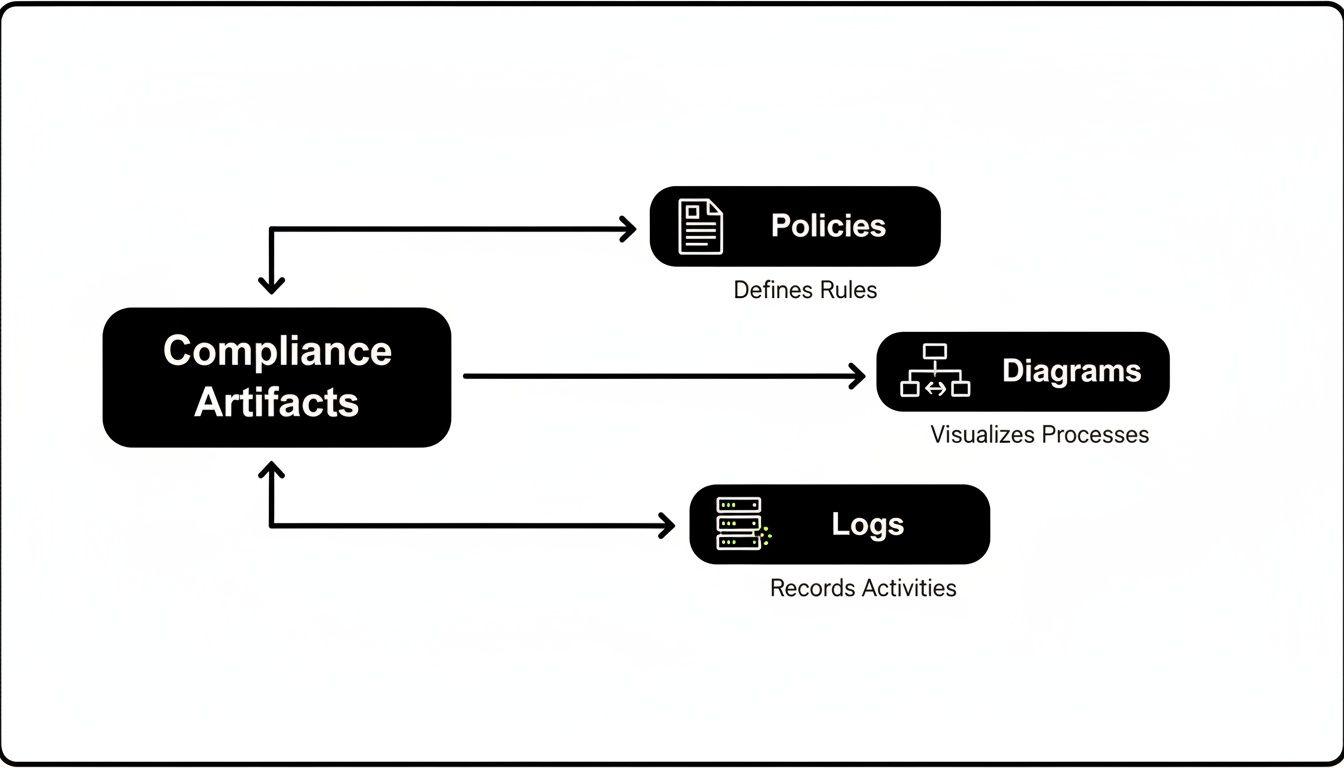
As shown, MOCs are not isolated documents. They are interconnected artifacts that, together, provide a complete narrative of your compliance posture.
To satisfy an auditor for NIS2, you need MOCs that prove your process is mature and tested:
- Incident Response Plan (IRP): A detailed, accessible document defining roles, communication channels, and step-by-step procedures for containment, eradication, recovery, and post-incident analysis.
- Simulation Exercise Reports: This is critical. You need documentation from tabletop exercises, purple-teaming, or red-team drills. These reports prove your IRP is a living document that your team has practiced using, not just “shelfware.”
- Post-Incident Analysis Documents: Following a real or simulated incident, a “lessons learned” or root cause analysis report is a crucial MOC. It demonstrates that you analyze incidents and take concrete steps to improve your defenses.
DORA: Evidencing Digital Operational Resilience
DORA targets the financial sector and its critical technology providers, demanding hard proof of digital operational resilience. This means showing that your systems can withstand, respond to, and recover from all types of ICT-related disruptions.
Under DORA, the burden of proof is on demonstrating resilience, not just claiming it. This requires a shift from reactive security to proactive, evidence-based risk management that covers your entire technology stack and supply chain.
Key MOCs for DORA focus on ICT risk management and third-party dependencies:
- ICT Risk Management Framework: A formal, board-approved document outlining how your organization identifies, assesses, and mitigates technology risks across its operations.
- Business Impact Analysis (BIA): Evidence that you have analyzed the impact of system failures. This analysis must identify critical business functions and define clear Recovery Time Objectives (RTOs) and Recovery Point Objectives (RPO). You might be interested in exploring the role of a Data Protection Officer and how they manage these risks under GDPR Art. 37.
- Third-Party Risk Assessment Records: Detailed due diligence records for every critical ICT supplier. This includes reviewing their security certifications (e.g., SOC 2), audit reports, and ensuring contracts contain specific clauses mandating security and resilience standards.
Architecting Systems for Built-In Compliance
Authentic compliance is not achieved through a last-minute scramble before an audit. It is an emergent property of a well-architected system. The most effective strategy for managing Means of Compliance (MOC) is to build systems where evidence is generated automatically as a byproduct of normal operations. This approach transforms compliance from a manual, error-prone process into an automated and trustworthy one.
When compliance is treated as an architectural pillar, long-term costs and operational friction are drastically reduced. If a system is built to be observable, proving its behavior to an auditor becomes a continuous, low-effort task. This is the difference between building compliance in versus bolting it on.
Patterns for Automated Evidence Collection
A few core architectural patterns provide the foundation for any system designed to produce its own MOC. Adopting them creates a portfolio of verifiable proof that is always current and reflects the system’s actual state.
This is a strategic response to increasing regulatory complexity. A recent report highlights that 21% of C-Suite executives will prioritize compliance in 2025—a massive jump from just 2% in 2024. With 61% of software firms now planning for AI audits and 69% of firms naming regulatory complexity as a major hurdle, building for auditable compliance is a clear competitive advantage. Discover more insights about these compliance statistics.
Here are key patterns for built-in compliance:
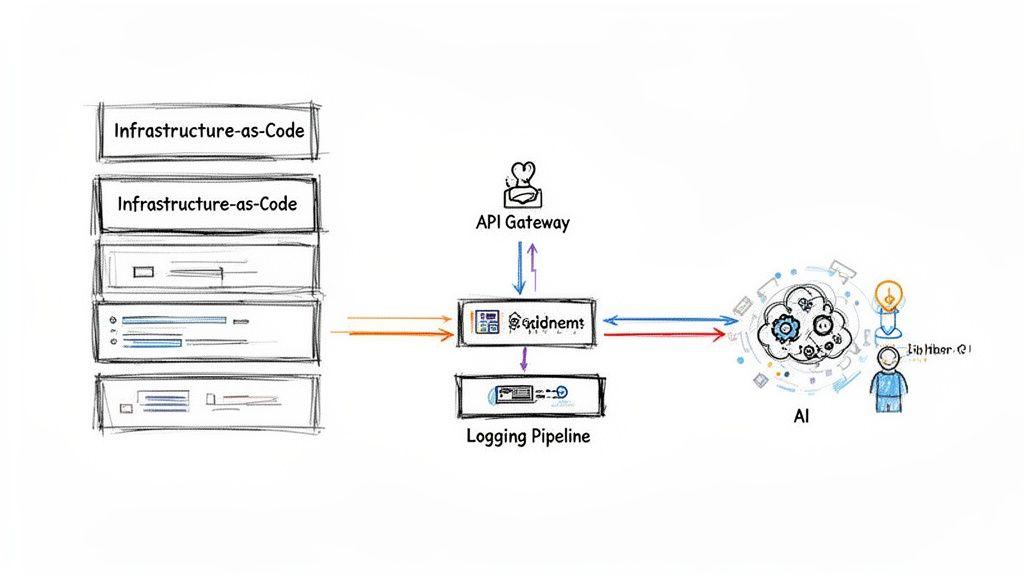
- Infrastructure-as-Code (IaC): Defining infrastructure using tools like Terraform or CloudFormation turns the code itself into a powerful MOC. These version-controlled, declarative files provide an auditable record of your environment’s configuration. An auditor can review the code to verify security settings, network rules, and access policies without needing access to a live system.
- Comprehensive and Immutable Logging: Every critical action—data access, permission changes, login attempts, deletion requests—must be logged. For these logs to serve as a reliable MOC, they must be immutable. Sending logs to a separate, write-once, read-many (WORM) storage service (like AWS S3 with Object Lock) creates an unchangeable audit trail that proves exactly what the system did and when.
- Centralized API Gateways: An API gateway acts as a single, controlled entry point for all data requests. By routing all traffic through it, you can enforce and log critical policies—such as authentication, authorization, and rate limiting—in one place. The gateway’s logs become a central ledger proving who accessed what data and under which policies.
Architectural Considerations for AI Systems
With AI, generating a MOC means making opaque, non-deterministic models more transparent and auditable. The system architecture must be designed specifically to provide this evidence.
For AI, compliance is about proving that you have established and can enforce clear boundaries for the model’s behaviour. Your architecture must be designed to monitor, constrain, and document its actions, transforming abstract “responsible AI” principles into concrete, verifiable controls.
Here are practical architectural patterns for building auditable AI systems:
- Explainability Hooks: Build API endpoints into your AI service that can be queried to provide reasoning for a model’s decision. For example, a loan application model should not just return “denied”; it should also expose the key features that contributed to that outcome. The logs from these queries become your MOC for algorithmic transparency.
- Guardrails and Policy Enforcement Layers: Implement a “guardrail” layer that intercepts both model inputs (prompts) and outputs. This layer can enforce hard rules, such as blocking requests containing personally identifiable information (PII) or preventing the model from generating harmful content. The logs from this guardrail prove that you have active controls in place to mitigate AI-specific risks.
- Logged Human-in-the-Loop (HITL) Workflows: For high-stakes decisions, design a workflow where an AI’s output is routed to a human for review before any action is taken. The system must log the entire process: the AI’s initial recommendation, the human reviewer’s identity, their final decision (and any overrides), and the timestamp. This creates an explicit audit trail demonstrating human oversight.
Common Compliance Pitfalls and How to Avoid Them

Creating documentation is not the same as achieving compliance. Many organizations treat Means of Compliance (MOC) as a box-ticking exercise, creating a dangerous gap between what is documented and what is actually running in production.
This superficial approach leads to predictable failures. The most common pitfall is the creation of “shelfware”—compliance documentation prepared for an audit, then filed away and forgotten. Because software systems are dynamic and constantly evolving, this static evidence becomes obsolete almost immediately. When an incident occurs or an auditor arrives, the discrepancy between the documentation and the live environment becomes a critical liability.
The Dangers of Compliance Theatre
This practice leads to “compliance theatre”: the appearance of security is prioritized over its actual implementation. Teams perform the motions of compliance, generating artifacts that look good on paper but lack substantive backing. For example, a policy may mandate quarterly access reviews, but when an auditor asks for proof, no logs or records exist to show they ever happened.
The consequences are severe:
- Failed Audits: Auditors are trained to find these gaps. If an MOC claims a control is in place but you cannot provide live, verifiable evidence of its operation, you will fail the audit.
- Increased Likelihood of Security Breaches: A documented control that was never implemented is a known vulnerability you have chosen not to address. The breach is often the first—and most expensive—indicator that your MOC was fiction.
- Erosion of Trust: Failing an audit or suffering a preventable breach because your evidence did not match reality irreparably damages your reputation with customers, partners, and regulators.
In practice, ‘compliance theatre’ is more than just a poor process; it’s a critical business failure. It creates a false sense of security that leaves an organisation exposed when a real-world test—like a targeted cyberattack or a surprise regulatory inspection—occurs.
Fostering Continuous and Authentic Compliance
To avoid these traps, compliance must be treated as a continuous, integrated process, not a one-time project. Authentic compliance is a living practice, not a static snapshot.
Integrate MOC into the Development Lifecycle Treat compliance evidence as a required deliverable for any significant system change. If a developer builds a new microservice that handles personal data, the updated Data Flow Diagram (DFD) and logging configurations must be part of the same pull request. This makes compliance a manageable, everyday engineering responsibility.
Conduct Regular Internal Reviews Do not wait for an external audit to test your MOC. Conduct your own internal reviews on a recurring schedule to validate your evidence against live systems. These self-audits should be as rigorous as an external one, simulating the questions an auditor would ask and actively searching for gaps.
This proactive approach ensures your evidence remains current and accurate. It transforms your means of compliance from a brittle artifact into a resilient, trustworthy asset that reflects the true state of your systems. This is how you transition from “compliance theatre” to genuine, demonstrable security.
Actionable Steps for Building Compliant Systems
Effective Means of Compliance are the tangible proof of a commitment to security and privacy. They are not created in a last-minute scramble but are the result of deliberate architectural choices and continuous, integrated processes. The core principle is that real compliance is built, not just documented. To move from “compliance theatre” to a state of provable, resilient security, technical leaders must embed these practices into their engineering culture.
Ultimately, your Means of Compliance portfolio tells a story. It should be a clear, consistent, and evidence-backed narrative of how your organisation protects its data, systems, and customers. A strong narrative builds trust and resilience, while a weak one invites risk and scrutiny.
A Pragmatic Roadmap to Demonstrable Compliance
For a CTO or product leader, the journey begins with small, concrete actions that build momentum. Instead of attempting a complete overhaul, focus on integrating these high-impact habits into your team’s daily workflow.
Here is a pragmatic roadmap for turning compliance theory into daily engineering practice:
- Map Critical Data Flows First: Your initial task should be to create or update Data Flow Diagrams (DFDs) for systems handling sensitive data. This visual evidence is a foundational MOC that identifies your highest-risk areas, allowing you to prioritize controls where they matter most.
- Make Security Logging a Core Requirement: For your next feature or sprint, include immutable, context-rich logging as a non-negotiable part of the “Definition of Done.” Ensure logs capture who did what, when, and to which data, creating an automatic audit trail.
- Automate One Manual Compliance Check: Identify a manual compliance task, such as verifying cloud security group configurations against a written policy, and automate it. This transforms a static document into a living, verifiable control and demonstrates a commitment to continuous compliance.
- Schedule Recurring Compliance Reviews: Book a quarterly meeting with engineering and product leads to review your MOCs against live systems. Treat it like a fire drill; ask challenging questions and identify gaps before an external auditor does.
- Build a Centralized Compliance Library: Establish a wiki or repository to organize your MOCs. Link policies, architectural diagrams, risk assessments, and audit logs together to create an accessible, interconnected evidence base for both internal teams and external auditors. You can learn more about managing these processes effectively in our guide to governance, risk, and compliance software.
Adopting these habits transforms compliance from a perceived burden into a strategic advantage, reinforcing the value of a knowledgeable partner in building reliable digital products.
Frequently Asked Questions About Means of Compliance
Implementing a structured approach to compliance raises practical questions, especially for fast-growing technology companies. This section provides direct, actionable answers to common challenges that technical leaders face when putting Means of Compliance (MOC) into practice.
How Can a Startup with Limited Resources Effectively Manage Means of Compliance?
The key is to start small and integrate compliance into the development process from day one. Do not aim for perfect compliance across multiple frameworks immediately. Instead, focus on high-impact controls that address your most significant risks. This incremental approach is manageable and demonstrates due diligence to auditors.
A practical first step is creating a Data Flow Diagram (DFD) to visualize how sensitive data moves through your system. From there, implement fundamental controls that offer the most security value:
- Robust Logging: Ensure critical system events are logged to a secure, tamper-evident location.
- Access Control: Enforce strict role-based access control (RBAC) for sensitive data and systems.
- Infrastructure-as-Code (IaC): Use tools like Terraform or CloudFormation. The code itself becomes a verifiable MOC for your environment’s configuration, proving how your infrastructure is built and secured.
Finally, prioritize documenting your most critical processes, such as your incident response plan or data deletion workflow. Auditors often value a clear, documented plan for continuous improvement more than a perfect but static compliance snapshot.
What Is the Difference Between Means of Compliance and a Certification?
They are related but distinct concepts. Means of Compliance are the specific, granular pieces of evidence—such as logs, configuration files, and policy documents—that you collect to prove a requirement is met. A certification, such as ISO 27001, is the formal attestation from an accredited auditor who has reviewed your collection of MOCs and confirmed that your overall management system meets the standard’s requirements.
Think of it this way: your Means of Compliance are the individual bricks, architectural plans, and inspection logs. The certification is the formal approval confirming that the entire house you built is solid and up to code.
For example, a server configuration script is an MOC that helps demonstrate a security control. An auditor would review that script, alongside many other MOCs, to verify that your entire information security management system (ISMS) meets the ISO 27001 standard.
How Does Privacy by Design Relate to Creating Means of Compliance?
Privacy by Design is an approach that makes creating and maintaining MOCs significantly simpler and more reliable. When you architect privacy controls into your software from the beginning, the evidence of compliance becomes a natural byproduct of the system’s operation, rather than a manual artifact created after the fact.
For instance, if you build a feature that automatically anonymizes user data after 30 days—a classic ‘Privacy by Design’ principle—the system logs that record this automated action become a powerful and effortless MOC for your data retention policy.
Without this design, you would be forced to implement a manual process, execute it periodically, and then document its completion. This manual approach is not only more labor-intensive but also prone to human error. By architecting for privacy, you build a system that generates its own compliance evidence, making your MOC portfolio more robust and easier to manage.
At Devisia, we believe that robust compliance is an outcome of pragmatic architecture and clear processes. We help companies build reliable digital products where security and privacy are inherent properties, not afterthoughts. Learn more about how we can help you build maintainable, evidence-backed systems at https://www.devisia.pro.
