Using a generic confidentiality agreement template from the internet is a common shortcut for tech companies, but it’s a practice fraught with risk. Standard Non-Disclosure Agreements (NDAs) are often misaligned with the realities of agile development, API-driven architectures, and the large-scale data flows inherent in AI systems. For founders, CTOs, and compliance managers, this misalignment introduces significant and often overlooked liabilities.
Why Standard NDAs Fail in Modern Tech Stacks
Before adopting a one-size-fits-all NDA, it’s crucial to analyze the technical realities of your operations. A standard template often functions more as a procedural checkbox than a genuine safeguard for your core intellectual property (IP).
The fundamental problem is that these documents were conceived for a different business era—one characterized by physical assets and linear project management, not ephemeral cloud infrastructure and iterative software delivery. The reliance on vague definitions like “Confidential Information” is a critical failure point when your actual IP comprises source code, architectural diagrams, API keys, and proprietary training datasets.
The Disconnect with Agile Methodologies and API Economies
Agile development and the proliferation of third-party APIs create a dynamic environment where information flows constantly between internal teams, contractors, and external service providers. A static, boilerplate agreement cannot adequately govern these complex interactions.
- Agile Development: In an agile workflow, new features, code modifications, and architectural decisions are made in short, iterative cycles. A generic NDA lacks the specificity to protect these evolving assets, potentially leaving new IP exposed from one sprint to the next.
- API Integrations: Integrating a third-party service is not merely a data-sharing event; it creates a technical and operational dependency. A standard agreement rarely addresses the specific risks, such as data persistence on vendor servers, security vulnerabilities introduced by the integration, or liability allocation in the event of a breach in the third-party service.
For a technical partnership, a confidentiality agreement is not a legal formality; it is a foundational component of your risk management framework. It must be architected with the same diligence as your software.
The Amplified Risks in AI System Development
For companies building or utilizing AI systems, the stakes are significantly higher. Training a machine learning model often involves sharing vast quantities of sensitive or proprietary data with vendors, partners, or contractors. A standard confidentiality agreement template is dangerously insufficient for this purpose.
Consider a practical scenario: A SaaS company shares its curated customer interaction dataset with a third-party AI vendor to train a specialized large language model (LLM). The generic NDA they signed fails to explicitly prohibit the vendor from using this data to train their own foundational models. Months later, the vendor releases a new product feature that appears to incorporate insights derived from the SaaS company’s unique data.
The startup’s competitive advantage has effectively been absorbed into the vendor’s offering.
This type of IP leakage occurs because the agreement lacked precise clauses on:
- Data Usage Limitations: Explicitly restricting how the data can be used (e.g., solely for training a specific model instance for the client’s exclusive benefit).
- Model Ownership: Clearly defining ownership of the resulting trained model, its weights, and any derivative works.
- Data Destruction: Mandating the secure, verifiable deletion of all training data after project completion and requiring a certificate of destruction.
A robust agreement defines the operational and behavioral boundaries between parties—what they can and, more importantly, cannot do. This principle of setting clear expectations is also vital for internal teams, as detailed in our guide on creating a company code of conduct. Viewing the confidentiality agreement as a critical system component is the first step toward meaningful IP protection.
Core Components of a Tech-Focused Confidentiality Agreement
The following breakdown outlines the essential clauses for a confidentiality agreement template designed for software, AI, and digital product development. This is a foundational guide, not a substitute for qualified legal counsel, but it provides a robust starting point for technical leaders. Understanding the “why” behind these clauses enables more effective adaptation and negotiation.
Defining “Confidential Information”: The Heart of the Agreement
This is where most generic NDAs fail. If the definition of “Confidential Information” is ambiguous, the entire agreement lacks practical enforceability. The objective is to be specific enough to be defensible in a dispute while remaining broad enough to cover future innovations. A weak agreement uses vague terms like “business information.” A strong one, tailored for technology, explicitly enumerates its most critical assets.
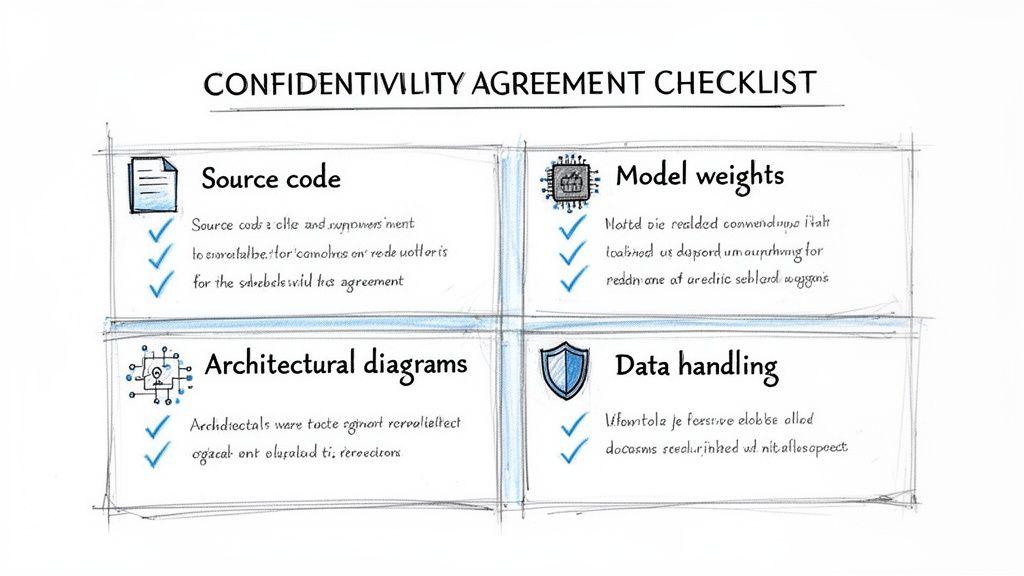
A robust template should include:
- Source Code and Object Code: Protects the literal implementation of your software.
- Architectural Diagrams and Technical Schematics: Safeguards your system blueprints and high-level designs.
- AI Model Weights, Parameters, and Training Data: Critical for any AI-driven company, protecting the output of expensive training processes.
- API Keys, Credentials, and Security Configurations: Prevents unauthorized access to your infrastructure and services.
- User Data and System-Generated Analytics: Protects the datasets you collect and process, which are often a core business asset.
- Undisclosed Product Roadmaps and Feature Specifications: Protects your strategic direction.
This level of detail eliminates ambiguity. When a contractor is bound by this agreement, they understand that “Confidential Information” refers directly to the database schema and the fine-tuned model they are working with.
Obligations of the Receiving Party
This section dictates what the recipient must do—and not do—with your information. It moves beyond a simple promise of secrecy to establish clear operational requirements.
Key obligations include:
- Standard of Care: The recipient must protect your information with the same level of security they apply to their own most sensitive data, and in no case less than a “reasonable” standard of care. This prevents a partner with lax security from using their own poor practices as an excuse.
- Purpose Limitation: Information may only be used for the specifically agreed-upon purpose (e.g., “to evaluate a potential API integration”). This clause prevents a vendor from repurposing your user data for their own analytics or model training.
- Access Control: The recipient must limit internal access to individuals with a strict “need-to-know” who are themselves bound by confidentiality obligations.
This clause transforms the agreement from a legal document into a set of operational instructions for secure data handling. It compels partners to consider their internal security posture and signals your company’s commitment to IP protection.
Exclusions from Confidential Information
No agreement can restrict information that is already in the public domain. This section is essential for fairness and legal enforceability, as courts are unlikely to uphold agreements that attempt to claim ownership of public knowledge.
Standard, necessary exclusions cover information that:
- Is or becomes publicly available through no fault of the recipient.
- Was already rightfully in the recipient’s possession before disclosure.
- Is independently developed by the recipient without reference to your confidential information.
- Is obtained from a third party who had the legal right to share it.
This section helps build trust by demonstrating that you are not overreaching, making the other party more likely to sign without protracted negotiation.
Term and Termination
The duration of confidentiality obligations is a critical consideration. While “perpetual” protection is appealing, it is often impractical and can be deemed unenforceable by courts. A more defensible strategy involves a fixed term for general information and a perpetual term for trade secrets.
A common and robust approach:
- Fixed Term (3-5 years): This is a standard duration for most business and technical information, whose commercial value often diminishes over time.
- Indefinite Term for Trade Secrets: The agreement should specify that information qualifying as a “trade secret” under applicable law (e.g., your core search algorithm) must be kept confidential for as long as it retains its status as a trade secret.
Crucially, the termination clause must stipulate that the duty of confidentiality survives the conclusion of the business relationship. The end of a project does not grant a contractor the right to publish your source code on GitHub; the obligation persists for the full specified term.
Remedies for Breach
This clause outlines the consequences of a leak. While monetary damages can be sought, they often fail to compensate for the harm caused by a stolen trade secret.
Therefore, your agreement must include a provision for injunctive relief. This gives you the right to seek an immediate court order to stop the unauthorized disclosure. The clause should explicitly state that a breach would cause “irreparable harm” for which monetary damages are an inadequate remedy. This language is critical, as it provides the legal basis for a court to grant an injunction.
By understanding these core components, you shift from passively using a confidentiality agreement template to actively architecting a defense for your company’s most valuable assets.
Adapting Your Agreement for Specific Tech Scenarios
A strong confidentiality agreement template is a starting point, not a final document. In technology, context is everything. Adapting your agreement for specific use cases is a critical risk management function that aligns legal protections with the technical realities of the engagement.
Treating every third-party interaction identically is a significant misstep. Onboarding a freelance developer to build a new feature carries different risks than sharing a proprietary dataset to train an AI model. Each scenario demands a tailored agreement to mitigate its unique IP and data security risks.
Engaging with Freelance Developers and Contractors
When hiring external developers, the primary risk is IP ownership. You are paying for the creation of an asset, and the company must own it outright. A standard NDA is insufficient; it requires specific IP assignment language.
This is achieved by adding a “Work for Hire” or “Assignment of Inventions” clause. This clause must state unambiguously that all code, designs, documentation, and other materials created by the contractor during the project are the exclusive property of your company. It should also include a waiver of any “moral rights” the developer might retain in their work.
Without an explicit assignment clause, a company could fund the development of its core product only to discover the contractor retains ownership of the code. This is a catastrophic failure that could prevent you from modifying, selling, or even using the software you paid for.
The agreement must also specify that upon termination, the contractor must return or securely destroy all company information, including wiping local copies of the codebase and revoking access to repositories and systems.
Integrating Third-Party APIs and Services
When integrating a vendor’s API, the risk profile shifts from IP creation to data security and liability. Your confidentiality agreement must govern the flow of data between your systems and the vendor’s, and define what they are permitted to do with it.
Key modifications should address:
- Data Usage and Persistence: Be explicit. How can the vendor use the data transmitted via their API? Can they store it? For how long? Are they permitted to use it for their own analytics or to train their models? Leave no room for interpretation.
- Liability and Security Breaches: The contract must define responsibility. If the vendor is breached and your customer data is exposed, who is liable? The agreement needs provisions for security standards, breach notification timelines, and indemnification.
- Downstream Dependencies: What if the API provider uses other services (sub-processors)? Your agreement should require disclosure of these dependencies and ensure that confidentiality and security obligations are passed down to their vendors.
Sharing Data for AI Model Training
This is one of the highest-risk scenarios, demanding the most rigorous customization. When you share a proprietary dataset for AI model training, you are handing over a core asset. A standard NDA is wholly inadequate.
First, the agreement must be precise about the scope of use. The data should only be used for the single, defined purpose of training a specific model for your benefit. It must explicitly forbid the recipient from using your data to train or improve any other models, particularly their own commercial products.
Second, you need clauses that provide oversight and control:
- Anonymization and Pseudonymization: If the data contains personal information, the agreement should mandate specific technical standards for data transformation before it is shared. This fits into a broader strategy of data protection and privacy by design.
- Audit Rights: This critical clause grants you the contractual power to inspect the recipient’s systems and processes to verify compliance with the agreement, particularly regarding data segregation and destruction.
- Data Destruction: Upon project completion, the agreement must require the secure and permanent deletion of your data from all systems. You should also require a “certificate of destruction” as verification.
The following table summarizes how key clauses should be adapted for different technical contexts.
Confidentiality Agreement Clause Variants for Technical Use Cases
| Scenario | Key Clause to Modify | Recommended Language/Focus | Primary Risk Mitigated |
|---|---|---|---|
| Freelance Developer | Intellectual Property | ”Assignment of Inventions”; “Work for Hire”. Explicitly state all work product is company property. | Loss of IP ownership for code you paid for. |
| Product Demo (Vendor) | Purpose & Permitted Use | ”Solely for evaluation purposes.” Prohibit reverse engineering, benchmarking, or non-evaluative use. | A prospect using your demo to build a competing feature. |
| API Integration | Data Usage & Liability | ”Data Processing Addendum (DPA)”. Define data use, storage limits, and liability for breaches. | Unauthorized data use by vendor; liability for their security failures. |
| AI Model Training | Scope of Use & Data Handling | ”Limited Use License”. Prohibit use for any other model/purpose. Mandate data segregation and destruction. | Your proprietary data being used to train a competitor’s AI. |
This table illustrates the core principle: your NDA’s language must mirror the specific risks of the technical collaboration. The stakes continue to rise as compliance demands grow. Globally, 2024 data privacy trends and predictions show increasing investment in privacy, making properly customized confidentiality agreements more critical than ever for every technical partnership.
Choosing Between Mutual and Unilateral Agreements
The decision between a mutual (bilateral) and unilateral (one-way) NDA is a strategic one that sets the tone for the engagement. The wrong choice can create unnecessary friction or, worse, leave technical assets unprotected. A unilateral agreement is designed for a one-way disclosure of information.
When a Unilateral Agreement is Appropriate
A unilateral agreement is the correct tool for specific, limited scenarios where one party is the primary discloser. It protects the discloser without placing unnecessary obligations on the recipient.
Common use cases include:
- Pitching to an Investor: You are disclosing your product roadmap and financials to a VC. They are evaluating you, not sharing their fund’s proprietary data in return.
- Demoing to a Prospective Client: You are presenting a software solution. Your team shares technical specifications, but the client is primarily observing.
- Initial Vendor Screening: You provide a high-level technical brief to a potential vendor to assess their capabilities. A deep, mutual exchange of proprietary data has not yet begun.
In these instances, a unilateral agreement is efficient. It protects your disclosure without creating a false expectation of a deep, two-way technical partnership.
The Case for Mutual Agreements in Technical Collaborations
Most substantive technical collaborations are not one-way disclosures. Once you begin co-developing a product, integrating systems, or engaging in deep technical discovery, both parties will inevitably share proprietary information.
In these situations, a mutual confidentiality agreement is non-negotiable.
A mutual agreement establishes a level playing field, acknowledging that both parties are bringing valuable assets to the table. It fosters a spirit of partnership. Attempting to impose a unilateral NDA when you know your partner will need to share their API documentation, security protocols, or performance benchmarks can start the relationship on an adversarial note.
A mutual agreement is the appropriate choice for:
- Joint Development Projects: Both engineering teams will exchange source code, architectural diagrams, and internal development practices.
- Deep API Integrations: You share your system’s internal logic, and your partner must share details of their API implementation, including potential security considerations.
- AI Model Collaboration: You provide a proprietary dataset, and the vendor may share the architecture of the model used to process it.
Choosing a mutual agreement is not just about fairness; it is pragmatic. It signals that you view the other party as a partner and acknowledges the reality of how modern software is built, fostering the trust required for a successful technical engagement.
Integrating Agreement Management into Your Tech Workflow
A signed confidentiality agreement template has no value if it’s archived in a forgotten inbox. The real challenge is operationalizing these agreements. For engineering and product teams, an ad-hoc approach to managing NDAs creates the very compliance gaps they are meant to prevent.
An effective agreement lifecycle management process should be clear and repeatable, covering initiation, execution, storage, and renewal. Relying on email chains and manual tracking is not a scalable or secure solution.
The diagram below illustrates the distinct information flows for unilateral and mutual agreements, a key consideration when designing a workflow.
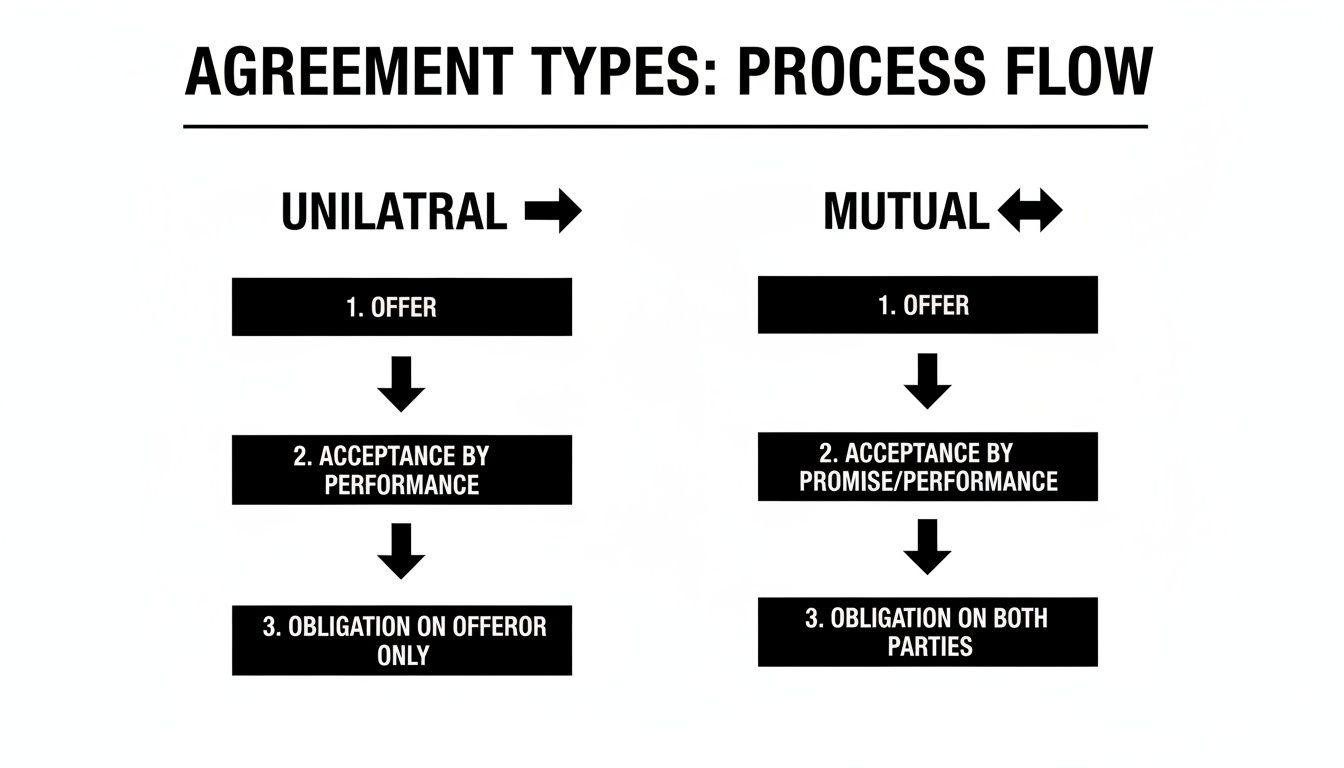
As shown, a mutual agreement necessitates a two-way exchange of protected data, demanding a more collaborative workflow from the outset.
Establishing a Centralized Workflow
A best practice is to build a workflow around a central repository integrated with a digital signature platform. This establishes a single source of truth, eliminating version control issues and lost documents.
A simple, effective process includes:
- Initiation: A designated person or automated trigger selects the correct agreement template (e.g., contractor vs. vendor) from a pre-approved library.
- Tracking: A digital signature tool provides a real-time dashboard of all pending agreements, eliminating the need for manual follow-up.
- Storage: Once executed, the final document is automatically filed in a secure, central location with a consistent naming convention.
- Renewal: For long-term relationships, automated reminders should be set for agreements nearing their expiration date. This is critical for vendors with ongoing access to sensitive systems.
Onboarding and Team Responsibilities
A workflow is only effective if the team adheres to it. During onboarding, engineers, product managers, and other personnel who handle sensitive data must be trained on the process. They need to understand which agreements govern which information and what their personal obligations are.
This extends beyond signing an employee NDA on day one. It requires ongoing operational discipline. A developer must know that the new API vendor they are integrating is covered by a mutual NDA with specific data handling clauses.
This operational rigor is increasingly critical with the rise of AI. Many organizations now add transparency clauses to contracts to specify how AI is used for data processing. As data leakage from generative AI becomes a top security concern, confidentiality templates must evolve to include terms on AI governance, human-in-the-loop controls, and system observability to manage risk effectively.
A disciplined approach transforms a static legal document into a dynamic component of your technical operations. For a closer look at related contracts, see our guide on the essentials of a Data Processing Agreement.
FAQs on Confidentiality Agreements in Tech
For CTOs, founders, and product leaders, questions about confidentiality agreements are practical and urgent. Here are clear answers to some of the most common issues.
What Makes a Confidentiality Agreement Legally Enforceable?
Enforceability hinges on several key factors. The most common point of failure is vagueness.
Your definition of “Confidential Information” must be specific. Simply stating “all business information” is insufficient. To be defensible, the agreement should explicitly list assets like source code, AI model weights, trade secrets, and specific client data.
The term of the agreement must be reasonable. A perpetual term for all information can be viewed by courts as an unfair restraint of trade. A standard duration of 3-5 years is typically enforceable for general business information, while true trade secrets can be protected for as long as they legally remain secret.
Finally, the agreement must specify remedies for a breach. Including a clause that a breach will cause “irreparable harm” and allows for injunctive relief is critical. This provides the legal standing to obtain a court order and stop a leak immediately, which is often more valuable than monetary damages.
How Should We Handle Pre-Existing Intellectual Property?
This is a critical detail that generic confidentiality agreement templates often miss. A robust agreement needs a “carve-out” or “background IP” clause.
This clause clarifies that any intellectual property a party owned before the agreement remains their own. When bringing a contractor in to work on an existing codebase, for example, it is wise to document this pre-existing IP.
This clause functions as a legal firewall. It prevents a partner or contractor from later claiming ownership of your foundational technology and makes it clear that no license to this background IP is granted unless explicitly stated in a separate agreement, such as a Statement of Work.
Can an NDA Protect a SaaS Product Idea?
An NDA protects the concrete expression of an idea, not the abstract concept itself. You cannot legally protect the “idea” for a new project management tool. What you can and must protect are the specific, tangible assets shared during its development.
A well-drafted confidentiality agreement will protect assets such as:
- Proprietary algorithms that power unique features.
- Detailed UI/UX wireframes and design mockups.
- Technical architecture diagrams.
- Go-to-market strategies and financial models.
The key is to define these tangible assets within the “Confidential Information” clause. An NDA will not stop a competitor from building a similar product, but it will legally prevent them from using your proprietary work to do so.
What Is the Difference Between an NDA and a Non-Compete Agreement?
These two legal instruments serve completely different functions.
A Confidentiality Agreement (NDA) is about secrecy. Its sole purpose is to prevent the unauthorized disclosure of proprietary information. It restricts the flow of information.
A Non-Compete Agreement, conversely, is about activity. It restricts a former employee or partner from working for a competitor or starting a competing business for a specified time and in a specific geographic area.
With non-compete agreements facing increasing legal scrutiny and bans in some jurisdictions, a meticulously drafted confidentiality agreement has become an even more critical tool for protecting your core assets: your data, code, and trade secrets.
At Devisia, we build reliable digital products and AI-enabled systems with a focus on pragmatic architecture and long-term maintainability. We help you turn your business vision into meaningful, secure software. Learn more about our approach.
