GDPR Art 37 defines the mandatory appointment of a Data Protection Officer (DPO). For founders and technical leaders building SaaS or AI systems, this article is not just a compliance checkbox; it is a foundational component of your data governance architecture.
The DPO requirement is triggered for public authorities, or more critically for technology companies, when core business activities involve “large-scale, regular and systematic monitoring” of individuals or processing large volumes of sensitive data. Understanding this trigger is crucial for avoiding significant regulatory and business risk.
The Problem: When is a DPO Actually Mandatory?
Many founders and product leaders, particularly in startups and mid-sized companies, incorrectly assume the DPO role is only for large enterprises. This is a critical misunderstanding of the regulation. The trigger for appointing a DPO is not company size or revenue, but the nature and scale of its data processing activities.
Ignoring this obligation can result in fines of up to €10 million or 2% of global annual turnover, whichever is higher. For modern SaaS and AI products, the line between standard operations and “large-scale, systematic monitoring” is often blurred. Activities that are integral to product development and value creation frequently cross the GDPR threshold.
Consider if your company engages in any of the following:
- User Analytics: Tracking user behavior within your platform to refine features, drive engagement, or reduce churn.
- Personalized Services: Employing algorithms to deliver tailored content, recommendations, or experiences based on user activity.
- Location-Based Features: Processing geolocation data from user devices to provide a service.
- AI Model Training: Using large datasets of personal information to train or validate machine learning models.
If these activities are central to your product, you are likely operating in territory where a DPO is mandatory. This decision tree illustrates how core business activities can trigger the requirement.
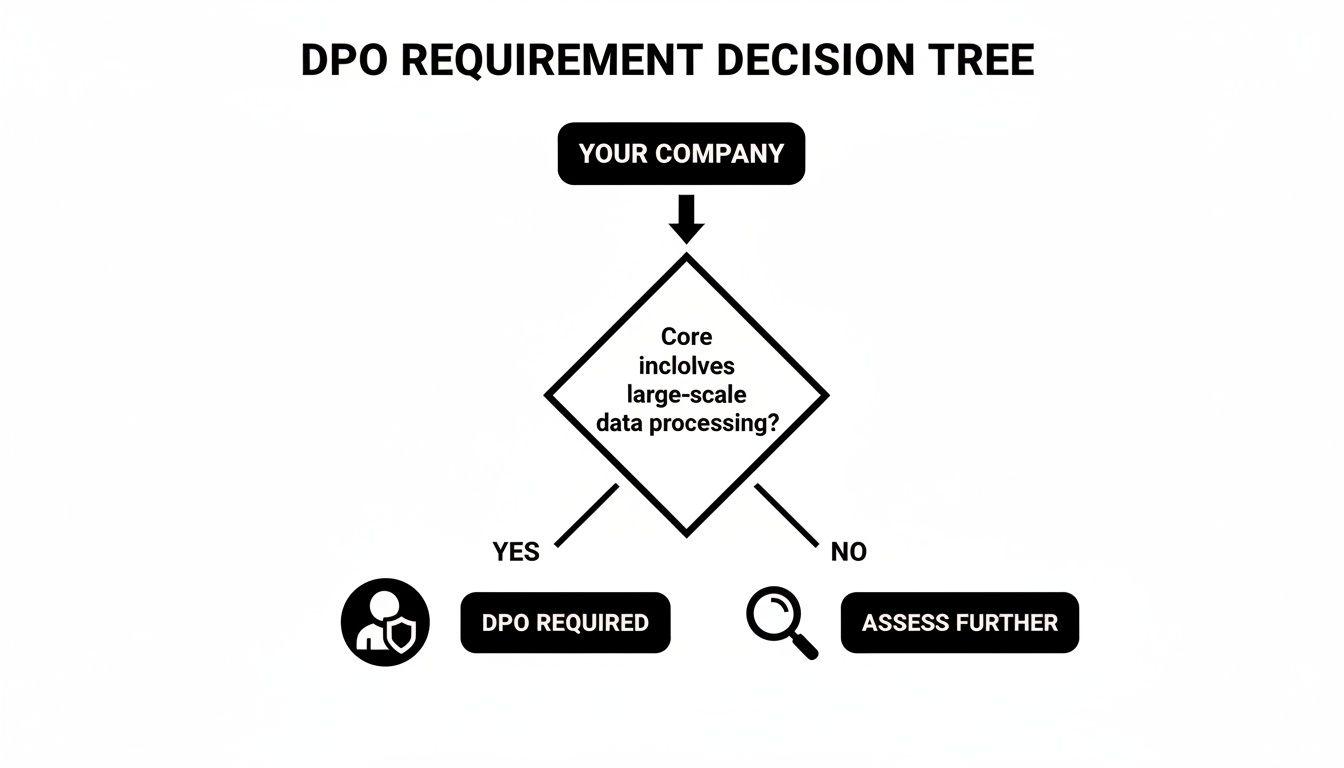
If data processing is inseparable from how your product delivers value, the question shifts from if you need a DPO to how you will architect the role.
A DPO is an Architect, Not a Compliance Checkbox
A common and dangerous misstep is treating the DPO as a mere administrative formality. A superficial approach, such as assigning the DPO title to a CTO or Head of Engineering, creates an immediate conflict of interest—a direct violation of Article 38. The individual responsible for building the product cannot be the same person independently overseeing its data protection compliance. This naive approach creates a fundamental weakness in your governance structure.
In a well-architected organization, the DPO functions as a strategic advisor, bridging the gap between dense legal requirements and real-world technical implementation. Their role is to ensure data protection is built into your systems by design, not bolted on as an afterthought. This approach is fundamental to building trust and ensuring the long-term viability of your product.
For technical leaders, understanding the DPO mandate in GDPR Art 37 is the first step toward building software that is robust, compliant, and trustworthy. To explore this architectural philosophy further, see our guide on how to implement GDPR privacy by design.
Decoding the Triggers for DPO Appointment
Determining if you need a Data Protection Officer (DPO) requires translating ambiguous legal phrases from GDPR Art 37 into concrete technical and business contexts. Many technology leaders misinterpret these triggers, assuming their company is too small or their data processing isn’t “risky” enough. This creates significant compliance gaps.
The central problem is that legal terms like “core activities” or “regular and systematic monitoring on a large scale” do not map directly to a tech stack or product feature. To assess your obligation correctly, you must analyze these triggers through the lens of your own software architecture and business model.
What Constitutes “Core Activities”?
The term “core activities” refers to the primary operations necessary to achieve your company’s principal objectives. It is about what your business does to create value, not secondary functions like payroll or internal IT support. If processing personal data is an inseparable part of your product’s functionality, it is a core activity.
For most SaaS and AI companies, this threshold is easily met.
- SaaS Platform: If a project management tool must process user-generated tasks, comments, and files to function, that data processing is a core activity.
- AI Product: If a system requires personal data to train models or deliver personalized outputs, that processing is fundamental. The product would not exist without it.
A common misinterpretation is to believe that because data processing merely supports a product, it isn’t a core activity. This is a false distinction. If the product is non-functional without the processing of personal data, then that processing is a core activity under GDPR Art 37.
Demystifying “Regular and Systematic Monitoring”
This trigger is where most modern technology companies are captured. It is a two-part criterion: the monitoring must be both “regular and systematic” and conducted on a “large scale.” Let’s deconstruct these with practical software examples.
“Regular and systematic” implies the monitoring is not a one-off or random event. It is planned, methodical, and an ongoing part of your operational model.
Consider these common scenarios:
- User Analytics in a SaaS Platform: Continuously tracking clicks, feature usage, and navigation paths to improve UX is systematic. It’s a planned, ongoing part of the product development lifecycle.
- Behavioral Profiling for AI: An AI model that personalizes content based on viewing history or in-app behavior is conducting regular monitoring. The tracking is constant and integral to the service.
- Location Data in Mobile Apps: An application using background location data for alerts or other services is performing systematic monitoring by design.
The term “large scale” is not defined with a precise number in the GDPR, but Recital 91 provides guidance. Factors include the volume of data, the number of data subjects, the geographical extent, and the duration of the processing. A B2B SaaS platform with thousands of users or an AI tool processing massive datasets will almost certainly meet the “large scale” threshold.
The costs of compliance governance, particularly mandates like Article 37, have tangible market effects. Research indicates that after GDPR’s implementation, European firms in data-intensive sectors saw profits decline by 8% and sales by 2%. The regulation steered companies, especially smaller B2B firms, away from radical innovation toward more incremental updates. These findings on GDPR’s market impact underscore that managing Article 37 compliance is not just a legal exercise; it is a strategic imperative to protect profitability and sustain innovation.
Architecting the DPO Function: Internal vs. External
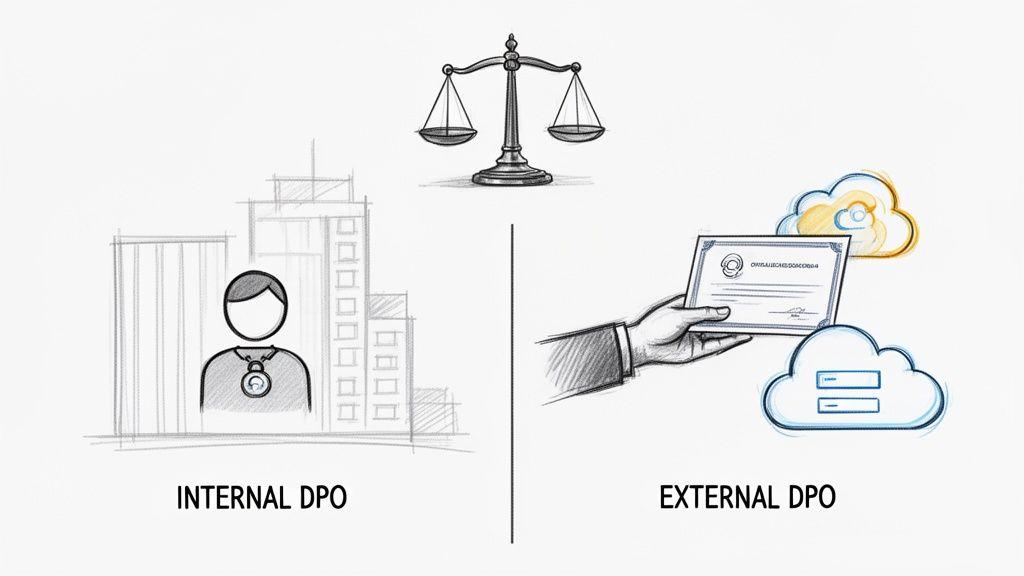
Once you determine a Data Protection Officer (DPO) is mandatory under GDPR Art 37, the next critical decision is an architectural one: how to structure the role. This choice is not merely an HR matter; it fundamentally shapes how data governance integrates with your engineering and product teams. The decision involves a trade-off between two primary models: an internal DPO or an external service (DPO-as-a-Service).
Neither model is inherently superior. The optimal choice depends on your organization’s scale, internal expertise, and risk appetite. It is a decision that requires a pragmatic assessment of the trade-offs involved.
The Internal DPO Model
The most direct approach is to appoint an internal DPO, either by hiring a dedicated expert or designating a qualified existing employee. The primary advantage is deep institutional knowledge. An internal DPO understands your company culture, products, and technical architecture, and already has relationships with key stakeholders in engineering, legal, and leadership. This proximity can accelerate decision-making and help embed privacy-by-design principles more naturally into your software development lifecycle (SDLC).
However, this model presents significant challenges and risks:
- Talent Scarcity: True data protection experts who also possess a deep understanding of modern software architecture are rare and command high salaries.
- The Conflict of Interest Trap: This is the most common failure point. Article 38 of the GDPR explicitly requires that the DPO operate without conflicts of interest. Appointing a CTO, Head of Security, or a lead engineer as DPO is a direct violation, as these roles determine how and why data is processed—the very activities a DPO must independently oversee.
- Resource Overhead: For smaller organizations, a full-time DPO represents a substantial financial commitment, potentially diverting budget from core product development.
An internal DPO must possess the authority and independence to challenge product roadmaps and architectural decisions without fear of reprisal. Their reporting line must go directly to the highest level of management, ensuring their independence is a functional reality, not just a line on an org chart.
The External DPO (DPO-as-a-Service) Model
The alternative is to contract a third-party firm or consultant to serve as your external DPO. This model, often called DPO-as-a-Service, provides access to specialized expertise on a fractional basis, which is often a more cost-effective and scalable solution for startups and SMBs.
External DPOs also offer a breadth of experience from serving multiple companies, providing valuable cross-industry perspectives. Their independence is structurally guaranteed, satisfying the conflict-of-interest requirement with minimal internal friction.
However, this model is not a simple “plug-and-play” solution. A superficial engagement is a major risk.
- Deep Integration is Essential: An external DPO cannot be effective as a distant advisor. They must be deeply integrated with your product and engineering teams, participating in planning meetings, reviewing Data Protection Impact Assessments (DPIAs), and understanding your technical stack.
- Knowledge Transfer: The DPO requires a direct line of communication and a commitment from your team to provide context on data flows, architecture, and processing activities. Without this, their advice will remain generic and ineffective.
- Availability Guarantees: Your service-level agreement (SLA) must guarantee the DPO’s availability when you need it most, particularly during a data breach or an urgent regulatory inquiry.
Comparison of Internal vs. External DPO Models
| Factor | Internal DPO | External DPO (DPO-as-a-Service) |
|---|---|---|
| Expertise | Deep knowledge of the company’s specific products and culture. May lack broader industry perspective. | Broad expertise from multiple clients and industries. May lack deep initial context about your business. |
| Cost | High fixed cost (full-time salary and benefits). Can be a significant burden for smaller companies. | Lower, predictable operational expense (retainer fee). More scalable and cost-effective for most SMBs. |
| Conflict of Interest | High risk. Must be carefully managed to ensure independence from roles that determine processing activities (e.g., CTO). | Low risk. Independence is structurally built-in, providing a clear separation of duties. |
| Availability & Integration | Fully available and integrated. Part of the team’s daily workflow. | Availability depends on the SLA. Requires deliberate effort to integrate into engineering and product workflows. |
| Scalability | Scaling expertise requires hiring more staff, which can be slow and expensive. | Can scale up or down quickly based on business needs, such as during a new product launch or M&A activity. |
Ultimately, the objective is not merely to have a DPO, but to have an effective one. The optimal model is the one that provides your organization with independent, expert advice that is deeply integrated with the teams building your products.
The DPO’s Mandate: Beyond Designation
Merely appointing a Data Protection Officer (DPO) to satisfy GDPR Art 37 is insufficient. The true measure of compliance lies in how the role is empowered and integrated into the organization, as mandated by Articles 38 and 39. A DPO who exists only on paper is a significant liability, not a compliance asset. They must be an active, hands-on partner in your operations. This requires moving beyond a reactive, “check-the-box” mentality and embedding the DPO function directly into core business processes, particularly the software development lifecycle (SDLC).
Proper and Timely Involvement in Workflows
Article 38 demands that the DPO be involved “properly and in a timely manner” in all issues relating to the protection of personal data. For a SaaS or AI company, this has profound architectural implications. It means the DPO’s input is required long before code is deployed. This proactive involvement must begin at the earliest stages of the development cycle.
- Planning Phase: The DPO should participate in privacy-by-design workshops, helping architects and product managers identify potential data risks in new features before they are fully scoped.
- Development Phase: They must be available to advise engineering teams on the practical implementation of data minimization, pseudonymization, and other privacy-enhancing techniques.
- Review Phase: A core function is to review Data Protection Impact Assessments (DPIAs) for high-risk processing activities. This requires a combination of legal acumen and technical depth. Learn more about conducting a privacy impact assessment for your projects.
This level of integration ensures data protection becomes an architectural principle from day one, not a frantic remediation effort later. A DPO who only sees a new feature after it is built cannot perform their duties effectively.
The Specific Tasks of a DPO under Article 39
Article 39 provides a non-exhaustive list of the DPO’s minimum tasks, reinforcing their role as an active advisor and monitor, not just a passive contact point.
The DPO’s core function is to independently monitor compliance and advise on risk. They act as a critical internal control mechanism, providing objective feedback to the highest level of management on whether the organisation’s data processing activities align with GDPR requirements.
This mandate translates into several key duties:
- Informing and Advising: The DPO must educate all stakeholders—from the board to junior developers—on their GDPR obligations. This includes developing training materials and fostering ongoing awareness programs.
- Monitoring Compliance: This is an active, not passive, role. The DPO is responsible for auditing internal adherence to GDPR, including reviewing how responsibilities are assigned, assessing staff training, and conducting internal process audits.
- Advising on DPIAs: They provide expert advice on whether a DPIA is necessary, how to conduct it, and whether its conclusions are sound.
- Cooperating with Supervisory Authorities: The DPO serves as the official point of contact for data protection authorities and must cooperate with any inquiries or investigations.
These tasks require that the DPO be provided with sufficient resources, authority, and unrestricted access to all data processing operations. Failure to provide this support effectively nullifies their appointment and exposes the organization to significant risk.
Practical Steps to Implement the DPO Function
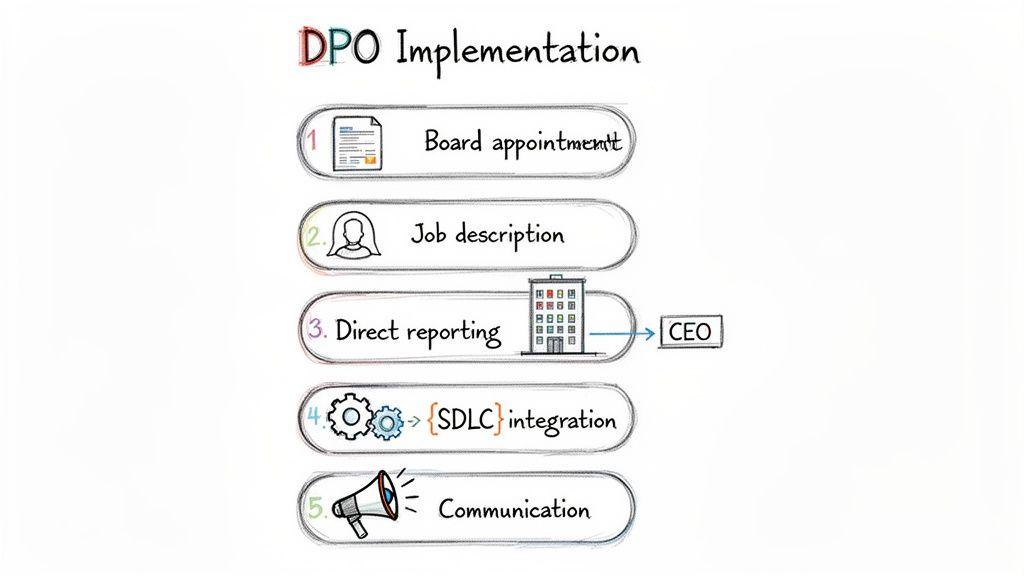
Moving from the theory of GDPR Art 37 to operational reality is a common stumbling block. Appointing a Data Protection Officer (DPO) is not just an HR task; it is a deep architectural and operational decision. For CTOs and compliance managers, the objective is to build a function that genuinely reduces risk and informs engineering decisions, not to create a “paper DPO” for compliance theater.
A superficial appointment—assigning the title without real authority or resources—creates a false sense of security that will crumble under regulatory scrutiny. These steps provide a pragmatic path to building a DPO function that is both compliant and effective.
1. Formalize the Appointment
The DPO’s designation cannot be a casual handshake. It must be an official, documented decision made at the highest level of management, ideally recorded in a board resolution or equivalent executive decision. This formal record serves two purposes: it provides evidence to auditors that you take compliance seriously, and it signals to the entire organization that the DPO has the full backing of leadership.
2. Craft a Conflict-Free Job Description
The job description is your primary tool for defining the DPO’s mandate and, critically, preventing the conflicts of interest forbidden by Article 38. It must map directly to the tasks outlined in Article 39. The most dangerous mistake is adding “DPO” to an existing executive’s title, such as CTO or Head of Marketing, whose roles involve determining the means and purposes of data processing.
Your job description should codify the DPO’s independence. Use this as a starting point:
- Core Responsibility: To inform and advise the company, from the board to development teams, on its GDPR obligations.
- Primary Task: To independently monitor internal compliance with GDPR and other data protection laws, including conducting internal audits.
- Key Function: To advise on Data Protection Impact Assessments (DPIAs), including their methodology and outcomes.
- External Role: To serve as the point of contact for supervisory authorities and data subjects.
- Reporting: To report directly to the highest level of management (e.g., the board or CEO).
3. Establish a Direct Reporting Line
A DPO is rendered ineffective if their assessments are filtered through layers of management. Article 38 is unequivocal: the DPO “shall directly report to the highest management level.” This is a structural requirement, not a suggestion. This direct line ensures the DPO’s unvarnished assessments of risk and compliance gaps reach those with the power to act. In practice, this means the DPO must have regular, direct access to the CEO or executive board.
4. Integrate the DPO into Key Workflows
An effective DPO cannot operate from an isolated compliance silo. They must be woven into the workflows where data decisions are made.
Key integration points include:
- Software Development Lifecycle (SDLC): Involve the DPO early, during privacy-by-design workshops and feature planning, before code is written.
- Change Management: Any significant change to systems, architecture, or vendors that affects personal data requires DPO review.
- Incident Response: The DPO must be a core member of your incident response team to guide breach notification obligations under Articles 33 and 34.
- Vendor Risk Management: The DPO should review and advise on third-party contracts, particularly the Data Processing Agreement, to ensure they meet GDPR standards.
5. Communicate the Role and Mandate
Finally, everyone in the company—from engineering to sales—must understand who the DPO is, what their function is, and why they must be consulted on relevant projects. Clear communication prevents the DPO from being perceived as a blocker and positions them as an essential guide for building secure and compliant systems.
The High Cost of DPO Non-Compliance
For a company building SaaS or AI products, the risk of failing to comply with GDPR Art 37 extends far beyond the steep fines. The true damage is the operational disruption, reputational harm, and loss of investor confidence that follow a regulatory enforcement action. Viewing the DPO appointment as an administrative task to be deferred is a strategic miscalculation that exposes the business to severe and lasting consequences.
Reputational Damage and Customer Churn
In B2B software, trust is the product. A public compliance failure, especially one as fundamental as neglecting the DPO requirement, signals to customers that you are not serious about data governance. Your compliance gap becomes their business risk. This leads to heightened scrutiny from their legal teams, difficult contract renewals, and ultimately, customer churn.
The moment a supervisory authority announces an investigation for an Article 37 breach, you lose control of the narrative. You are no longer perceived as a trusted partner but as a potential liability—a reputation that is incredibly difficult to repair.
Operational Disruption and Investor Scrutiny
Data protection authorities have the power to do more than just issue fines. They can impose corrective measures, such as an order to temporarily or permanently cease data processing activities. Imagine being forced to suspend service for all EU customers until compliance is demonstrated. The operational chaos and revenue loss would be immediate and catastrophic.
This level of disruption is a major red flag for investors and financial partners.
- For Startups: A regulatory investigation can derail a funding round. Due diligence will uncover the compliance failure, flagging it as an unacceptable legal and operational risk.
- For Established Companies: An enforcement order can trigger default clauses in loan agreements or investment terms, creating a financial crisis that threatens the entire business.
Since GDPR became enforceable on May 25, 2018, regulators have been active. By December 2023, authorities had issued over 2,100 GDPR fines totaling €4.4 billion, demonstrating the seriousness with which they enforce requirements like Article 37. This enforcement history makes it clear that for any business with users in the EU, the cost of robust data governance is simply the cost of doing business. You can find more details on GDPR Article 37 compliance and its enforcement.
Failing to appoint a DPO when required is not a simple oversight; it is a structural flaw. It reveals a reactive, short-term approach to risk that invites painful enforcement actions and erodes the trust your business is built upon. Proactive compliance is not an expense; it is an investment in your company’s resilience and long-term viability.
Answering Your Questions on GDPR Art 37 and the DPO Role
When it comes to GDPR Art 37, theory is one thing, but practical application is another. Tech leaders often run into the same critical questions. Here are the straight answers.
Can our CTO or Head of Security also be the DPO?
No. This is the single most common and dangerous mistake a company can make. The GDPR is unambiguous: a Data Protection Officer (DPO) must be free from any conflict of interest.
A CTO, Head of Security, or any role that defines the purposes and means of data processing—in other words, decides why and how data gets used—cannot also be the DPO. The DPO’s job is to independently monitor and challenge the very systems they would be responsible for building. Appointing your CTO as DPO isn’t just a bad idea; it’s a direct violation of Article 38.
We’re a small startup. Do we really need a DPO?
Company size is irrelevant. Your data processing activities are everything. A small startup absolutely might need a DPO if its core activities involve large-scale, regular, and systematic monitoring of individuals.
Think about a small ad-tech company or a SaaS product with a powerful user analytics feature. Even with just a few employees, the product itself can easily trigger the DPO requirement under GDPR Art 37. The regulation focuses on the scale and risk of the processing, not your headcount.
How do cloud providers affect our DPO requirement?
Using cloud providers like AWS or Google Cloud doesn’t change your DPO obligation one bit. While they are data processors with their own massive compliance teams, you remain the data controller.
As the controller, you are the one on the hook for the data you process on their services. The decision to appoint a DPO is based on your company’s activities, not your vendor’s. Their infrastructure is just the place where your core activities happen.
What’s the first step if we need a DPO but don’t have one?
If you realise you meet the criteria but haven’t appointed a DPO, the first step is to act immediately. And document everything. Don’t wait.
- Conduct an internal assessment to formally document why a DPO is needed, linking it directly to your specific data processing activities.
- Inform your leadership or board about the compliance gap and the urgent need to fill the role.
- Start the designation process. This could mean opening a job requisition for an internal DPO or vetting external DPO-as-a-Service providers.
Taking these documented steps immediately shows a commitment to fixing the problem. That can be a powerful mitigating factor if a supervisory authority ever comes knocking.
Building robust, compliant software is an architectural choice. At Devisia, we partner with companies to turn business vision into reliable digital products and AI systems, with privacy and long-term maintainability built in from day one. Learn how we deliver meaningful, secure software at https://www.devisia.pro.
