A Data Protection Manager is not another compliance role. They are the operational leader responsible for translating a company’s data protection strategy into reality, ensuring that both software and business processes comply with regulations like the GDPR.
This role is fundamentally different from a lawyer or a pure compliance officer. A capable Data Protection Manager translates complex legal text into concrete technical and operational controls that product and engineering teams can implement.
Why a Data Protection Manager Is a Strategic Hire
As companies race to adopt AI and navigate complex regulations, data protection has become a core component of product development and business strategy, not just an IT or legal checklist.
For founders, CTOs, and product leaders, operating without a dedicated Data Protection Manager creates significant, often underestimated, business risks. The problem is that a reactive, superficial approach to privacy exposes an organization to threats that go far beyond regulatory fines.
The Risks of Privacy as an Afterthought
Treating data protection as a feature to be “bolted on” later creates massive architectural debt and operational friction. When privacy isn’t integrated from the start, engineers are forced into costly, inefficient retrofits. This is especially painful for modern systems like SaaS platforms and AI-driven products, where data handling is central to their function.
The risks of this naive approach include:
- Financial Penalties: Regulations like GDPR, NIS2, and DORA carry significant fines for non-compliance, which can be crippling for a growing business.
- Reputational Harm: A data breach or privacy failure can destroy customer trust, damage your brand, and create a significant advantage for competitors.
- Architectural Debt: Building systems without a privacy by design mindset leads to brittle, complex code that is difficult to maintain and scale securely.
- Blocked Innovation: Without clear guidance, product teams become hesitant. They either avoid leveraging data for fear of breaking rules or push forward recklessly, creating future liabilities.
A Data Protection Manager bridges the gap between legal theory and engineering reality. They don’t just enforce rules; they enable teams to build robust, trustworthy, and compliant software by making privacy an architectural choice.
Ultimately, a proactive Data Protection Manager is critical for building maintainable software and navigating AI governance. They become a strategic partner, ensuring growth is built on a foundation of trust and resilience, turning a potential liability into a competitive advantage.
What a Modern DPM Actually Does
Forget the outdated image of a compliance manager buried in legal documents. A modern Data Protection Manager (DPM) is an operational leader who works directly with the technical teams building and shipping software. Their role is not just to interpret rules but to translate abstract privacy requirements into concrete engineering tasks and system designs.
They act as the bridge between legal theory and technical implementation, ensuring privacy is built into the architecture from day one. While a Data Protection Officer role (DPO) often requires independence for oversight and reporting, the DPM is hands-on, guiding engineers and product managers through the practical complexities of data handling.
Core Responsibilities of a Data Protection Manager
The DPM’s impact spans from high-level strategy to daily execution. They are responsible for creating the data protection playbook and ensuring it is followed on the ground.
This table breaks down their duties, showing the connection between long-term goals and day-to-day product development.
| Area of Focus | Strategic Responsibilities (Long-Term) | Tactical Responsibilities (Day-to-Day) |
|---|---|---|
| Product Development | Establishing Privacy-by-Design principles and integrating them into the software development lifecycle (SDLC). | Conducting Data Protection Impact Assessments (DPIAs) for new features or AI models. |
| Data Governance | Developing and maintaining the company’s overall data protection policy and records of processing activities (RoPA). | Managing and executing Data Subject Requests (DSRs) for access, deletion, or rectification. |
| Risk Management | Creating a risk management framework to identify, assess, and mitigate privacy risks across the organization. | Leading incident response for data breaches, including investigation, mitigation, and regulatory reporting. |
| Team Enablement | Designing and delivering ongoing training for engineering, product, and support teams on data handling best practices. | Acting as the go-to consultant for teams with questions on data handling, consent mechanisms, and architectural choices. |
This blend of strategy and tactics makes the DPM an indispensable partner for technical leadership.
The Financial and Growth Implications
The market recognizes the DPM’s value, especially for professionals who understand AI governance. This is no longer a cost center; it is a strategic business role, and salaries reflect this reality. An effective DPM not only prevents fines but also builds customer trust and enables engineering teams to innovate safely.
A DPM’s value is measured not just by risks avoided but by innovation enabled. By providing clear guardrails, they empower teams to build ambitious features with confidence, knowing data protection is handled correctly from the start.
A 2022 analysis of GDPR-related job trends from PECB, using data from major job platforms, revealed that roles blending privacy with AI command significantly higher salaries, with a median over $169,700. The U.S. Bureau of Labor Statistics projects a 15% growth for related management roles through 2034, signaling that this expertise is becoming a fundamental business requirement.
Integrating the DPM with Product and Engineering Teams
A common mistake is isolating the Data Protection Manager (DPM) in a compliance department. When the DPM is viewed as a gatekeeper, development teams either slow down waiting for approvals or build around them, creating hidden risks.
To build resilient and trustworthy products, the DPM must be embedded directly into the software development lifecycle. This transforms the DPM from a source of friction into a strategic enabler. By participating in agile ceremonies, they offer real-time guidance, ensuring data protection is treated as a core architectural requirement. This approach prevents expensive rework and gives teams the confidence to innovate securely.
The objective is to shift the conversation from “Can we do this?” to “How do we implement this correctly?” An integrated DPM doesn’t just block projects; they help translate complex legal requirements into actionable engineering tasks, identify pragmatic trade-offs, and design systems that are both compliant and effective.
A Blueprint for Collaboration
Effective integration requires clear communication channels and defined touchpoints within your existing development workflow. This ensures privacy remains a continuous conversation, not a last-minute checklist.
Key integration points should include:
- Sprint Planning & Backlog Refinement: The DPM identifies features requiring a Data Protection Impact Assessment (DPIA) early, flagging user stories that involve new personal data or processing activities.
- Architectural Reviews: They provide input on data flows, storage mechanisms, and access controls, ensuring designs adhere to privacy-by-design principles before code is written.
- Feature Kick-offs: The DPM joins initial discussions to clarify data minimization requirements, consent models, and retention policies, turning legal ambiguity into concrete technical constraints.
This workflow illustrates the core cycle of a DPM’s collaboration with technical teams.
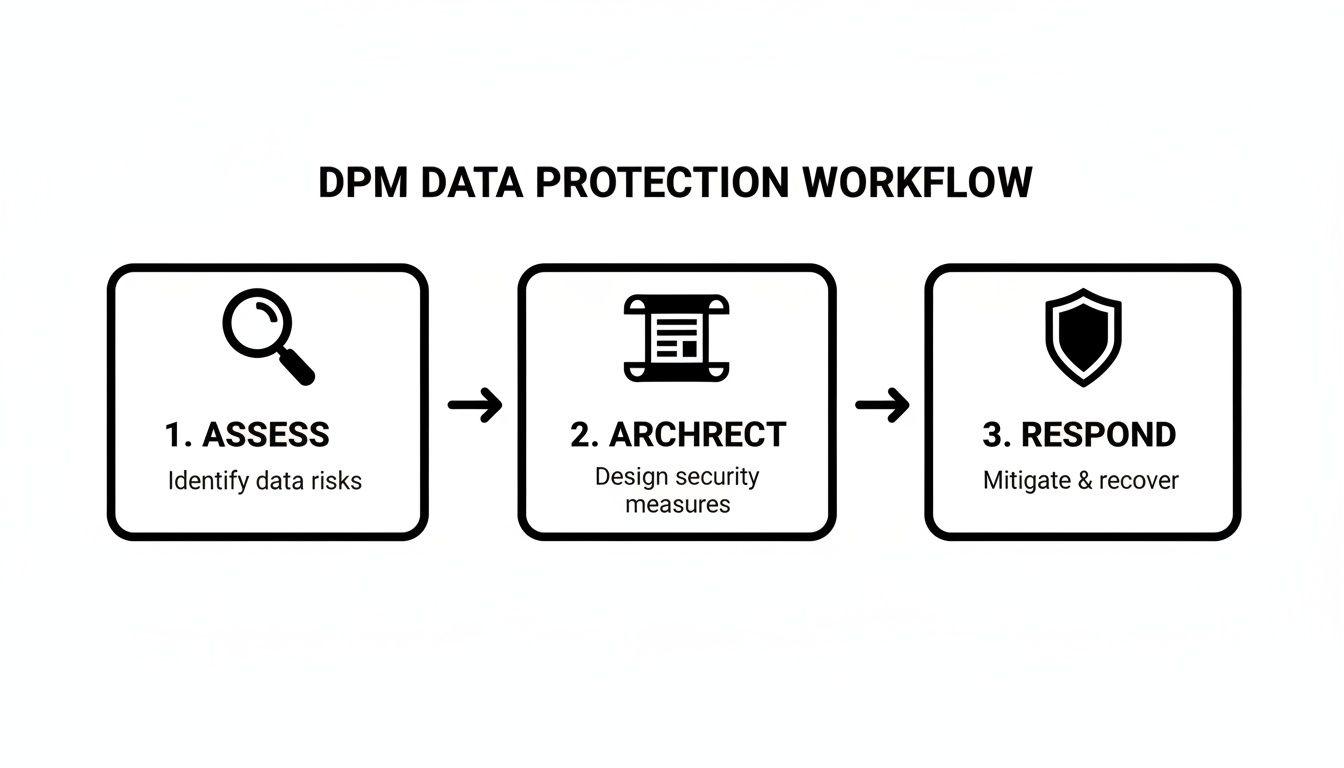
This is a continuous loop where the DPM helps teams assess privacy risks, architect robust solutions, and prepare to respond to incidents.
Real-World Scenario: Guiding an AI Feature Implementation
Imagine a SaaS company wants to build an AI feature that analyzes customer content to provide personalized recommendations. A product team operating without guidance might be tempted to collect all available data for model training, creating a privacy minefield.
An integrated DPM guides the team through a more rigorous process:
- Assess: The DPM initiates a DPIA. They ask critical questions: What specific data is absolutely necessary for the model? Can we pseudonymize it before training? What are the risks of model bias or user re-identification?
- Architect: Instead of blocking the project, the DPM partners with engineers to find a solution. They might suggest using federated learning to train models on-device or help design a system that uses a separate, anonymized dataset for training. The product goal is achieved while protecting user privacy.
- Implement & Respond: The DPM helps the product team draft clear, transparent language for user consent and updates the privacy policy. They also work with the operations team to establish monitoring for the AI system and create an incident response plan for data-related issues.
In this scenario, the Data Protection Manager is not a blocker but a strategic enabler. They provide the architectural guardrails that allow the team to build a powerful, competitive, and trustworthy AI feature without jeopardizing the company’s reputation.
How the DPM Manages AI Governance and Risk
 As AI becomes integral to business operations, the Data Protection Manager (DPM) faces complex new challenges. Adopting generative AI without a robust governance framework is not just a compliance issue; it’s a significant business risk.
As AI becomes integral to business operations, the Data Protection Manager (DPM) faces complex new challenges. Adopting generative AI without a robust governance framework is not just a compliance issue; it’s a significant business risk.
The DPM ensures the organization uses AI responsibly, not merely to check a legal box but to build products that earn customer trust. This requires moving beyond surface-level policy checks into the technical details of AI systems, assessing risks associated with Large Language Models (LLMs), vector embeddings, and the data used for fine-tuning.
This shift has created strong demand for privacy professionals with technical AI expertise. Data from Indeed’s career insights page shows that the average salary for a Data Protection Specialist in the US is $126,258 per year, with top earners in tech hubs like Atlanta reaching $226,728 annually.
Evaluating AI Data Sources and Lifecycles
A DPM’s first task in AI governance is to scrutinize the data pipeline. Teams often use large, unvetted datasets to train models, creating risks of data leakage, copyright infringement, and embedded bias.
The DPM challenges this practice by asking critical questions:
- Data Provenance: Where did the training data for this pre-trained model originate? Do we have the legal basis to use our customer data for fine-tuning?
- Data Minimization: Are we using the absolute minimum personal data required for the task, or are we over-collecting?
- Transparency and Documentation: Can we trace and document the entire data lifecycle—from collection to its use in a model’s output—to satisfy regulatory scrutiny?
A DPM’s role is to ensure the data fueling your AI is as clean and compliant as the code running it. They turn abstract ethical principles into concrete engineering requirements, ensuring your AI systems are not just powerful but legally defensible.
Balancing Performance with Privacy
There is often a trade-off between an AI model’s performance and its privacy safeguards. More data may yield better results, but it also increases risk. A pragmatic DPM helps teams navigate these trade-offs, preventing them from chasing performance at all costs.
For instance, they might champion the use of Privacy-Enhancing Technologies (PETs), such as differential privacy or federated learning. They also ensure systems include a reliable human-in-the-loop (HITL) process to review sensitive outputs, correct model errors, and prevent harmful automated decisions.
By documenting these controls and the rationale behind them, the DPM builds an audit trail that demonstrates due diligence. For technical teams implementing these controls, our AI Risk & Privacy Checklist offers a structured framework for assessing and managing these specific risks. This proactive approach helps AI projects achieve their goals without creating legal or reputational liabilities.
How to Hire Your First Data Protection Manager
Hiring your first Data Protection Manager (DPM) is a foundational decision for any tech company. You are not just filling a compliance gap; you are bringing in a strategic partner who will influence your product architecture and risk posture for years.
The ideal candidate for a technology-driven environment is a pragmatist with deep technical literacy. You need someone who thinks like an engineer but communicates effectively with business stakeholders.
Crafting the Right Job Description
A generic job description attracts generic candidates. Signal that you are looking for a hands-on technical partner, not a rule-enforcer. Frame the role around enabling secure innovation.
Focus on what the role does, not just what it knows:
- Technical Collaboration: Emphasize experience working directly within agile or DevOps teams, mentioning sprint planning and architectural reviews.
- Risk Assessment: Require real-world skill in conducting Data Protection Impact Assessments (DPIAs), especially for new software features and AI models.
- Privacy-by-Design: Ask for specific examples of implementing privacy-enhancing techniques in production systems.
- Pragmatic Mindset: Use language that reflects an appreciation for a business-aware approach—finding practical trade-offs rather than simply saying “no.”
Key Interview Questions to Ask
Separate the true practitioners from the theorists. Standard questions are insufficient. Use scenarios that test for practical, on-the-ground understanding.
- Scenario-Based: “Our product team wants to use a third-party LLM to analyze user-generated content. Walk me through the first five questions you would ask them.”
- Technical Acumen: “How would you explain the privacy risks of using vector embeddings for a semantic search feature to a junior engineer?”
- Risk Prioritization: “You’ve identified three moderate privacy risks in our upcoming release, but we only have engineering capacity to fix one before launch. How do you decide which one to address?”
The best candidates will not just recite GDPR articles. They will discuss trade-offs, ask insightful questions about your architecture, and propose concrete solutions that align with both compliance and the product roadmap.
Understanding Salaries and Certifications
Expertise in this field is in high demand, requiring a realistic budget. According to Data Protection Manager salary benchmarks on ZipRecruiter.com, the average salary in the US is around $97,145 a year. This figure can range from $66,000 for junior roles to $125,500 for senior professionals, with top experts commanding up to $163,000.
Certifications like CIPP/E (Certified Information Privacy Professional/Europe) or CIPM (Certified Information Privacy Manager) are useful indicators of foundational knowledge but are not a substitute for hands-on experience. A CIPP/E demonstrates knowledge of European law, while a CIPM shows understanding of privacy program management.
Treat certifications as proof of foundational knowledge. The true test is a candidate’s practical experience building and shipping products in a real-world technical environment.
Conclusion: Building Resilient Systems with Privacy at the Core
Hiring a Data Protection Manager is not just about compliance; it’s a strategic investment that improves product quality, customer trust, and long-term business resilience. It marks a shift from reactive box-ticking toward a culture of proactive data stewardship. This role makes a core philosophy practical: privacy is an architectural choice, not a feature you can bolt on later.
A DPM provides clear guardrails for engineering and product teams, enabling faster, more confident innovation. This proactive approach is essential for any organization building modern software.
A Data Protection Manager translates abstract legal requirements into concrete, maintainable engineering solutions. They don’t just put out fires; they build the operational foundation for trustworthy products and a durable competitive advantage.
The key takeaways are:
- Reduced Risk: Systematically de-risks product development by embedding compliance directly into the software development lifecycle.
- Faster Innovation: Empowers teams to build ambitious features with confidence, knowing privacy is handled correctly from the start.
- Stronger Competitive Advantage: Builds genuine customer trust and strengthens market position in a privacy-conscious world.
Practical Questions, Answered
This section provides direct, experience-based answers to common questions from CTOs, founders, and IT leaders about the Data Protection Manager role.
Do we need a full-time DPM or a consultant?
The answer depends on your company’s maturity and risk exposure.
For early-stage startups, a fractional or consultant DPM is often the most practical choice. It provides expert guidance to establish foundational policies and processes without the overhead of a full-time salary.
As a company scales—or if it operates in a high-risk sector like healthtech or fintech—a full-time, embedded Data Protection Manager becomes essential. They offer the continuous integration with development cycles, real-time risk assessment, and hands-on management of complex data flows that a consultant cannot provide.
What is the difference between a DPM and a DPO?
Although the acronyms are similar, the roles are distinct. The Data Protection Officer (DPO) is a formal, independent role required by GDPR under specific conditions. A DPO’s primary function is to monitor compliance and report to the highest level of management, free from operational influence.
In contrast, a DPM is an operational role focused on implementation. They work within your teams to translate legal requirements into technical controls and business processes. You hire a DPM to execute; you appoint a DPO for independent oversight.
How can we measure the ROI of a DPM?
Measuring the return on a DPM requires focusing on risk mitigation and operational efficiency rather than direct revenue. The value is found in the costs you avoid and the friction you remove.
The ROI of a Data Protection Manager isn’t on a sales report. It’s measured in the fines you don’t pay, the data breaches you prevent, and the velocity at which your teams can innovate without introducing compliance risks.
Key metrics to track include:
- A reduction in privacy-related incidents and support tickets.
- Faster time-to-market for new features due to early, integrated compliance reviews.
- Avoidance of regulatory fines and associated legal costs.
- Improvements in customer trust and brand reputation.
At Devisia, we build reliable digital products with a pragmatic approach that embeds security and privacy from day one. If you need a technical partner to turn your vision into maintainable, scalable software, visit us at https://www.devisia.pro.
