When you hear “governance, risk, and compliance software,” or GRC software, it’s easy to tune out. The term sounds like it belongs in a boardroom, not a technical stand-up. But for CTOs, product leaders, and engineering managers, GRC software is a critical tool for translating abstract rules into concrete, auditable technical systems.
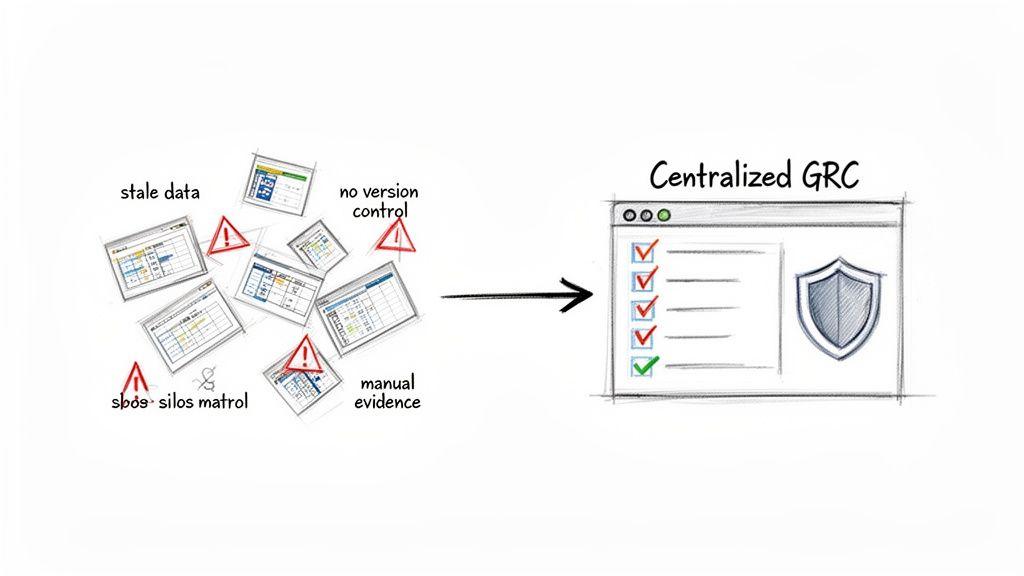
The core problem is that without a systematic approach, compliance work fragments into spreadsheets, disconnected documents, and endless email threads. This isn’t just inefficient; it creates significant operational risk. A GRC platform provides the solution: a structured system to manage this complexity, moving governance from manual chaos to automated control.
An Architectural Definition of GRC Software
For engineers and product managers, GRC software is often presented as a monolithic business solution, wrapped in marketing jargon. A more pragmatic, architectural definition is far more useful: GRC software is a system for operationalising business rules, policies, and controls across an organisation’s technical architecture.
Think of it like a CI/CD pipeline, but for governance. Instead of deploying code, you are deploying, testing, and monitoring the policies and controls that govern your systems.
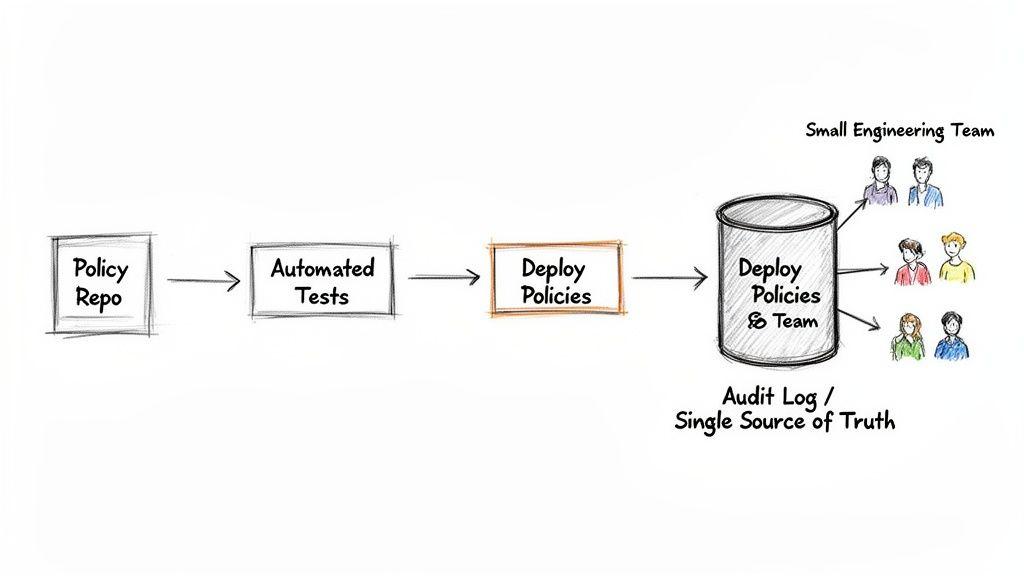
This framing is important. It turns GRC from a passive reporting tool into an active architectural component, connecting high-level policy to the specific technical controls that engineering teams build and maintain.
The Problem: Disconnected Systems and Manual Toil
Without a central system, governance work quickly degrades into a chaotic mess of spreadsheets, shared documents, and endless email chains. This isn’t just inefficient; it’s a critical architectural flaw. Data goes stale, version control is nonexistent, and audit preparation becomes a frantic, manual fire drill that pulls senior engineers away from value-generating work.
A dedicated GRC platform creates a single source of truth. It translates dense regulations like GDPR, NIS2, or DORA into structured data, mapping them to the specific systems, controls, and owners responsible for implementation. This creates a clear, auditable trail from policy to proof.
This structured approach is a foundational element for scaling operations responsibly, especially in regulated industries like finance or healthcare. It’s about building a reliable digital product, not just a functional one.
Key Functions for Technical Teams
From a practical standpoint, a GRC platform offers several critical functions that directly benefit engineering and product teams. It gives you a framework for managing risks tied to new features, third-party services, or changing regulations—proactively, not reactively.
An effective GRC platform helps your teams:
- Automate Evidence Collection: Instead of manually grabbing screenshots or exporting logs, the platform integrates with your tech stack—AWS, Azure, Jira, GitHub—to gather proof of compliance automatically.
- Streamline Audits: When auditors arrive, the evidence is already organised, linked to the relevant controls, and stored centrally. This dramatically cuts down the time engineers spend pulled away from product development.
- Standardise Risk Assessments: The platform enforces a consistent methodology for evaluating risk. This ensures every team uses the same criteria and language to describe, measure, and prioritise threats, from a code vulnerability to a third-party dependency.
- Improve Visibility: Dashboards provide a real-time view of your compliance posture, flagging control gaps or emerging risks before they turn into critical incidents.
Ultimately, GRC software is an architectural choice that supports long-term resilience and maintainability. For more on the regulatory drivers behind this need, you can explore our article on the EU’s Data Governance Act.
What’s Inside a GRC Platform? Core Architectural Capabilities
While the concept of a “single source of truth” is useful, its real value is realised through its specific functions. A modern governance, risk, and compliance software platform isn’t a monolithic application; it’s a collection of integrated modules that translate high-level policies into trackable actions for engineering and product teams.

For any technical leader, understanding these core pillars is critical for selection and implementation. The goal is to adopt a GRC framework that enhances engineering workflows, rather than hindering them. Each module addresses a specific part of the governance lifecycle, and their integration is what prevents a regression to spreadsheet-driven chaos.
Let’s break down the primary modules and their practical implications for technical teams.
| GRC Capability | Core Function | Impact on Engineering & Product Teams |
|---|---|---|
| Governance & Policy Management | Centralises all internal policies and external regulations. Manages versions, owners, and links policies to technical controls. | Provides a definitive source for all rules. Eliminates ambiguity and searching through wikis for the latest data handling policy. |
| Risk Management | Creates a structured process to identify, assess, and mitigate risks, from infrastructure vulnerabilities to data privacy concerns. | Transforms risk assessment from subjective guesswork into a quantifiable process. Helps prioritise technical debt or security patches based on measured impact. |
| Compliance Management | Maps technical controls to specific legal and industry requirements (like GDPR or ISO 27001). Automates evidence collection. | Ends the repetitive, manual work of proving compliance. A single security control can be mapped to satisfy multiple audit requirements. |
| Audit Management | Streamlines the entire audit process, from planning and evidence gathering to tracking remediation of findings. | Drastically reduces the time engineers are diverted to support audits. Evidence is pre-organised and readily available, not buried in logs or screenshots. |
| Vendor Risk Management | Extends the internal risk framework to third-party suppliers, from SaaS tools to cloud providers and open-source libraries. | Ensures that a new API integration or marketing tool doesn’t introduce an unacceptable security vulnerability. Creates a repeatable process for vetting dependencies. |
These capabilities are not abstract business concepts; they have a direct and practical impact on how your teams build and operate software.
Governance and Policy Management
This is the foundation. The governance and policy management module acts as the definitive repository for all internal policies, external regulations, and industry standards. More than a file store, it’s a structured database where policies are version-controlled, assigned owners, and linked directly to the technical controls that enforce them.
For a software organisation, this is where you connect an internal data encryption policy to a specific architectural implementation. For example, a rule stating “all PII at rest must be encrypted” can be tied directly to the AWS RDS configuration that enforces it, creating a clear, traceable line from policy to proof. For a deeper look at this structured approach, see our guide on choosing a document management system.
Risk Management
The risk management module transforms risk assessment from a gut-feel exercise into a systematic, data-driven process. It provides a framework for identifying, assessing, and treating risks across the entire technology landscape—from macro-level business threats to a specific vulnerability in a software dependency.
A strong risk register enables you to measure risk with consistent metrics (like likelihood and impact), assign remediation tasks to the right teams, and track mitigation efforts. This moves risk management from a periodic, check-the-box activity to a continuous, proactive discipline integrated into your development lifecycle.
For a CTO, this provides an objective basis for decision-making. When a team proposes using a new open-source library, the risk module provides a standard workflow to evaluate its security posture, license compliance, and potential impact on the system.
Compliance Management
This is where policy and risk converge to demonstrate that you are operating as designed. The compliance management module maps your technical controls to the specific requirements of regulations like GDPR, DORA, or ISO 27001. It automates the painful, manual task of showing that your technical safeguards meet your legal and contractual obligations.
Consider a practical engineering scenario:
- Mapping Controls to Regulations: A GRC platform can map a single control, like your user authentication service, to multiple requirements across GDPR (Article 32), PCI DSS, and SOC 2 simultaneously. This “test once, satisfy many” approach eliminates enormous amounts of redundant work.
- Automating Evidence Collection: Instead of asking engineers for screenshots to prove a setting is correct, the system can connect to your cloud provider’s API and automatically pull evidence that security groups are configured as required. This creates an audit trail without manual intervention.
Audit and Vendor Risk Management
The audit management module reduces the friction of internal and external audits. It helps you plan audits, manage fieldwork, track findings, and ensure remediation plans are executed. For auditors, it provides a single, organised portal to review controls and evidence, accelerating the entire process.
Similarly, vendor risk management extends your governance framework to your supply chain. It provides workflows to assess the security and compliance of third-party vendors—be it a new SaaS marketing tool or a critical cloud provider. This is essential for preventing a vulnerability in a third-party service from becoming your next security incident.
Why Spreadsheets and Silos Are an Architectural Anti-Pattern
For many growing tech companies, the initial approach to governance and compliance is a familiar patchwork of tools: spreadsheets for risk tracking, shared drives for policies, and email threads for audit management. This feels pragmatic at first—it’s low-cost and uses existing tools.
However, this approach is not free. It is a form of technical debt that becomes exponentially more expensive to remediate as the organisation scales.
The fundamental problem is that these disconnected tools create information silos. The risk register in a spreadsheet has no connection to the compliance checklist in another document or the audit findings buried in an old email. This fragmentation creates massive, often invisible, risks that only surface during a crisis or a high-stakes audit.
The Cascade Effect of Manual GRC
Consider a common scenario: a software team must comply with a new data residency requirement under GDPR. In a manual GRC world, this triggers a flurry of disconnected activity. Someone updates a policy document, emails the new rule to engineering leads, and starts tracking implementation in a spreadsheet.
Months later, an auditor asks for proof. The compliance manager finds the spreadsheet is outdated. The engineer who implemented the control has left the company, and no documented evidence links the policy to the actual technical configuration. A minor task has escalated into a major compliance gap, requiring an all-hands fire drill to find evidence.
This is the default reality for teams relying on manual processes. The most dangerous risks of this approach are:
- Data Staleness: Information in a spreadsheet is outdated the moment it’s entered. You never have a real-time view of your risk posture, only a static snapshot.
- No Version Control: With multiple editors, it’s nearly impossible to track changes, maintain a clean audit trail, or determine who approved what.
- Manual Evidence Collection: Constantly interrupting engineers to request screenshots or log exports is a significant productivity drain and a source of friction between teams.
- Inability to Correlate Data: You cannot see how a risk flagged by one team impacts a compliance obligation owned by another. Critical connections are missed until it’s too late.
The Business Case for Centralisation
Transitioning from spreadsheets to dedicated governance risk and compliance software is a strategic investment in business resilience. A centralised GRC system provides a single, reliable source of truth where policies, risks, controls, and evidence are interconnected, delivering measurable value.
By automating control monitoring and evidence collection, a GRC platform fundamentally changes the audit dynamic. Instead of a reactive scramble, audits become a planned, predictable process based on continuously updated data. This dramatically reduces preparation time and the associated costs.
This shift is occurring globally, especially in fast-growing IT markets. Rapid digitalisation and stricter regulations are fueling GRC adoption. For example, in some regions, 49% of organisations have moved off spreadsheets to automated GRC tools. These platforms deliver up to 53% better accuracy in compliance reporting and help unify cybersecurity controls—a critical need as 58% of GRC solutions now embed cyber risk modules. You can see how GRC software adoption is surging in high-growth IT regions for more data.
For a CTO or product leader, the ROI is clear. It’s measured in reduced audit fees, faster compliance cycles, and fewer hours wasted by your most valuable resources—your engineers. Most importantly, it delivers accurate, real-time risk data, which is non-negotiable for making sound technical and business decisions.
How to Select GRC Software: An Architect’s Checklist
Choosing a governance, risk, and compliance (GRC) software platform is a critical architectural decision. It is easy to be distracted by polished dashboards and long feature lists, but the true test is how well the solution integrates with your existing engineering ecosystem and workflows.
A tool that looks impressive but forces teams into manual data entry or context switching will quickly become expensive shelfware. The right GRC software should feel like a natural extension of your tech stack, not a bolted-on compliance chore. A naive selection based on license fee ignores the total cost of ownership (TCO), which includes engineering hours for integration, ongoing maintenance, and lost productivity from inefficient processes.
1. Prioritise API-First Design
For any modern GRC platform, an API-first architecture is non-negotiable. This means the software was designed around its API from the start, ensuring that every function available in the UI is also programmatically accessible. This is the key to unlocking the custom integrations and automated workflows that deliver real value.
When evaluating a solution, ask pointed questions about its API:
- Completeness: Is every feature, including reporting and user management, exposed via the API? Or are there gaps that will force you back into manual work?
- Documentation Quality: Is the API documentation clear, comprehensive, and well-maintained? Poor documentation is a major red flag for future integration challenges.
- Authentication and Rate Limits: Does it use modern authentication standards like OAuth 2.0? Are the rate limits practical for your automation needs?
An API-first approach allows you to adapt the tool to your processes, not the other way around. It is the foundation for treating GRC as code.
2. Scrutinise Automation and Integration Capabilities
The core promise of GRC software is to eliminate manual toil. Your selection criteria should be heavily weighted toward the platform’s ability to automate evidence collection directly from your technical environment. The goal is to make compliance a continuous, automated background process, not a periodic fire drill.
Look for native integrations with the tools your engineering teams use daily:
- Cloud Providers: Direct connectors for AWS, Azure, and GCP are table stakes. The tool should automatically monitor configurations like IAM roles, security groups, and encryption settings.
- Development Tools: Integrations with Jira, GitHub, or GitLab let you link compliance tasks and risks directly to development tickets and code commits, creating a seamless audit trail.
- Security Scanners: The platform must be able to ingest findings from vulnerability scanners and static analysis tools to centralise risk management and track remediation.
A platform’s true strength is measured by its ability to gather proof without human intervention. If a vendor’s answer to evidence collection is “just use our spreadsheet import feature,” it’s a clear sign their tool will perpetuate manual work, not eliminate it.
3. Assess Configurability and Workflow Matching
Finally, the best GRC software is highly configurable. Your organisation has its own unique risk appetite, compliance workflows, and reporting needs. A one-size-fits-all solution will invariably create friction.
Assess how easily you can customise risk assessment matrices, control frameworks, and approval workflows without extensive custom code. This is especially critical for companies with specialised regulatory demands or those building novel AI systems that require bespoke governance models. The platform must be flexible enough to adapt as your business and the regulatory landscape evolve.
True configurability empowers you to build a GRC system that is a precise fit for your operational reality, ensuring it gets used and delivers long-term value.
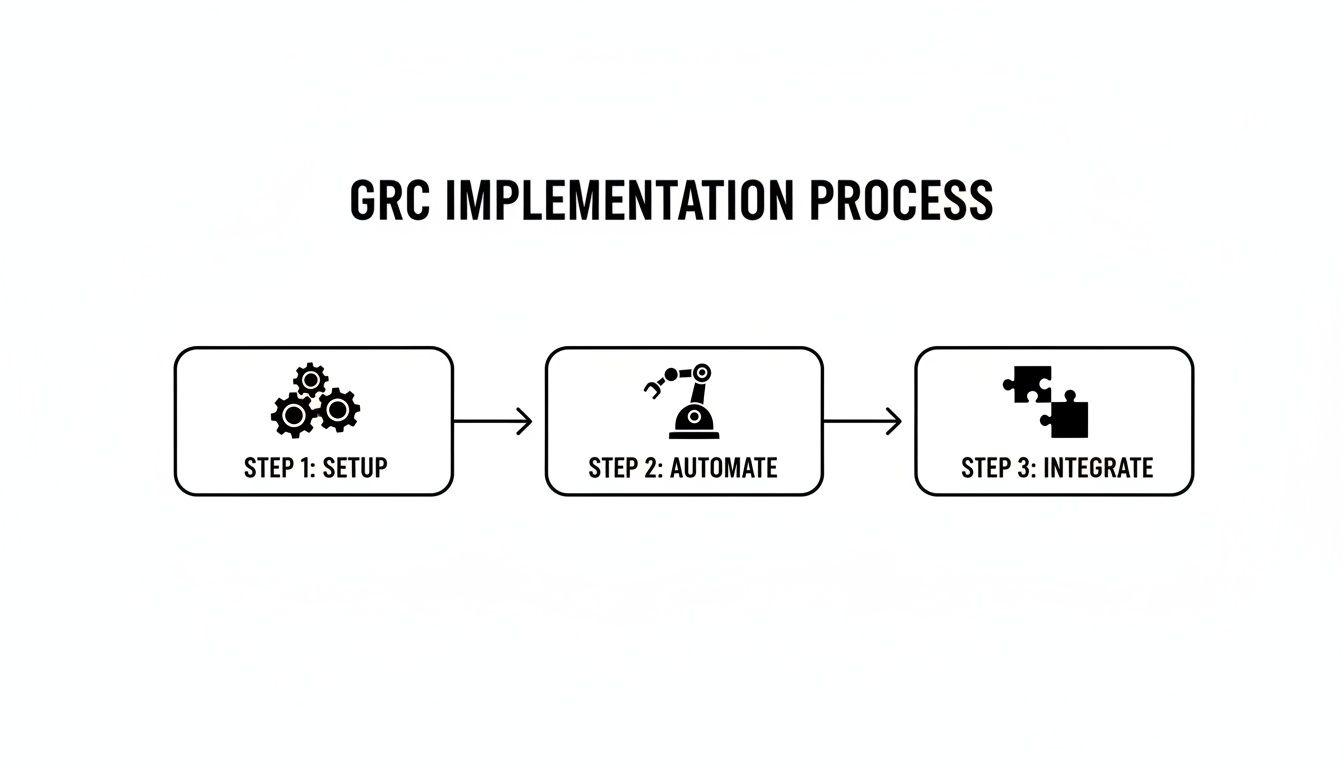
A Phased Roadmap for GRC Implementation
Rolling out governance risk and compliance software is not a “big bang” event. Attempting to solve every governance issue at once is a classic recipe for failure, creating overwhelming complexity, frustrating engineering teams, and stalling the project before it delivers any value.
A pragmatic approach mirrors modern software development: implement in clear phases, deliver incrementally, and secure buy-in at each step. By starting with a high-impact area, you can demonstrate value quickly, build momentum, and refine your process before scaling across the organisation.
Phase 1: Core Setup and Policy Centralisation
The first phase is about building a solid foundation. The goal is to get core governance documents out of scattered folders and into a single, structured repository within the GRC platform. This isn’t just an upload-and-forget exercise; it’s about mapping the relationships between policies, their owners, and the business units they affect.
Select one area where the operational pain is high and a quick win is achievable. Good candidates include:
- GDPR Compliance: Map your data protection policies to GDPR articles and link them to the systems processing personal data.
- Vendor Risk Management: Formalise how you onboard and assess third-party tools, especially those touching sensitive customer information.
- ISO 27001 Preparation: Begin documenting your security controls and mapping them against the standard’s requirements.
By focusing on a single domain, you can achieve a quick, visible win. Centralising policies creates immediate clarity and establishes the GRC platform as the single source of truth, ending the chaos of conflicting document versions.
This phase also establishes reusable patterns for future rollouts. Involving key stakeholders, such as a Program Management Officer drives strategic initiatives, ensures alignment with broader business goals.
Phase 2: Automated Control Monitoring and Risk Assessment
With a central policy foundation in place, the next phase is to bring it to life with automation. This involves connecting your governance risk and compliance software to your live technical environment to actively reduce the manual burden on engineering teams.
For example, instead of asking an engineer for a screenshot to prove a database is encrypted, you configure the GRC tool to query your cloud provider’s API directly. The tool checks the configuration and records the evidence automatically, creating a reliable audit trail with zero human effort.
The North American IT sector, holding a 41% global share of the GRC market, has seen significant gains here. By automating routine checks, firms have reduced manual audit efforts by an average of 46%, freeing up critical engineering time. You can learn more about how North American IT firms leverage GRC automation to manage complex regulatory demands.
Phase 3: Advanced Integrations and AI Governance
The final phase transforms the GRC platform into the central nervous system for all risk and compliance activities. This means building deeper integrations and preparing for emerging challenges like AI governance.
Common architectural patterns in this phase include:
- Webhook-Based Notifications: Configure the GRC platform to send real-time alerts to tools like Slack or Microsoft Teams when a high-priority risk is identified or a control fails.
- Custom Connectors: Build bespoke integrations for your proprietary internal systems, ensuring no part of your tech stack operates outside the governance framework.
- CI/CD Pipeline Integration: Embed GRC checks directly into your deployment pipeline. For example, a pipeline could query the GRC tool to confirm a new service has an approved risk assessment before allowing a production deployment.
This phased journey transforms GRC implementation from a monolithic, high-risk project into a manageable, value-driven process.
Measuring Success and Avoiding Common Pitfalls
Adopting governance risk and compliance software is a significant architectural commitment. Its success should not be measured by a vague feeling of being “more organised,” but by concrete metrics that matter to engineering and product leaders.
A successful GRC implementation reduces friction and creates tangible value. A poor one adds another layer of bureaucracy. The litmus test is simple: does the system reduce manual work, improve visibility, and strengthen your risk posture?
Defining and Measuring Success
To justify the investment, track metrics that tie directly to engineering efficiency and risk reduction. Focus on KPIs that tell a real story:
- Time to Audit Readiness: How many engineering hours are spent preparing for an audit? A successful implementation should dramatically reduce this number through automated, continuous evidence collection.
- Percentage of Automated Controls: Track the ratio of technical controls monitored automatically versus manually. This is a direct measure of reduced engineering toil and should increase over time.
- Mean Time to Remediate (MTTR) for Control Failures: How quickly can your team detect and fix a compliance issue, such as a misconfigured security group? An integrated GRC tool should significantly shrink this cycle time.
Conversely, avoid vanity metrics like “number of risks logged” or “policies in the system.” These figures are easily gamed and say nothing about whether the organisation is safer or more efficient.
Common Implementation Pitfalls and How to Avoid Them
Even the best tool will fail if the implementation is flawed. Most mistakes are predictable and stem from treating GRC as a one-time project instead of an ongoing operational discipline.
This process flow shows the core stages of a healthy, iterative implementation.
The key insight is that setup, automation, and integration are not a linear sequence but continuous, overlapping activities that must be revisited. Knowing the common pitfalls is the best way to steer clear.
GRC Implementation Pitfalls and Mitigation Strategies
| Common Pitfall | Description of Risk | Mitigation Strategy |
|---|---|---|
| Treating GRC as a One-Off Project | The biggest mistake is viewing GRC adoption as a task with a start and end date. Compliance is never “done.” Regulations change, architectures evolve, and new risks emerge constantly. | Adopt a continuous improvement mindset. Treat your GRC platform like any other critical software—it needs ongoing maintenance, refinement, and regular reviews to identify new automation opportunities. |
| Neglecting Engineering Buy-In | If engineers see the GRC tool as a top-down mandate that creates more work, they will resist it. Without their active support, meaningful automation and integration into core dev workflows is impossible. | Involve engineers from day one. Frame the GRC platform as a tool to reduce their toil and shield them from audit distractions. Give them ownership of automating controls and connecting the platform to their CI/CD pipeline. |
| Choosing a Tool That Fights Your Architecture | A GRC solution with a poor API, few integrations, or a rigid structure is a recipe for failure. It will force your teams into manual workarounds, defeating the purpose of the investment. | Prioritise API-first design and proven integrations during selection. Run a proof-of-concept (PoC) to confirm the tool can connect to your critical systems (cloud provider, code repos, security scanners) and adapt to your workflows. |
Anticipating these pitfalls enables you to build a GRC practice that strengthens your organisation instead of merely checking a box.
Frequently Asked Questions About GRC Software
It’s natural for technical and product leaders to be sceptical about governance, risk, and compliance software. An investment of this scale must deliver real-world value that justifies the cost and effort. Here are straightforward answers to common questions.
Can We Build a GRC System In-House?
The build-versus-buy decision is common, but building a GRC system in-house is a trap for most organisations. You are not just creating a few workflows on a database; you are committing to building and perpetually maintaining a complex product that must keep pace with a flood of new regulations like DORA and NIS2.
A homegrown system means your team owns the entire lifecycle, including:
- A Content Library: Constantly tracking, interpreting, and updating dozens of legal frameworks and industry standards. This is a full-time job.
- Workflow Engine Maintenance: The logic for risk assessments, control tests, and audit trails requires continuous refinement as your business evolves.
- Integration Development: Building and maintaining connectors to your entire tech stack (cloud platforms, security scanners, CI/CD pipelines) is a massive, ongoing engineering cost.
Buying a GRC solution offloads this maintenance burden. You trade some level of bespoke customisation for a platform that is kept current by dedicated experts. The real choice is about strategic focus: do you want your engineers building compliance software or your core product?
How Does GRC Software Integrate with Our Tech Stack?
Modern GRC platforms are designed to be connected, not isolated. A strong, API-first architecture should be a non-negotiable selection criterion. The goal is to weave the GRC platform into your existing engineering fabric.
Common integration points include:
- CI/CD Pipelines: Configure your pipeline to query the GRC tool, for example, to block a deployment if a service has not completed its mandatory risk assessment.
- Security Tools: The platform can ingest findings from vulnerability scanners and static analysis tools, centralising security risks and creating auditable remediation tasks within the GRC framework.
- Cloud Providers (AWS, Azure, GCP): This is where automation delivers immense value. The GRC tool can query cloud APIs to verify security group rules, encryption settings, and IAM policies, turning manual evidence gathering into an automated, continuous process.
This transforms GRC from a passive reporting tool into an active, operational part of your infrastructure.
What Is a Typical Implementation Timeline?
A “big bang” rollout is a recipe for failure. A successful GRC implementation is a phased journey. For a mid-sized tech company, a realistic timeline unfolds over several months:
- Months 1-2 (Phase 1): Start small. Focus on a single, high-impact area like Vendor Risk Management or GDPR compliance. Use this phase to set up core policies, define initial workflows, and train key stakeholders.
- Months 3-5 (Phase 2): Prove the value of automation. Connect the platform to your primary cloud provider and one or two key security tools. This demonstrates the power of automated evidence collection and builds momentum.
- Months 6+ (Phase 3): Expand and deepen. Roll the platform out to other business units and build more advanced integrations, such as connecting it to your CI/CD pipeline or internal service catalogues.
This incremental approach delivers value quickly, facilitates adoption, and ensures the platform solves the problems it was intended to address.
At Devisia, we believe that robust governance is an architectural choice, not an afterthought. We help companies build reliable digital products and AI-enabled systems with maintainability and compliance built in from day one. If you’re looking to turn your business vision into a resilient and scalable software solution, explore how we can help at https://www.devisia.pro.
