Article 30 of the GDPR is not a legal formality for the compliance department to handle. For software teams, it’s a technical mandate requiring a detailed logbook of your data processing activities—a living blueprint of how your software handles personal data. This logbook is officially known as the Record of Processing Activities (RoPA). Far from being a simple administrative task, maintaining it is a critical engineering challenge.
This guide reframes Article 30 GDPR compliance, not as a bureaucratic hurdle, but as an essential discipline for building robust, secure, and legally sound software systems.
The Problem: Why Article 30 Is a Critical Engineering Challenge
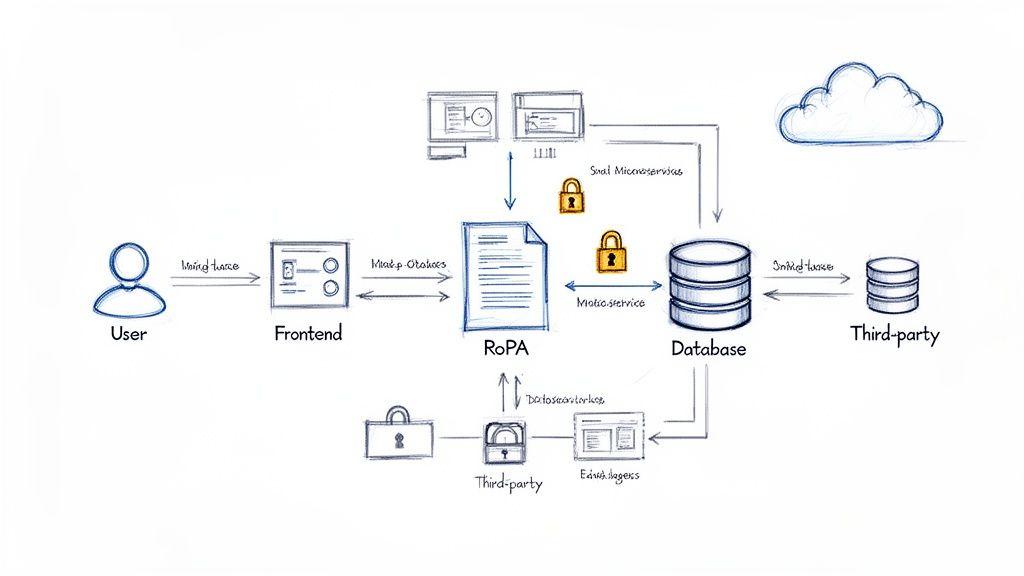
Many technical leaders treat Article 30 as a legal problem, delegating the RoPA to non-technical teams. This is a naive and high-risk mistake. Your RoPA is a direct reflection of your system’s architecture, data flows, and security posture. It forces a level of transparency that reveals whether you truly understand how data moves through your services, where it’s stored, or which third-party APIs have access to it.
For companies building SaaS platforms, custom software, or AI-driven systems, a poorly maintained RoPA signals deep operational and technical risks. It’s a leading indicator of a reactive, rather than proactive, approach to data governance.
The Consequences of a Superficial Approach
Failing to produce an accurate, up-to-date RoPA on demand can trigger severe penalties and intense regulatory scrutiny. This holds true even if your underlying data handling practices are otherwise compliant. The inability to demonstrate accountability is, itself, a significant violation.
The core problem: A RoPA is not a document you create once. It’s an output of a continuous process. Every new feature, microservice, or third-party integration that touches personal data must be reflected in your records.
This dynamic requirement places the responsibility squarely on engineering and product teams. The stakes for getting this wrong are high. Fines for non-compliance can be severe, but the greater risk is often the loss of customer trust and the operational chaos that follows a regulatory investigation. You can discover more insights about GDPR enforcement trends and learn from past cases.
This is why we maintain that privacy is an architectural choice, not a feature. The RoPA is the tangible evidence of that choice.
Defining Your Role: Controller vs. Processor
Under Article 30 of the GDPR, your documentation requirements hinge on a critical architectural question: are you a data controller or a data processor? This is a foundational determination. An incorrect classification invalidates your entire compliance effort from the start.
- A data controller is the entity that determines the “why” and “how” of data processing. Think of them as the system architect. If your SaaS company decides what personal data to collect from users and for what purpose, you are the controller.
- A data processor, in contrast, processes personal data on behalf of a controller. They are the builders executing the architect’s plans. For example, if your platform uses a third-party cloud provider (e.g., AWS, Azure) to store user data, that provider is your processor. They act only on your documented instructions.
The Controller’s RoPA Mandate
As a controller, you hold primary responsibility. Your RoPA must be a comprehensive map of your data ecosystem, proving you manage the entire processing lifecycle.
Your records must include:
- Name and contact details of your organization and Data Protection Officer (DPO), if applicable.
- Purposes of the processing: Be specific. “User authentication,” “subscription payment processing,” or “transactional email delivery.” Generic descriptions are a red flag.
- Categories of data subjects and personal data: Define whose data you process (e.g., “website visitors,” “subscribed users”) and what data you collect (e.g., “email addresses,” “IP addresses,” “payment history”).
- Categories of recipients: List any third parties with whom data is shared, including cloud hosting services, analytics platforms, and other sub-processors.
- International data transfers: Document any transfer of personal data outside the European Economic Area (EEA) and the legal safeguards in place, such as Standard Contractual Clauses (SCCs).
- Envisaged time limits for erasure: Specify your data retention policies. Vague statements like “as long as necessary” are non-compliant.
- A general description of technical and organisational security measures (TOMS): This includes outlining encryption standards, access control policies, and incident response protocols.
The Processor’s RoPA Mandate
If you act as a data processor—for instance, providing a white-label API to other businesses—your Article 30 obligations are more focused but equally important. You must meticulously document the activities you perform for each controller.
Your RoPA must contain:
- Name and contact details of your organization, each controller you act for, and their respective DPOs.
- Categories of processing carried out on behalf of each controller. This details the specific tasks you perform, such as “data storage,” “data aggregation,” or “report generation.”
- International data transfers and the safeguards used if you move data outside the EEA on a controller’s instruction.
- A general description of your technical and organisational security measures.
The controller’s RoPA answers “what and why,” while the processor’s RoPA answers “for whom and how.” This distinction is central to building accountable software systems.
The table below offers a direct comparison to help audit your existing records or build a compliant RoPA from scratch.
RoPA Requirements: Controller vs. Processor
| Requirement | Required for Controller | Required for Processor |
|---|---|---|
| Contact details of the organisation and DPO | ✔️ | ✔️ |
| Purposes of the processing | ✔️ | ❌ |
| Categories of data subjects and personal data | ✔️ | ❌ |
| Categories of recipients | ✔️ | ❌ |
| Details of the controller(s) served | ❌ | ✔️ |
| Categories of processing performed per controller | ❌ | ✔️ |
| International data transfers and safeguards | ✔️ | ✔️ |
| Envisaged data erasure timelines | ✔️ | ❌ |
| Description of technical and organisational security measures | ✔️ | ✔️ |
Solution: Building and Maintaining Your RoPA in an Agile Environment
A Record of Processing Activities (RoPA) is not a static document. In an agile environment with weekly or bi-weekly sprints, a static RoPA is a compliance failure waiting to happen. The solution is to integrate RoPA maintenance directly into your agile development lifecycle, treating it as a dynamic record that evolves alongside your software.
If your RoPA is disconnected from your engineering workflow, it will inevitably become outdated, inaccurate, and a liability during a regulatory audit.
1. Start with Comprehensive Data Discovery
Before documenting processing activities, you must know what they are. This requires a technical deep-dive to trace every piece of personal data across your technology stack. This is the most underestimated aspect of complying with Article 30 GDPR.
This process involves identifying and tracking data through:
- Applications and Microservices: Pinpoint every service that collects, transforms, or stores personal data.
- Databases and Data Stores: Map which tables, columns, or documents hold personal information, from primary SQL databases to caches and message queues.
- Third-Party APIs and Sub-processors: Document every external service that touches personal data, from payment gateways to analytics tools.
This is not a one-off audit; it must become a standard, repeatable part of your system design and review process.
2. Integrate RoPA Updates into Your SDLC
The most common failure point for a RoPA is reliance on manual, ad-hoc updates. The solution is to embed update triggers directly into existing engineering workflows. The principle is simple: if a code change touches personal data, it must also trigger a RoPA update.
Integrate this into your development process:
- Add a “Privacy Impact” section to user stories or pull request templates. Before merging, the developer must answer:
- Does this feature collect new categories of personal data?
- Does it introduce a new third-party sub-processor?
- Does it change how existing data is stored, used, or shared?
- Does it alter the data retention period?
- Flag for review. If the answer to any of these is “yes,” the ticket should be flagged for a RoPA review before deployment.
An outdated RoPA is more than a documentation error; it’s a misrepresentation of your data architecture. By embedding updates into your CI/CD pipeline, you transform the RoPA from a compliance burden into an accurate, living blueprint of your system.
3. Automate Where Possible, Review Constantly
While full automation is unrealistic, you can automate parts of the discovery and update process. Code scanners can detect PII in new database schemas, and infrastructure-as-code scripts can flag the addition of new data-handling services. These tools can generate draft RoPA updates for human review.
Automation must be paired with regular, human-led reviews synchronized with your development cycles.
- Establish a review cadence tied to sprints or major releases. A product owner or designated privacy champion should be responsible for verifying the RoPA’s accuracy at the end of each sprint or before a major release. This ensures the record remains a true reflection of the production environment.
This structured approach is crucial for complex systems like AI, where data flows can be less predictable. Our free AI Risk & Privacy Checklist can help assess and document potential risks tied to your machine learning models.
Common RoPA Mistakes That Attract Regulatory Scrutiny
A superficial Record of Processing Activities (RoPA) can be more dangerous than having none. To a regulator, a vague or incomplete document signals a fundamental misunderstanding of your Article 30 GDPR obligations and often invites a deeper investigation. It suggests your data governance is an afterthought, not a core architectural principle.
Vague Descriptions of Security Measures
One of the most frequent errors is providing generic descriptions of security. Stating “encryption is used” or “industry-standard security is in place” is meaningless. This lack of specificity suggests you either don’t know the details or are intentionally obscuring them.
A compliant RoPA demands precision. You must be prepared to specify details like:
- Encryption protocols for data in transit (e.g., TLS 1.3) and at rest (e.g., AES-256).
- Access control mechanisms, such as role-based access control (RBAC), multi-factor authentication (MFA), and the principle of least privilege.
- Pseudonymisation or anonymisation techniques used to reduce data risk.
- Logging and monitoring procedures for detecting and responding to security incidents.
Without this level of detail, your RoPA fails to provide the required assurance.
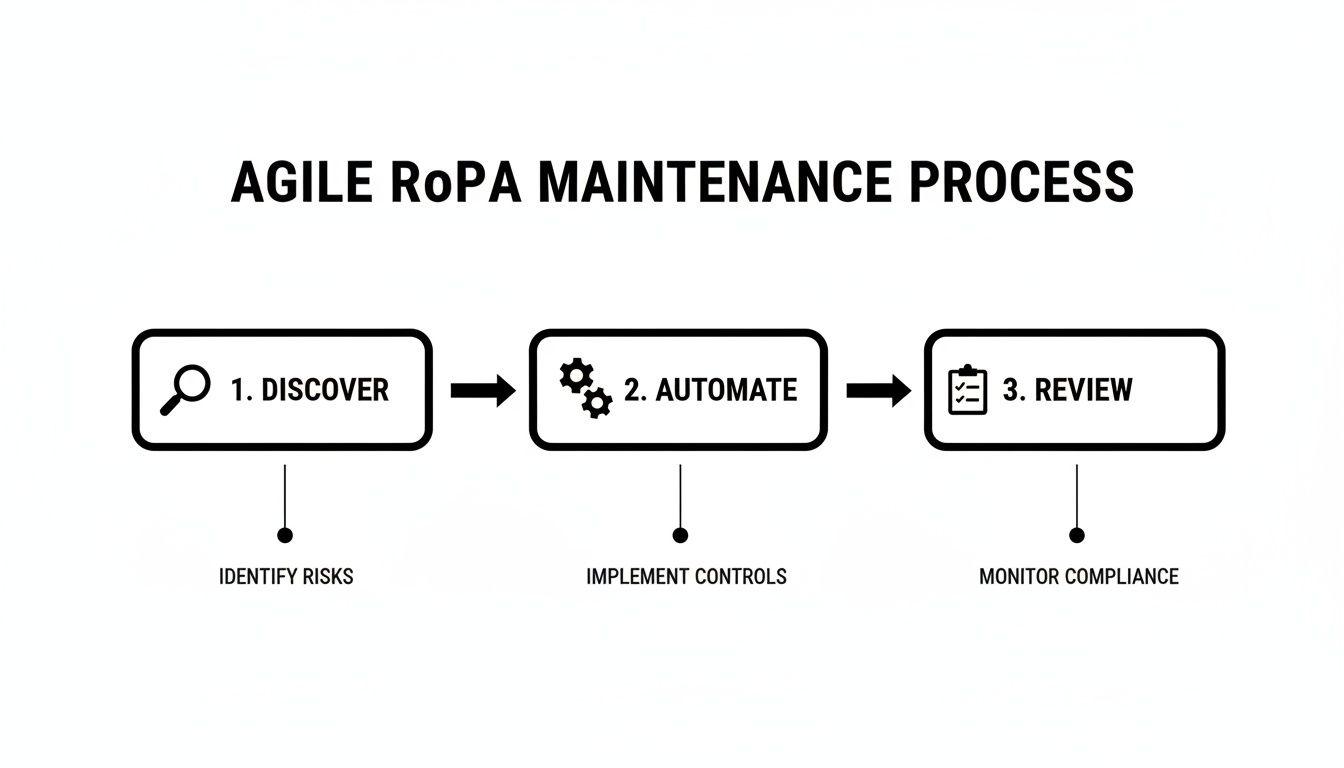
This cyclical process—Discover, Automate, and Review—ensures your RoPA remains a living document that accurately reflects your current architecture and security controls.
Inaccurate or Missing Data Flow Mapping
Another critical failure is neglecting to accurately map data flows to sub-processors and third-party services. A modern tech stack can involve dozens of SaaS applications, and each one that processes personal data must be documented.
Your RoPA must be an honest representation of every system that processes personal data on your behalf. Omitting a key service, whether a CRM, analytics platform, or cloud database, renders your entire record inaccurate and untrustworthy.
This mistake is a classic symptom of a compliance process that is disconnected from the engineering lifecycle.
Failing to Document a Lawful Basis
Every processing activity in your RoPA must be justified by one of the six lawful bases defined in the GDPR (e.g., consent, contract, legitimate interest). It’s not enough to list what you do with data; you must document why you are legally permitted to do it.
Common mistakes include:
- Omitting the lawful basis entirely.
- Assigning an incorrect basis, like claiming “legitimate interest” for an activity that requires explicit “consent.”
- Failing to document the specific legitimate interest when that basis is used.
A missing or incorrect lawful basis is a direct violation of core GDPR principles and an immediate red flag for any auditor. It demonstrates a lack of foundational understanding of data protection law and undermines any claim of being audit-ready and compliant by design.
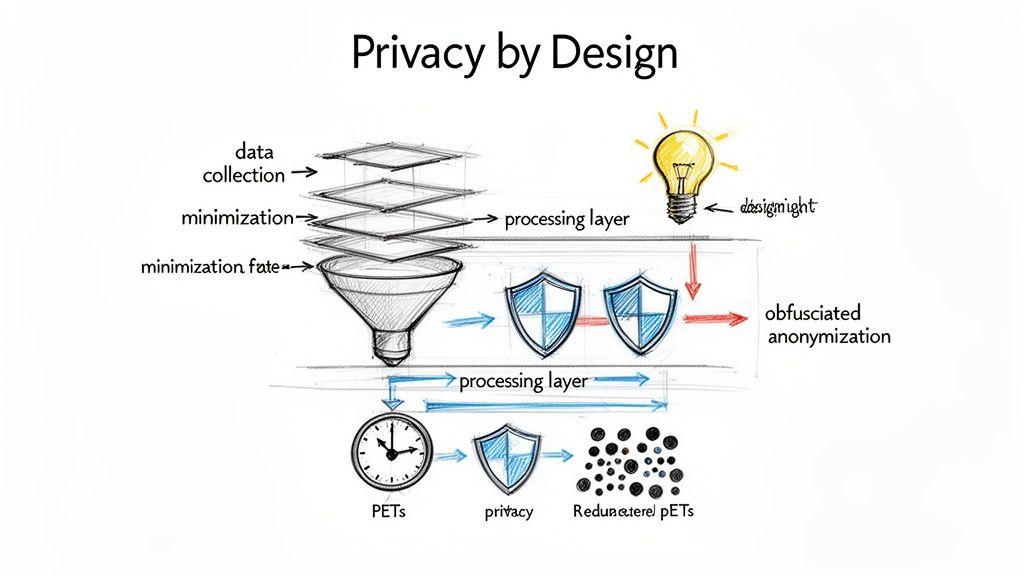
Using Your RoPA to Drive Privacy by Design
Most teams view the RoPA as a compliance chore. This perspective misses its strategic value. A well-maintained RoPA is one of the most powerful tools an engineering team has for implementing Privacy by Design.
Instead of a static report, your RoPA becomes a dynamic blueprint for building more secure, efficient, and trustworthy systems.
From Data Mapping to Architectural Insights
The data mapping required for Article 30 GDPR is effectively an architectural review. Tracing data from user input through microservices, databases, and third-party APIs inevitably uncovers insights that extend beyond compliance.
This process highlights systemic issues:
- Redundant Data Collection: You might discover that three different microservices collect the same user preference data, creating unnecessary storage costs and expanding your risk surface.
- Insecure Data Pathways: Mapping data flows can reveal vulnerabilities, like an internal service sending personal data over an unencrypted channel or a legacy integration using outdated security protocols.
- Opportunities for Data Minimisation: The RoPA forces you to document the purpose for every piece of personal data. This often reveals data that is collected but never used, providing a clear business case for its removal.
Informing Technical Decisions and Reducing Risk
A living RoPA becomes a central source of truth for key engineering decisions, providing objective evidence to justify privacy-enhancing choices.
- Implementing Privacy-Enhancing Technologies (PETs): When your RoPA documents sensitive data processing, it builds a strong case for implementing PETs like pseudonymisation for analytics or differential privacy for research.
- Justifying Data Retention Policies: The RoPA requires you to specify erasure timelines, forcing concrete technical discussions that lead to automated scripts that purge data once its purpose is fulfilled.
- Triggering Data Protection Impact Assessments (DPIAs): The RoPA acts as an early warning system. When a new feature proposes processing data in a novel or high-risk way (e.g., with AI), the act of updating the RoPA triggers the need for a DPIA, ensuring risks are assessed before code is written.
An active RoPA is a proactive tool for shaping what you build next. It provides the data-driven foundation for a culture where every engineer understands the privacy implications of their code.
Ultimately, integrating the RoPA into your architectural process does more than satisfy Article 30 GDPR. It leads to cleaner, more efficient systems that are easier to maintain and secure.
Actionable Takeaways for Engineering and Product Leaders
Complying with Article 30 is a discipline of sound engineering and risk management. For technical leaders, the Record of Processing Activities (RoPA) is an essential architectural artifact—a map revealing the health, security, and integrity of your software systems.
A well-maintained RoPA is evidence of control. It demonstrates a practical understanding of how personal data flows through your products. This clarity is not just for regulators; it’s for your team. It drives better technical decisions, reduces architectural debt, and builds the user trust that is critical to commercial success. Ignoring it is not just a compliance risk—it’s a significant engineering blind spot.
Key Takeaways
Mastering Article 30 GDPR isn’t about avoiding fines. It’s about instilling a discipline of transparency and accountability that leads to fundamentally better and more secure software.
Here are the key actions to focus on:
- Treat the RoPA as a living architectural document. Integrate RoPA updates into your Software Development Lifecycle (SDLC). A change to a data model, the addition of a third-party API, or a new data-collecting feature must trigger a RoPA update. Make it part of your “definition of done.”
- Use the RoPA for architectural reviews. Leverage your data map to identify and eliminate redundant data collection, find insecure data pathways, and enforce data minimization. A clean RoPA often correlates with a cleaner, more efficient system architecture.
- Demand technical specificity in all documentation. Vague descriptions like “standard security measures” are unacceptable red flags. Ensure your RoPA contains precise details reflecting your actual implementation—from specific encryption protocols to exact data retention schedules.
- Clarify roles: controller vs. processor. Ensure your team understands whether they are acting as a data controller or a processor for a given activity. This distinction defines your legal obligations under Article 30 and is the foundation of a defensible compliance posture.
Frequently Asked Questions About Article 30
Here are answers to common questions that software and IT teams encounter when implementing Article 30.
Does the 250-employee exemption apply to tech companies?
Almost never. Article 30 includes an exemption for organizations with fewer than 250 employees, but its exceptions render it irrelevant for nearly every software company.
The exemption is void if your data processing is:
- Not occasional (i.e., it’s a core business activity).
- Likely to pose a risk to the rights and freedoms of individuals.
- Involves special categories of data (e.g., health information).
Since nearly all SaaS platforms and software products involve continuous user data processing, they fall into the first exception. If you are building and operating software, assume you must maintain a RoPA, regardless of company size.
Is a spreadsheet sufficient for our RoPA?
A spreadsheet can be a starting point for a very simple business, but it does not scale with modern software complexity. It quickly becomes difficult to maintain, version, and audit, especially in agile teams where the architecture is constantly evolving.
While the GDPR permits records in electronic formats, a spreadsheet often becomes an outdated liability. Dedicated privacy management platforms or well-integrated documentation tools (like Confluence with strict templates and review processes) are far more effective for creating a living document that engineering, product, and legal teams can trust.
How often must we update our RoPA?
Your RoPA must be a living document. It is not a report you file quarterly. It should reflect your processing activities in near real-time.
Any significant change—such as integrating a new third-party API, launching a feature that collects new data, or changing a data retention policy—requires an immediate update. The best practice is to build RoPA updates into your software development lifecycle and schedule formal reviews at least quarterly to ensure nothing has been missed.
At Devisia, we believe privacy is an architectural choice, not just a compliance feature. We build robust, maintainable, and audit-ready software systems designed for the real world. Learn how we can help you turn your business vision into a reliable digital product at https://www.devisia.pro.
_Article created using Outrank
